What to do if you clicked a phishing link
Phishing is a type of cyberattack in which criminals pose as legitimate organizations or individuals to trick people into revealing sensitive information, such as passwords or credit card details. It often involves deceptive emails, messages, or fake websites that are designed to look authentic and trick victims into providing personal information.
Clicking a phishing link can be alarming, but there are several important steps you can take to protect your information and secure your devices. If you're asking yourself, "I clicked a phishing link—what now?" this guide will provide the answers you need. Whether it's on a desktop or mobile device, knowing how to respond promptly can make all the difference.
Why clicking phishing links can be dangerous
What happens if you click a phishing link? The consequences can be serious because these links often lead to malicious websites designed to steal personal information, such as passwords, credit card information, or other sensitive data. These sites can also install malware on your device, giving attackers access to your files, contacts, and even your camera or microphone. In some cases, the malware can spread throughout your network, compromising other devices and systems and potentially causing widespread damage. In addition, phishing links may exploit vulnerabilities in software or applications, putting your data at even greater risk.
How to recognize phishing tactics
Recognizing phishing tactics is key to protecting your personal information and avoiding cyber threats. Phishing schemes often use emotional manipulation, urgency, and visual deception to get you to click on malicious links or share sensitive information. Here's how to spot the warning signs:
-
Urgent or threatening language
Phishing messages often create a sense of urgency or fear, pressuring you to act quickly. Common phrases include "Your account is being suspended," "Immediate action is required," or "Suspicious activity has been detected on your account. These tactics are designed to make you panic and click before you think. Legitimate companies rarely use such high-pressure language, especially without prior notice. -
Suspicious links and URLs
Always hover over links in emails or messages before clicking to check the URL. Phishing links are often designed to look like authentic websites, but may have slight misspellings, extra characters, or unusual domain endings. For example, a legitimate website might be "bank.com", while a phishing site might be "bank-secure-login.com". If anything about the link looks strange or unexpected, avoid clicking it. -
Unexpected attachments or links
Phishing emails often contain unexpected attachments or links with enticing names to get you to click. Attachments may be labeled as "invoice," "order confirmation," or "important update," but they may contain malware. Be wary of attachments from unknown senders, especially if the email seems out of context or unexpected. If you receive a suspicious attachment, do not open it and confirm its authenticity directly with the sender. -
Incorrect or strange email addresses
Phishing emails often come from addresses that look similar to legitimate company emails, but are slightly different. For example, an email from "support@secure-bank.com" instead of "support@bank.com" could be a phishing attempt. Check the sender's email address carefully. If it doesn't match the company's official domain or seems odd in any way, it's probably fraudulent. -
Poor grammar and spelling
Although not always present, many phishing messages contain misspellings, poor grammar, or awkward wording. Professional companies make sure their communications are polished, so messages with numerous errors can be a red flag. If an email from what appears to be a bank or large company is riddled with typos, it's probably a phishing attempt. -
Requests for sensitive information
Legitimate companies rarely ask for sensitive information (such as passwords, credit card numbers, or social security numbers) via email or text. If a message requests this information, it's almost certainly a phishing attempt. Be especially cautious if the email suggests that you must provide information immediately to avoid negative consequences. -
Too-good-to-be-true offers
Messages promising large sums of money, prizes, or exclusive deals are often phishing scams. These messages are designed to play on emotions and excitement, enticing you to click links or provide details to claim your prize. If the offer seems too good to be true, it probably is. Always verify these offers through official channels instead of clicking the links provided.
How to know if you have clicked a phishing link
Unfortunately, prevention doesn't always work, so it's crucial to know how to identify when you've landed on a phishing site. Recognizing key warning signs — such as missing SSL certificates, missing contact information, poor design, or urgent pop-ups — can help you act quickly before irreversible damage is done.
-
No SSL certificate: Secure sites start with "https://" and have a lock icon in the browser address bar to indicate an encrypted connection. If a site lacks this, especially one that asks for personal information, it may not be secure.
-
Few or no additional pages: Phishing sites often have only one or very few pages, focused mostly on collecting user information. Various links on such websites often lead back to the main page. This contrasts with legitimate websites, which are usually much more comprehensive.
-
Poor content quality: Phishing sites often have misspellings, poor design, strange fonts, or broken images, as scammers prioritize speed over quality.
-
Missing contact information: Legitimate sites provide ways to contact them, such as email, phone, or address information. Missing these details, along with a lack of a clear and accessible privacy policy, could be a sign of phishing.
-
Requests for personal information: Phishing sites often aggressively ask for sensitive information. Trustworthy sites will rarely ask for personal information without your permission.
-
Urgent pop-ups: Phishing sites use pop-ups to create urgency by asking you to take quick action, such as clicking links or providing information. Trustworthy sites generally avoid these tactics.
What to do when you click a suspicious link on your phone or computer? The steps below outline exactly what to do to limit any harm and secure your information.
Immediate steps to take if you clicked a phishing link
Phishing attacks are a serious threat to your personal information and security. If you accidentally clicked a spam link, it's important to act quickly to minimize the potential damage. Here's a guide on what to do:
Avoid entering more information
If you're prompted to enter personal or financial information after clicking the phishing link, don't provide it. Phishing sites are designed to look legitimate, but any information you enter can be collected by the attacker.
Secure your device
-
Run an antivirus or anti-malware scan
Your next step should be to run a full scan of your device with antivirus or antimalware software. These tools will check for any malicious software (malware) that may have been installed when you clicked the link. Many modern cybersecurity tools can detect and quarantine common phishing-related malware to help protect your device and data. -
Update passwords
Immediately change passwords for sensitive accounts, such as your email, bank accounts, or online shopping sites. Make sure these new passwords are unique, strong, and difficult to guess. Avoid using the same password for multiple accounts, as this increases your risk if one account is compromised. -
Enable two-factor authentication (2FA)
For an extra layer of security, enable two-factor authentication (2FA) for your critical accounts. This extra step requires you to enter a code sent to your phone or email, or use an authentication application. Even if an attacker gets your password, 2FA can prevent them from logging in without the second verification step.
Monitor for suspicious activity
Once you've secured your device, it's important to monitor for any unusual behavior related to your accounts and finances.
-
Review financial statements
Carefully review your bank and credit card statements. Look for any unauthorized transactions or charges that weren't made by you. If you find any, report them to your bank immediately and dispute the charges. -
Review account activity
Check your email, social media, and other online accounts for suspicious activity. Look for emails you didn't send, changes to account settings, or unfamiliar devices accessing your accounts. If you notice anything unusual, update your security settings and consider resetting your password. -
Consider a credit freeze (if applicable)
If you provided financial information, consider freezing your credit to prevent identity theft. This will prevent anyone from opening new lines of credit in your name. If you're unsure whether this step is necessary, contact a credit bureau or cybersecurity professional for advice.
Report the phishing incident
It's important to report phishing attempts to help authorities track and prevent cybercrime.
-
Notify your bank or relevant companies
If your personal or financial information has been compromised, notify your bank, credit card companies, or other relevant institutions immediately. They can monitor your accounts for fraudulent activity and take additional security measures. -
Report to anti-phishing authorities
Report the phishing attempt to organizations that specialize in combating cybercrime, such as the Anti-Phishing Working Group (APWG). Reporting will help raise awareness and may help track down the attackers. -
Alert contacts
If the phishing link came via email or messaging platforms, notify your contacts of the attack. In some cases, the phishing attempt may have spread to your friends or colleagues through your account, so it's important to warn them so they don't fall for the same scam.
How to prevent future incidents
Taking proactive steps to secure your online presence can help you avoid future phishing attacks. Two of the most effective ways to prevent these incidents are to use reliable security software and to regularly update your account passwords with additional security measures.
Use security software
Security software is your first line of defense against phishing scams and other cyber threats. A good security suite should include features that help you browse safely, block malicious links, and protect your devices from malware. Here's what to look for:
-
Safe browsing and anti-phishing protection: Many security programs include features that block phishing websites and warn you about suspicious links. These tools can alert you when you're about to enter a site known for phishing or other scams, helping you avoid malicious clicks before they cause harm.
-
Automatic scanning and malware protection: Comprehensive security software regularly scans your device for malware and removes any threats it finds. This prevents spyware and other malicious programs from collecting sensitive information.
-
Browser extensions for safe browsing: Some security suites include browser extensions that provide additional security while you browse. These extensions can detect phishing attempts on the fly, giving you an extra layer of protection.
Update passwords and security regularly
Strong, unique passwords combined with additional security measures provide critical protection for your online accounts. Here's how to effectively secure your accounts:
-
Use strong, unique passwords: Avoid using the same password for multiple accounts, as this increases your risk if one password is compromised. Strong passwords should be at least 12 characters long and contain a mix of letters, numbers, and special characters. Consider using a password manager like LastPass or Dashlane to generate and securely store complex passwords.
-
Enable two-factor authentication (2FA): 2FA is a powerful tool that adds an extra layer of security by requiring you to enter a code, usually sent to your phone or generated by an app, in addition to your password. Even if an attacker gets your password, they won't be able to access your account without this second step.
-
Update your passwords regularly: Regularly updating your passwords can make it harder for hackers to gain long-term access to your accounts. Set a reminder to change your most sensitive passwords, such as banking and email accounts, every few months for added security.
Our solution: AdGuard
AdGuard products offer comprehensive protection that can address multiple risks after clicking a phishing link. Here's how each product can help:
AdGuard Temp Mail
AdGuard Temp Mail is a particularly useful tool for avoiding phishing risks by providing disposable email addresses. When you need to sign up for services or try online offers, using a temporary email address keeps your primary inbox secure and prevents attackers from collecting personal information. Temp Mail can be critical in protecting your primary email from potential phishing attempts, reducing the likelihood of exposure to future attacks.
AdGuard Ad Blocker
AdGuard Ad Blocker removes intrusive ads and blocks malicious links on websites, helping to prevent further interaction with phishing schemes. By filtering content, it also reduces the risk of malvertising (i.e. ads that contain hidden malware). The goal of malvertising is to trick you into following a link to a malicious website or to inadvertently install harmful software. This proactive filtering can stop additional attempts by phishing actors to engage with compromised users.
AdGuard DNS
AdGuard DNS acts as a secure intermediary by blocking access to known phishing and malicious websites at the network level. After clicking a phishing link, AdGuard DNS can prevent your device from connecting to fraudulent sites by redirecting requests away from these harmful URLs. This DNS service not only blocks known phishing domains, but also filters out other potentially dangerous sites, creating a safer browsing experience.
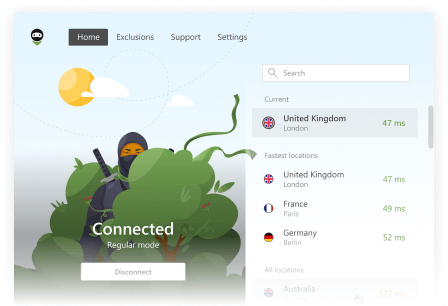
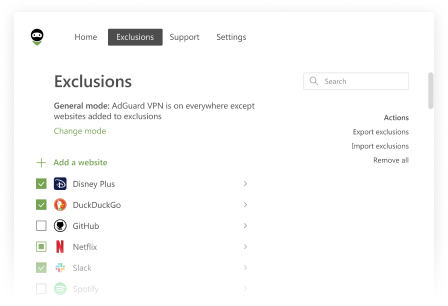
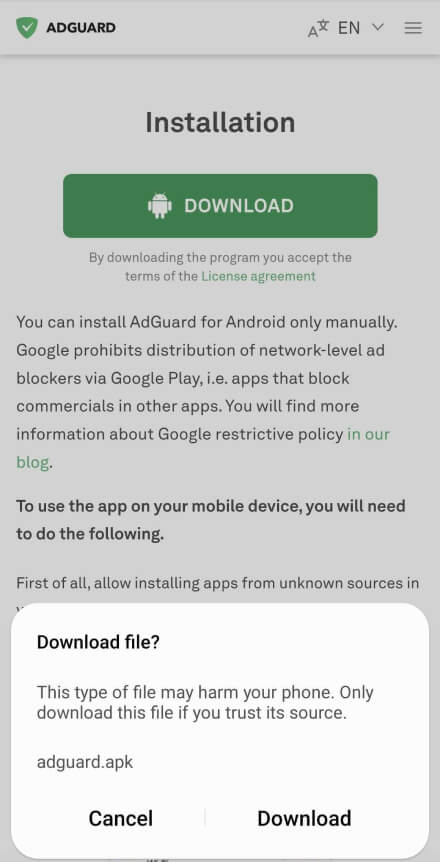
AdGuard VPN
Using AdGuard VPN increases your privacy and limits an attacker's ability to gather information about your device or browsing patterns. The VPN masks your real IP address and encrypts your Internet traffic, making it difficult for attackers to target you with further phishing attempts. AdGuard VPN is especially useful if you accidentally click a link while on a public Wi-Fi network, as it encrypts data that would otherwise be vulnerable to eavesdropping.