AdGuard Home 0.107.76


更新日期:2026年5月21日
都说「没坏就别去动它」。但如果它真的坏了呢?比如我们在上次更新中不小心弄乱的缓存?针对这种情况,我们有热修复补丁!请务必安装今天的更新,来修复 AdGuard Home 上的缓存。
AdGuard Home 0.107.75


更新日期:2026年5月19日
🔒 这次更新给 AdGuard Home 来了一次硬核的安全升级。用户可以理解为:把锁拧紧,再把门挨个检查一遍。
我们修复了一个影响 DNS‑over‑QUIC 和 DNS‑over‑HTTPS 的严重漏洞,该漏洞曾可能危及用户的 DNS 隐私。现在这个缺口已经堵上,个人加密流量又可以安心地穿过那层结实的隧道了。
此外,我们把 Go 语言版本也更新到了最新,顺手清理了其库文件里已知的安全隐患。
AdGuard Home 0.107.74


更新日期:2026年4月16日
跟生活中的所有事情一样,最好的东西之所以最好,恰恰是因为它们与众不同。没有平凡,何来非凡?
说了这么多,其实就想说:这次 AdGuard Home 的更新有点“无聊”,主要是修复错误和安全更新。这样下次我们再添新功能的时候,才会让人觉得新鲜又刺激!
AdGuard Home 0.107.73


更新日期:2026年3月10日
我们发布此热修复,用于解决近日发现的一个严重漏洞。该错误导致用户在未提供有效凭证的情况下绕过身份验证,完全控制 AdGuard Home。我们强烈建议用户立即更新 AdGuard Home 客户端。
AdGuard Home 0.107.72


更新日期:2026年2月25日
新年的首次发布总是意义非凡,它为未来数月定下基调。📆
我们在 2026 年的开篇之作或许不算光鲜亮丽,却是一套扎实的组合拳:全新的 TLS 证书更新机制、若干其他细微新功能、部分配置调整、几项关键修复,以及常规的安全更新。
敬请期待更多精彩改进!
AdGuard Home 0.107.69


更新日期:2025年10月30日
AdGuard Home v0.107.69 现已发布。此版本虽未新增功能,但重点修复了两项潜藏的系统漏洞,现可以确保系统运行更为稳定顺畅。
AdGuard Home 0.107.68


更新日期:2025年10月23日
首先照例说明基础改进:我们实施了多项安全更新,而本次版本甚至无需进行错误修复。不过,让我们聚焦核心升级:DNS 重写规则一键开关功能正式上线。
该功能是早期用户强烈期待的特性之一,我们很高兴终于能将其实现。现在,用户既可批量启用/停用 DNS 重写规则,也能针对单条规则进行独立控制,无论是通过编辑 YAML 配置文件还是在界面中操作皆可实现。
AdGuard Home 0.107.66


更新日期:2025年9月15日
您可能拥有世界上最好的软件,但如果人们无法用上它,那就形同虚设。正因如此,在本次更新中,我们优先修复了一些身份验证错误,以确保用户始终能顺利登录并充分利用 AdGuard Home 的全部功能。再加上常规的安全更新和少量其他改动,v0.107.66 版本现已到来!
AdGuard Home 0.107.64


更新日期:2025年7月29日
和「先有鸡还是先有蛋」不同,漏洞总是比修复更早出现。不过,好在这次更新把它们都解决了!🥚🐔
这次我们修复了各种类型的 Bug 错误,包括安全漏洞错误、缓存响应 TTL 问题,以及 DNSCrypt 证书问题。立即升级 AdGuard Home 新版本!
AdGuard Home 0.107.63


更新日期:2025年6月30日
问题未必都出在大功能上。有时只需若干修复与优化,即可全面提升系统稳定性 🔩
AdGuard Home 0.107.62


更新日期:2025年5月29日
许多厂商都标榜「客户至上」(client-oriented),而 AdGuard Home 则真正实现了「
$client为本」。本次更新我们重点修复了包含 client 修饰符规则失效的问题。👥同时照例通过升级 Go 版本修复了若干漏洞,进一步强化了 AdGuard Home 的安全防护。
AdGuard Home 0.107.60


更新日期:2025年4月17日
如果您正在仔细阅读这些更新说明,那您一定是 AdGuard Home 的资深用户了,毕竟这次更新没有炫酷的新功能,主要是修复了Go 语言的漏洞、优化了 UI 和 Docker 支持,以及进行了一些错误修正。
AdGuard Home 0.107.59


更新日期:2025年3月21日
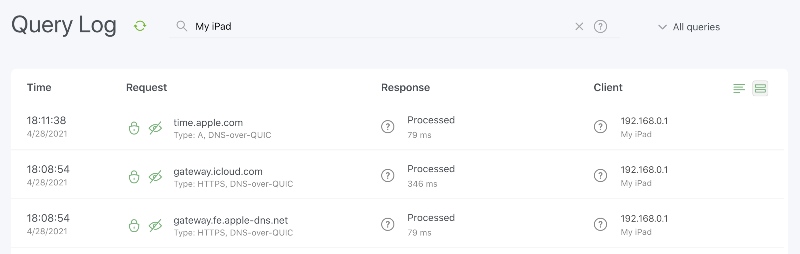
此次热修复解决了上一个更新引入的错误,即用户无法在「查询日志」的搜索框中输入任何内容的问题。我们还修复了与客户端修饰符功能有关的问题。
致谢
特别感谢我们的社区管理员团队 @AdguardTeam/community-moderators,以及所有提交和检查问题、添加翻译并帮助我们测试此版本的用户!
AdGuard Home 0.107.58


更新日期:2025年3月20日
这次更新中,我们修复了不少漏洞,同时还加入了一个实用的功能,值得为大家详细介绍一下。
全新升级的 DNS 查询检查工具
如果您非常注重隐私保护和广告拦截,手里肯定已经积累了一大堆规则,无论是各类过滤列表,还是自定义规则。每次调整规则时,您有没有想过如何快速检查某个 DNS 查询是否会被拦截?现在,我们对 DNS 查询检查工具进行了优化,新增了 DNS 记录类型和特定客户端的过滤功能。用户可以通过 IP 地址或 ClientID 进行查询,清楚看到哪些规则会生效。好消息是,用户还能直接解封某个域名,操作更便捷!
AdGuard Home 0.107.57


更新日期:2025年2月21日
2025年才刚开始,但有些人已经需要休息一下了 🕙 说到“休息“,在新版本中,我们新增了在 Web UI 中设置上游超时时间的功能,同时还修复了一些错误并提升了安全水平。
AdGuard Home 0.107.56


更新日期:2025年1月24日
在新版本中,我们修复了一些错误,增加了新的应用程序接口(API),并更新了 Go 版本以弥补一些漏洞。
AdGuard Home 0.107.55


更新日期:2024年12月12日
是时候发布新版本了!我们建议所有 Windows 用户关注此次更新,因为我们修复了一个影响部分 Windows 用户的问题。至于其他 AdGuard Home 用户,我们还更新了 Go 版本以加强安全性,并修复了几个漏洞问题。
AdGuard Home 0.107.54


更新日期:2024年11月6日
Windows 用户会对本次 AdGuard Home 更新特别感兴趣。我们针对 Windows 进行了必要的安全改进。不过,AdGuard Home 更新能满足每个人的需求,而不仅仅是 Windows 用户。现在,过滤器性能更好。当然,我们还修复了一些其他错误。
AdGuard Home 0.107.53


更新日期:2024年10月3日
我们将 AdGuard Home 的更新推迟了几个月。当然,我们有充分的理由:我们在社区成员的帮助下(非常感谢大家!🙏),发现了两个错误,因此,我们一直在努力修复它们。测试解决方案的时间比预期要长一些,但最终,我们相信质量胜于速度。
本次更新不仅仅是修补漏洞和修复错误,我们还做了一些改进。例如,我们在「安全搜索」功能中添加了对 64 位 RISC-V 架构和 Ecosia 搜索引擎的支持。完整的更新日志如下。
AdGuard Home 0.107.52


更新日期:2024年7月4日
在此更新中,我们修复了许多错误,将前端迁移到了 TypeScript,并更新了前端库,以提高开发质量和用户体验。
AdGuard Home 0.107.51


更新日期:2024年6月6日
这次更新我们修复了错误并改进了安全。我们在开发即将发布版本的新功能。
AdGuard Home 0.107.50


更新日期:2024年5月24日
我们发布此修复程序的原因是,上次 AdGuard Home 更新后,一些用户无法启动 AdGuard Home。
AdGuard Home 0.107.49


更新日期:2024年5月21日
在这次补丁中,我们修复了一些错误,让 AdGuard Home 运行更流畅。
AdGuard Home 0.107.48


更新日期:2024年4月5日
上次更新后,被禁止的用户可以使用加密协议执行 DNS 查询。 这是一个错误,我们已修复了它。
我们对这一疏忽表示诚挚的歉意。 我们将尽一切努力确保今后不再发生此类错误。
AdGuard Home 0.107.47


更新日期:2024年4月4日
这是另一个与安全相关的错误修复更新。我们修复了时区选择问题和其他一些恼人的错误。
AdGuard Home 0.107.46


更新日期:2024年3月20日
在更新版本中,我们修复错误并改进性能 🔧
AdGuard Home 0.107.45


更新日期:2024年3月7日
这是一个小更新,包含安全改进、错误修复和新功能。
AdGuard Home 0.107.44


更新日期:2024年2月6日
最大的变化往往是最不被人所注意到的 —— 我们今天的更新就是如此。我们为齿轮“上油“了,进行了重要改进和各种错误修复 🔧。
AdGuard Home 0.107.43


更新日期:2023年12月11日
Everybody needs something to keep themselves warm during the cold winter days ❄️. Many people opt for hot coffee ☕ or hot chocolate, but we at AdGuard prefer hotfixes 🔥.
AdGuard Home 0.107.42


更新日期:2023年12月7日
As the winter holidays approach, many of us begin to think about what gifts we will give and receive 🎁. With AdGuard, the holidays come early: we decided not to wait too long and present you with this new version of AdGuard Home today!
Among the long-awaited features in this release are the option to enable caching for persistent clients with custom DNS upstream configuration and the option to disable plain DNS for better security.
AdGuard Home 0.107.41


更新日期:2023年11月13日
四季交替,但不同的 Bug 却总出现 📆 不过,在此版本中,我们不仅修复了许多 Bug 错误,还添加了一些功能,使 AdGuard Home 的配置更简单,并保护其免受 DDoS 攻击!
AdGuard Home 0.107.40


更新日期:2023年10月18日
还有什么比阻挡您上网的错误更可怕的呢?幸运的是,我们推出热修复程序以解决所有错误!
AdGuard Home 0.107.39


更新日期:2023年10月11日
我们继续改善 AdGuard Home!在这次更新中,我们添加了一些新功能,修复了错误。
AdGuard Home 0.107.38


更新日期:2023年9月11日
新版本就像水果一样:苹果越美味就越容易招来虫子 (Bug 错误)。 从这个意义上说,前一个版本似乎非常“美味” ,而我们在这次发布的热修复中修复了剩余的错误。
AdGuard Home 0.107.37


更新日期:2023年9月9日
夏天悄悄地溜走了,但我们还是收获了期待已久的功能和改进,以及错误修复!
服务拦截的暂停时间
现在,用户可以一键设置服务拦截过滤器的暂停时间。比如说,在设置中在全天内拦截社交媒体,但是下班后给自己30分钟刷抖音的时间。
这项功能已经在内部开发了几个月,终于可以在这个版本的网页用户界面中使用了!
后备服务器
另一个大家期待已久的功能是,首选上游 DNS 服务器无响应时使用的后备服务器。
后备服务器的语法与首选上游的输入相同,因此用户可以为不同的域名设置不同的后备服务器。
上游的统计数据
与 DNS 上游相关的另一项功能是,在仪表板上显示新的上游统计数据。
新功能让用户查看哪一个上游服务器是速度最快的,哪一个上游服务器使用数量最多的。
致谢
特别感谢我们的开源贡献者 @ssrahul96,以及所有提交和检查问题、添加翻译并帮助我们测试此版本的人!
AdGuard Home 0.107.36


更新日期:2023年8月2日
这次更新我们修复了错误并改进了安全。我们在开发即将发布版本的新功能。
AdGuard Home 0.107.35


更新日期:2023年7月26日
In the previous release, we optimized the filtering-rule list updates, achieving up to three times speedup in some cases. However, the new algorithm proved to be too strict, so in this release we have relaxed its validations while maintaining the optimization for more typical filtering-rule lists 🏎️
As always, there are other minor bug fixes in this release as well.
AdGuard Home 0.107.34


更新日期:2023年7月12日
在这次更新中,我们改进了 AdGuard Home 的安全性,并修复了错误。
安全浏览和 CPU 跳跃
6月,我们发布了 AdGuard Home 的安全性以及错误修复的更新。讽刺的是,更新带来了另一个错误。发布上次更新后,「安全浏览」和「家长控制」就无法正常运作,这在某些情况下导致性能下降、随机崩溃和巨大的 CPU 跳跃。
我们花了整整一个月的时间才弄清楚本问题,如果没有社区成员,包括 @bigwookie、 @TheCableGuy99 和其他人的帮助,我们肯定会花更长的时间解决该问题。事实证明,重大错误实际上是由三个小错误一起造成的。在这次更新中,我们处理好了这些错误。
Docker HEALTHCHECK
Docker 用户应该注意到,Docker 的
HEALTHCHECK 机制已经被移除,因为它会导致很多问题,特别是在与 Podman 和其他流行的 Docker 工具一起使用时。感谢
特别感谢我们的开源贡献者 @Jiraiya8,以及所有提交和检查问题、添加翻译和帮助我们测试此版本的人!
AdGuard Home 0.107.33


更新日期:2023年7月3日
这次是一个错误修复的更新🔧。此外,我们正在进行内部改进,以方便在未来版本中增加新的功能。
AdGuard Home 0.107.32


更新日期:2023年6月13日
热修复,修复了以前版本的错误。
AdGuard Home 0.107.31


更新日期:2023年6月8日
热修复,我们修复了以前版本的两个主要错误。
AdGuard Home 0.107.30


更新日期:2023年6月7日
这次更新我们修复了错误并改进了安全。我们在开发即将发布版本的新功能。
AdGuard Home 0.107.29


更新日期:2023年4月18日
载人空间飞行国际日我们发布了上次更新,但我们的航天器,即 AdGuard Home,的发射出现了一些问题。 在这次更新,我们修复了一些让人讨厌的 Bug,并改进了客户端的忽略功能。
AdGuard Home 0.107.28


更新日期:2023年4月12日
我们终于发布一个包含大量新功能的更新。在这些功能中,我们想提到一些用户期待了很久的改进。
全面保护的暂停
首先,现在有一种方法可以在设定的时间段内暂停保护,从30秒到一整天。 当用户需要访问一个被错误屏蔽的网站或想暂时禁用 AdGuard Home 而不完全关闭它时,这是一个很好用的功能。
 一旦暂停时间结束,AdGuard Home 将重新开启保护。
一旦暂停时间结束,AdGuard Home 将重新开启保护。
 一旦暂停时间结束,AdGuard Home 将重新开启保护。
一旦暂停时间结束,AdGuard Home 将重新开启保护。更好的「安全搜索」管理
其次,用户现在可以通过启用或禁用 Google、Bing、YouTube 等特定服务来微调「安全搜索」设置。
 同样的操作也可以在单个客户层面上进行。此外,我们还改进了对 IPv6 地址的支持。
同样的操作也可以在单个客户层面上进行。此外,我们还改进了对 IPv6 地址的支持。
 同样的操作也可以在单个客户层面上进行。此外,我们还改进了对 IPv6 地址的支持。
同样的操作也可以在单个客户层面上进行。此外,我们还改进了对 IPv6 地址的支持。
AdGuard Home 0.107.27


更新日期:2023年4月5日
这次更新我们修复了一些错误。此外,我们更新了 Go 计算机编程语言的版本。下一个更新将包含更多改进。
AdGuard Home 0.107.26


更新日期:2023年3月9日
今天的更新包括,配置发出请求的和一个基于其类型拒绝请求的新选项,并且我们还修复了很多错误。
AdGuard Home 0.107.25


更新日期:2023年2月21日
这次的热补丁更新防止在使用未加密的 DNS-over-HTTPS 时出现致命的错误,在反向 HTTP 代理后配置 AdGuard Home 的用户遇到了这些错误。
AdGuard Home 0.107.24


更新日期:2023年2月16日
在 AdGuard Home 的新版本我们增加了一种在查询日志和统计信息屏幕上排除特定主机名的方法。这样用户可以更加方便地指定不想阻止的主机名。
AdGuard Home 0.107.23


更新日期:2023年2月1日
字体! 颜色! 按钮! 每个用户都喜欢讨论用户界面设计,但我们更喜欢为我们的亲爱的用户们修复错误,并添加新功能🚢。
除了黑暗模式的调整,这次版本还包括对 DNS64 的支持、几个新的可拦截的服务,以及一些错误修复和内部改进。
AdGuard Home 0.107.22


更新日期:2023年1月19日
漫长的夜晚,没有人喜欢的一件事是,用户界面太亮了,字体都看不清楚🔦。这次更新,AdGuard Home 终于应用了用户最常要求的功能之一,即黑暗模式!
新的黑暗模式仍是实验性的,显得比较粗糙。如果您想报告错误,请按照问题#5375中的说明报告错误。
AdGuard Home 0.107.21


更新日期:2022年12月24日
让冬天更温暖的热修复。
AdGuard Home 0.107.20


更新日期:2022年12月7日
当在世界杯上足球守门员尽力守门,保证球门安全时,我们也尽一切努力保证我们用户的隐私安全,随时发布更新🛡️ 此外,我们还增加了一个按钮让用户轻松清除 DNS 缓存。
AdGuard Home 0.107.19


更新日期:2022年11月23日
您可能发现自己使用社交媒体“过量”了,但现代人难以远离社交媒体。好吧,我们难以远离它们,但感谢 @sandervankasteel ,现在“逃离”社交媒体可以成为生活的一部分了:AdGuard Home 可以拦截流行 Mastodon 实例。休息一下,别再刷网页了,留一部分有意义的时间独处、阅读和成长吧!
除此之外,我们添加了
--update 命令行。现在,一键就可以更新 AdGuard Home。
AdGuard Home 0.107.17


更新日期:2022年11月2日
Despite this release appearing around Halloween, it shouldn't be spooky at all. The main novelty is that the list of services blockable with a single click is now synchronized with AdGuard DNS to make the user experience more unified across AdGuard services. We've also improved support for HTTP/3 as well as fixed a few annoying bugs.
AdGuard Home 0.107.16


更新日期:2022年10月7日
This is a security release. There are no new changes besides the update of the Go programming language version. More substantial changes are to come in the subsequent updates.
Full Changelog
Security
Go version has been updated to prevent the possibility of exploiting the CVE-2022-2879, CVE-2022-2880, and CVE-2022-41715 Go vulnerabilities fixed in Go 1.18.7.
AdGuard Home 0.107.15


更新日期:2022年10月3日
Sometimes, even a hotfix needs a hotfix. In the previous release, our mitigations turned out to be too restrictive, preventing some AdGuard Home features from working properly. In this release, we fix this along with a few other bugs.
We have also added experimental support for the HTTP/3 standard in the UI, DNS upstreams, and DNS clients!
Full Changelog
Security
As an additional CSRF protection measure, AdGuard Home now ensures that requests that change its state but have no body (such as POST /control/stats_reset requests) do not have a Content-Type header set on them #4970.
Added
Experimental HTTP/3 Support
See #3955 and the related issues for more details. These features are still experimental and may break or change in the future.
DNS-over-HTTP/3 DNS and web UI client request support. This feature must be explicitly enabled by setting the new property
dns.serve_http3 in the configuration file to true.DNS-over-HTTP upstreams can now upgrade to HTTP/3 if the new configuration file property
dns.use_http3_upstreams is set to true.Upstreams with forced DNS-over-HTTP/3 and no fallback to prior HTTP versions using the h3:// scheme.
Fixed
only application/json is allowed errors in various APIs #4970.
AdGuard Home 0.107.14


更新日期:2022年9月29日
This is a security release. Users are encouraged to update AdGuard Home as soon as possible.
Full Changelog
Security
A Cross-Site Request Forgery (CSRF) vulnerability has been discovered. The CVE number is to be assigned. We thank Daniel Elkabes from Mend for reporting this vulnerability to us.
SameSite PolicyThe
SameSite policy on the AdGuard Home session cookies has been upgraded to Lax. Which means that the only cross-site HTTP request for which the browser is allowed to send the session cookie is navigating to the AdGuard Home domain.Users are strongly advised to log out, clear browser cache, and log in again after updating.
Removal Of Plain-Text APIs (BREAKING API CHANGE)
We have implemented several measures to prevent such vulnerabilities in the future, but some of these measures break backwards compatibility for the sake of better protection.
The following APIs, which previously accepted or returned
text/plain data, now accept or return data as JSON. All new formats for the request and response bodies are documented in openapi/openapi.yaml and openapi/CHANGELOG.md.GET /control/i18n/current_language;POST /control/dhcp/find_active_dhcp;POST /control/filtering/set_rules;POST /control/i18n/change_language.Stricter
Content-Type Checks (BREAKING API CHANGE)All JSON APIs now check if the request actually has
Content-Type set to application/json.Other Security Changes
AdGuard Home 0.107.13


更新日期:2022年9月14日
In this hotfix release with the “lucky” patch number we have fixed a couple of issues that prevented some DHCP clients from receiving their assigned IP addresses. We've also added the new
dns.ipset_file setting, which should help users who maintain large ipsets, for example to use in firewall or VPN settings.Full Changelog
Added
The new optional
dns.ipset_file property, which can be set in the configuration file. It allows loading the ipset list from a file, just like dns.upstream_dns_file does for upstream servers #4686.Changed
The minimum DHCP message size is reassigned back to BOOTP's constraint of 300 bytes #4904.
Fixed
Panic when adding a static lease within the disabled DHCP server #4722.
AdGuard Home 0.107.12


更新日期:2022年9月7日
What better way is there to celebrate the coming of autumn than a patch release? In this new version, we have extended and significantly improved AdGuard Home's built-in DHCP server (fixing many bugs in the process) as well as improved our service blocking feature, thanks to many contributions from the community. As always, we have also updated our tooling to make sure that we use the latest versions without any known security issues.
Full Changelog
Security
Go version was updated to prevent the possibility of exploiting the CVE-2022-27664 and CVE-2022-32190 Go vulnerabilities fixed in Go 1.18.6.
Added
New
del DHCP option which removes the corresponding option from server's response #4337. See also a Wiki page.NOTE: This modifier affects all the parameters in the response and not only the requested ones.
A new HTTP API,
GET /control/blocked_services/services, that lists all available blocked services #4535.Changed
The DHCP options handling is now closer to the [RFC 2131][rfc-2131] (#4705).
When the DHCP server is enabled, queries for domain names under
dhcp.local_domain_name not pointing to real DHCP client hostnames are now processed by filters (#4865).The internal DNS client, used to resolve hostnames of external clients and also during automatic updates, now respects the upstream mode settings for the main DNS client #4403.
Deprecated
Ports 784 and 8853 for DNS-over-QUIC in Docker images. Users who still serve DoQ on these ports are encouraged to move to the standard port 853. These ports will be removed from the
EXPOSE section of our Dockerfile in a future release.Go 1.18 support. Future versions will require at least Go 1.19 to build.
Fixed
Dynamic leases created with empty hostnames #4745.
Unnecessary logging of non-critical statistics errors #4850.
AdGuard Home 0.107.11


更新日期:2022年8月19日
This hot summer is approaching its end, but hotfixes are still coming in! In this release, we have fixed configuration file migrations not working for people with AdGuard Home versions older than v0.107.7, as well as made a few minor improvements.
--
Full Changelog
--
Added
AdGuard Home 0.107.10


更新日期:2022年8月17日
In this new release, we add support for the new Discovery of Designated Resolvers DDR feature, which allows clients using plain DNS to automatically switch to secure protocols. As well as an Arabic localization and fixes for a couple of rather annoying bugs.
Full Changelog
Added
AdGuard Home 0.107.9


更新日期:2022年8月3日
Although not a lot of time has passed since the last release, this new one contains a security update, a new feature, a new platform, and some minor fixes :wrench:. It's always nice to have those!
Full Changelog
Security
Go version was updated to prevent the possibility of exploiting the CVE-2022-32189 Go vulnerability fixed in Go 1.18.5. Go 1.17 support has also been removed, as it has reached end of life and will not receive security updates.
Added
Domain-specific upstream servers test. If such test fails, a warning message is shown #4517.
windows/arm64 support #3057.
Changed
UI and update links have been changed to make them more resistant to DNS blocking.
Fixed
Go 1.17 support, as it has reached end of life.
AdGuard Home 0.107.8


更新日期:2022年7月19日
孔子说,人非圣贤孰能无过。因此,我们要积极面对自己的错误,并改成它。而这正是我们发现了错误修复版本之后做的第一件事情。
更新日志
安全
Go 版本已更新,以防止利用
CVE-2022-1705、CVE-2022-32148、CVE-2022-30631 和其他在 [Go 1.17.12] 中修复的 Go 漏洞的可能性(https://groups.google.com/g/golang-announce/c/nqrv9fbR0zE)。修复
AdGuard Home 0.107.7


更新日期:2022年7月19日
这个夏季我们给大家带来了 AdGuard Home 的新版本!
DNS-over-QUIC:RFC 9250
等待已久的 DNS-over-QUIC 协议终于改进了,成为了正式标准版本,RFC 9250。这次更新,我们以向后兼容的方式添加了正式版本的支持。
对上游的更多管控
现在,用户可以指定每一个网域的子网域的上游,同时排除网域本身。比方说,如用户想要把
server-1.example.com 查询由 1.1.1.1 的 DNS 服务器解析,但是把 example.com 依然由默认上游(在这种情况下,是 94.140.14.14)解析,那么您需要使用:94.140.14.14
[/*.example.com/]1.1.1.1说到上游,现在用户无须记得无加密 DNS 上游的 IP 地址。Bootstrap 服务器就能够解析它们,您就可以使用新的
udp:// 上游地址方案来自动解析上游的地址。udp://one.one.one.one # Same as 1.1.1.1.其他重要更新
现在,用户对如何收集运行时客户端信息有了更多的控制,包括完全禁用这一功能的选择。
来自客户请求的 EDNS 客户子网信息现显示于查询日志页上。
像往常一样,我们努力保持我们的工具与时俱进,以确保我们给用户们提供的安全网没有漏洞。
此外,还有更多小的改进。您可以查看更新日志了解所有改进!
致谢
特别感谢我们的开源贡献者,@Lanius-collaris,以及所有提交和检查问题、添加翻译和帮助我们测试这个版本的客户。
更新日志
安全
Go 版本已经更新了以防止可能被利用
CVE-2022-29526, CVE-2022-30634, CVE-2022-30629, CVE-2022-30580,以及 CVE-2022-29804 的弱点。
CVE-2022-29526, CVE-2022-30634, CVE-2022-30629, CVE-2022-30580,以及 CVE-2022-29804 的弱点。
强制执行的密码强度策略#3503.
添加的功能
只支持一个域的子域的上游
#4503.
能够通过
clients.runtime_sources 配置单独控制每个运行时客户端的来源 #3020.通过配置文件中新的
dns.private_networks属性,能够定制被认为是私有的网络集 #3142.在查询日志记录的请求细节部分的 EDNS 客户子网信息 #3978.
支持使用
udp://方案的普通UDP上游服务器的主机名 #4166.在 FreeBSD 和 OpenBSD 上,当 AdGuard Home 以服务形式安装时,现在默认会收集日志 #4213.
改进
在 OpenBSD 上,认识系统服务脚本现在使用推荐的
/bin/ksh shell,而不是 /bin/sh#4533。 要应用这一变化,请备份您的数据并运行 AdGuardHome -s uninstall && AdGuardHome -s install。反向 DNS 现在作为运行时客户的信息来源,比 ARP 具有更大的优先权。
通过更有弹性的 ARP 处理,改进对正在运行的客户的检测 #3597.
从乐观缓存提供的响应的TTL现在被降低到10秒。
特定域的私有反向 DNS 上游服务器现在被验证为只允许
*.in-addr.arpa 和 *.ip6.arpa 域指向本地服务的网络#3381。注意:如果你的配置中已经有无效的条目,请考虑手动删除它们,因为它们基本上没有作用。响应过滤现在使用信息回答部分的记录类型来执行,而不是问题的类型。#4238.
现在,构建脚本不再需要添加构建时间信息,而是使用标准化的环境变量 [
SOURCE_DATE_EPOCH][repr] 来添加构建二进制文件的提交日期 #4221 。 这应该可以简化软件包维护者和那些编译自己的AdGuard Home的人的可重复构建过程。配置文件中的
dns.bogus_nxdomain 属性现在支持CIDR符号和 IP 地址#1730.配置改进
在这个版本中,模式的版本已经从12变成了14。
对象
clients,在模式 13 和更早的版本中是一个实际持久性客户的数组,现在是由 persistent 和 runtime_sources 属性组成。# BEFORE:
'clients':
- name: client-name
# …
# AFTER:
'clients':
'persistent':
- name: client-name
# …
'runtime_sources':
whois: true
arp: true
rdns: true
dhcp: true
hosts: trueclients.runtime_sources.rdns 字段的值取自 dns.resolve_clients 属性。 要撤销这一变化,请删除 runtime_sources 属性,将 persistent 的内容移入 clients 本身,将clients.runtime_sources.rdns的值移入dns.resolve_clients,并将 schema_version 改回 13。属性
local_domain_name,在模式12和更早的版本中曾经是 dns 对象的一部分,现在是 dhcp 对象的一部分。# BEFORE:
'dns':
# …
'local_domain_name': 'lan'
# AFTER:
'dhcp':
# …
'local_domain_name': 'lan'要撤销这一变化,将该属性移回
dns 对象,并将 schema_version 改回 12。修改
--no-etc-hosts选项。 它的功能现在由 "clients.runtime_sources.hosts "配置属性控制。修复
AdGuard Home 0.107.6


更新日期:2022年4月14日
This is a small security-oriented update. This AdGuard Home version requires Go v1.17 and later to build, because older Go versions receive no further support, including security patches.
Aside from that, we've slightly updated
$dnsrewrite modifier to support the user-defined Discovery of Designated Resolvers (DDR). We are planning on continuing to make more improvements to it in the future updates, see #4463.The rest are minor changes and ever-present bugfixes.
Full Changelog
Security
User-Agent HTTP header removed from outgoing DNS-over-HTTPS requests.Go version was updated to prevent the possibility of exploiting the CVE-2022-24675, CVE-2022-27536, and CVE-2022-28327 vulnerabilities.
Added
Changed
Filtering rules with the dnsrewrite modifier that create SVCB or HTTPS responses should use ech instead of echconfig to conform with the latest drafts.
Deprecated
SVCB/HTTPS parameter name
echconfig in filtering rules with the dnsrewrite modifier. Use ech instead. v0.109.0 will remove support for the outdated name echconfig.Obsolete --no-mem-optimization option #4437. v0.109.0 will remove the flag completely.
Fixed
I/O timeout errors when checking for the presence of another DHCP server.
Network interfaces being incorrectly labeled as down during installation.
Rules for blocking the QQ service #3717.
Removed
Go 1.16 support, since that branch of the Go compiler has reached end of life and doesn't receive security updates anymore.
AdGuard Home 0.107.5


更新日期:2022年4月14日
This is a security release. There are no new changes besides the update of the Go programming language version.
More substantial changes are to come in the subsequent updates.
Full Changelog
Security
Go version was updated to prevent the possibility of exploiting the CVE-2022-24921 vulnerability. As the CVE page is still showing “reserved” at the time of publishing, see also golang/go#51112.
AdGuard Home 0.107.4


更新日期:2022年4月14日
A small update to fix a couple bugs and shore up some Go vulnerabilities.
More substantial changes are to come in the subsequent updates.
Full Changelog
Security
Go version was updated to prevent the possibility of exploiting the CVE-2022-23806, CVE-2022-23772, and CVE-2022-23773 vulnerabilities.
Changed
Minor UI improvements.
Fixed
AdGuard Home 0.107.3


更新日期:2022年2月3日
This version contains bug fixes and cleanups 🧹. Also, there is a new minor feature: now you can rewrite responses for domains using the response code
NOERROR. Similar rules will allow to get a successful response without records, e.g.:|example.com^$dnsrewrite=NOERRORFull Changelog
Added
AdGuard Home 0.107.2


更新日期:2022年1月12日
You know, it is very hard to break your bad habits. We're still struggling with one, the overwhelming need to roll out hotfixes to AdGuard Home releases 😢
Now this one is a hotfix release for a really critical CPU overconsumption bug in v0.107.1.
Please update asap and with this, we wish you happy holidays!🎄
Full Changelog
Fixed
Infinite loops when TCP connections time out (#4042).
AdGuard Home 0.107.1


更新日期:2022年1月12日
In a not-futile-at-all-we-swear 😅 attempt to fix all bugs before the New Year we're rolling out a hotfix to the recent v0.107.0. Hopefully, this time we got it all right. And if not, there are still a couple of sheets left on the calendar 📆 and the mug is still half-full with lukewarm coffee ☕
Acknowledgements
A special thanks to our open-source contributors: @Aikatsui and @mdawsonuk, as well as to everyone who filed and inspected issues, added translations, and helped us test this release!
Full Changelog
Changed
The validation error message for duplicated allow- and blocklists in DNS settings now shows the duplicated elements (#3975).
Fixed
ipset initialization bugs (#4027).Legacy DNS rewrites from a wildcard pattern to a subdomain (#4016).
Service not being stopped before running the
uninstall service action (#3868).Broken
reload service action on FreeBSD.Legacy DNS rewrites responding from upstream when a request other than
A or AAAA is received (#4008).Panic on port availability check during installation (#3987).
Incorrect application of rules from the OS's hosts files (#3998).
AdGuard Home 0.107.0


更新日期:2022年1月12日
We've had some big AdGuard Home updates in the past, but this one is to top them all. It's been brewing for almost eight months! 🙀 So no wonder there's heaps upon heaps of new features, improvements, bugfixes, and other changes. We'd better start listing them ASAP, or else we'll be risking missing the New Year's fireworks 🎆 🥂
Native Apple Silicon support
There's no shortage of killer features in this changelog, but this one takes the cake as the biggest of them all, without any doubt. You won't have to resort to Rosetta or any such solutions anymore if you want to configure AdGuard Home on a Mac with a Silicon chip.
RFC 9000 support In DNS-over-QUIC
It's not quite over nine thousand, but it'll do. The IETF has formalized QUIC this year with RFC 9000, and DNS-over-QUIC protocol finally supports it. If you haven't tried DoQ yet, consider this a sign.
$dnsrewrite rules and other DNS rewrites will now be applied even when protection is disabled (#1558)
Another popular demand. This change only makes sense, as DNS rewrites often carry a different purpose than simply blocking ads or trackers. You still can disable them by opening the admin panel, going to Settings → General settings, and removing the check mark from the Block domains using filters and hosts files box.
Note: rules contained in system hosts files (e.g.
/etc/hosts) now have higher priority. This may result in more rewrites appearing in your Query log. If some of these rewrites are invalid, remove the corresponding lines from your hosts files or comment them out.DNS-over-HTTPS queries now use the real IP address of the client instead of the address of the proxy (#2799)
Note that this change concerns only those proxies that you've added to the list of "Trusted proxies", otherwise it would be a major security risk. We wouldn't want anything of that sort to happen to you! 🙅♀️ Right now
trusted_proxies can only be configured in AdGuardHome.yaml, but that might change in the future.Optimistic DNS cache (#2145)
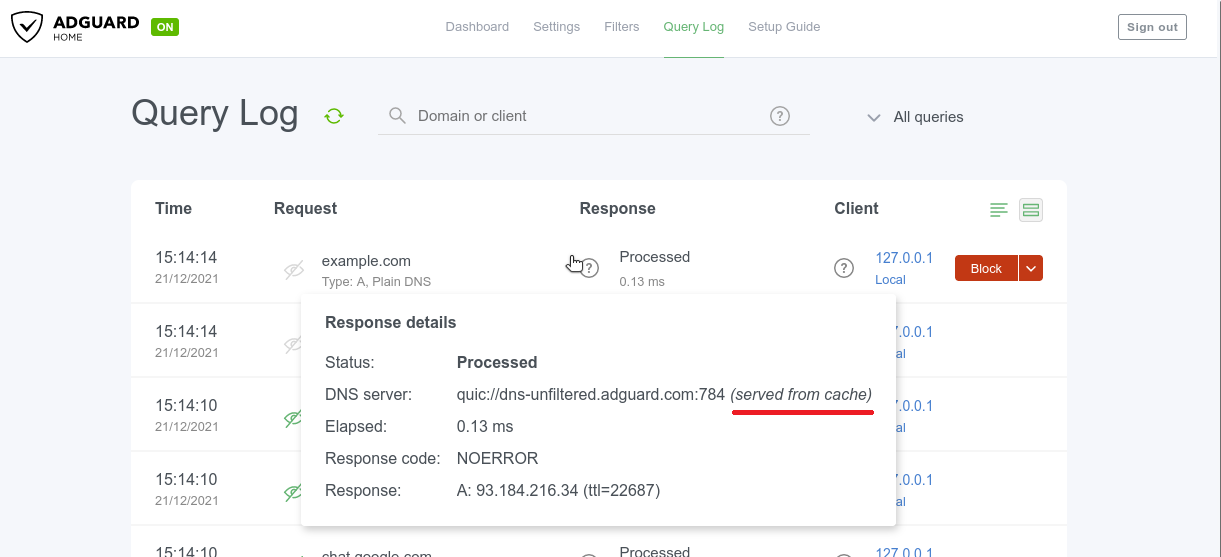
To reduce latency you may make AdGuard Home respond from the cache even when the stored entry is expired, while trying to refresh them at the same time🔄 This checkbox is located in Settings → DNS settings → DNS cache configuration and it's not ticked by default. Responses made from DNS cache are marked with a special label in the Query log.
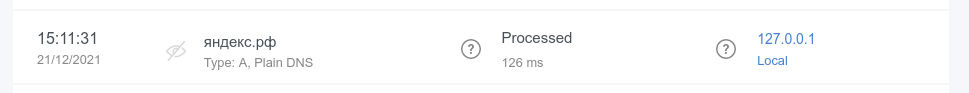
Query log search now supports internationalized domains (#3012)
Internationalized domain names (IDNAs) are domain names that contain symbols in non-Latin script/alphabet, such as
яндекс.рф or ουτοπία.δπθ.gr, for example. Previously, they were being converted to Unicode in AG Home Query log (xn--d1abqjx3f.xn--p1ai and xn--kxae4bafwg.xn--pxaix.gr in our examples), which is a detriment in most cases. Now IDNAs are displayed as is, and you can search for them without resorting to Unicode.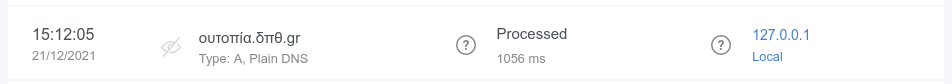
Acknowledgements
A special thanks to our open-source contributors: @Aikatsui, @anbraten, @bruvv, @DandelionSprout, @fvdm, @hnefatl, @markhicken, @p27877, and @systemcrash, as well as to everyone who filed and inspected issues, added translations, and helped us test this release! 🙏
Full Changelog
Added
Upstream server information for responses from cache (#3772). Note that old log entries concerning cached responses won't include that information.
Finnish and Ukrainian translations.
Setting the timeout for IP address pinging in the "Fastest IP address" mode through the new
fastest_timeout field in the configuration file (#1992).Static IP address detection on FreeBSD (#3289).
Optimistic cache (#2145).
New possible value of
6h for querylog_interval setting (#2504).Blocking access using client IDs (#2624, #3162).
source directives support in /etc/network/interfaces on Linux (#3257).RFC 9000 support in DNS-over-QUIC.
Completely disabling statistics by setting the statistics interval to zero (#2141).
The ability to completely purge DHCP leases (#1691).
Settable timeouts for querying the upstream servers (#2280).
Configuration file parameters to change group and user ID on startup on Unix (#2763).
Experimental OpenBSD support for AMD64 and 64-bit ARM CPUs (#2439, #3225, #3226).
Support for custom port in DNS-over-HTTPS profiles for Apple's devices (#3172).
darwin/arm64 support (#2443).freebsd/arm64 support (#2441).Output of the default addresses of the upstreams used for resolving PTRs for private addresses (#3136).
Detection and handling of recurrent PTR requests for locally-served addresses (#3185).
The ability to completely disable reverse DNS resolving of IPs from locally-served networks (#3184).
New flag
--local-frontend to serve dynamically changeable frontend files
from disk as opposed to the ones that were compiled into the binary.Changed
Port bindings are now checked for uniqueness (#3835).
The DNSSEC check now simply checks against the AD flag in the response (#3904).
Client objects in the configuration file are now sorted (#3933).
Responses from cache are now labeled (#3772).
Better error message for ED25519 private keys, which are not widely supported (#3737).
Cache now follows RFC more closely for negative answers (#3707).
$dnsrewrite rules and other DNS rewrites will now be applied even when the protection is disabled (#1558).DHCP gateway address, subnet mask, IP address range, and leases validations (#3529).
The
systemd service script will now create the /var/log directory when it doesn't exist (#3579).Items in allowed clients, disallowed clients, and blocked hosts lists are now required to be unique (#3419).
The TLS private key previously saved as a string isn't shown in API responses anymore (#1898).
Better OpenWrt detection (#3435).
DNS-over-HTTPS queries that come from HTTP proxies in the
trusted_proxies list now use the real IP address of the client instead of the address of the proxy (#2799).Clients who are blocked by access settings now receive a
REFUSED response when a protocol other than DNS-over-UDP and DNSCrypt is used.querylog_interval setting is now formatted in hours.Query log search now supports internationalized domains (#3012).
Internationalized domains are now shown decoded in the query log with the original encoded version shown in request details (#3013).
When /etc/hosts-type rules have several IPs for one host, all IPs are now returned instead of only the first one (#1381).
The setting
rlimit_nofile is now in the os block of the configuration file, together with the new group and user settings (#2763).Permissions on filter files are now
0o644 instead of 0o600 (#3198).Configuration Changes
In this release, the schema version has changed from
10 to 12.Parameter
dns.querylog_interval, which in schema versions 11 and earlier used to be an integer number of days, is now a string with a human-readable duration:# BEFORE:
'dns':
# …
'querylog_interval': 90
# AFTER:
'dns':
# …
'querylog_interval': '2160h'To rollback this change, convert the parameter back into days and change the
schema_version back to 11.Parameter
rlimit_nofile, which in schema versions 10 and earlier used to be on the top level, is now moved to the new os object:# BEFORE:
'rlimit_nofile': 42
# AFTER:
'os':
'group': ''
'rlimit_nofile': 42
'user': ''To rollback this change, move the parameter on the top level and change the
schema_version back to 10.Deprecated
Go 1.16 support. v0.108.0 will require at least Go 1.17 to build.
Fixed
EDNS0 TCP keepalive option handling (#3778).
Rules with the
$denyallow modifier applying to IP addresses when they shouldn't (#3175).The length of the EDNS0 client subnet option appearing too long for some upstream servers (#3887).
Invalid redirection to the HTTPS web interface after saving enabled encryption settings (#3558).
Incomplete propagation of the client's IP anonymization setting to the statistics (#3890).
Incorrect
$dnsrewrite results for entries from the operating system's hosts file (#3815).Matching against rules with
| at the end of the domain name (#3371).Incorrect assignment of explicitly configured DHCP options (#3744).
Occasional panic during shutdown (#3655).
Addition of IPs into only one as opposed to all matching ipsets on Linux (#3638).
Removal of temporary filter files (#3567).
Panic when an upstream server responds with an empty question section (#3551).
9GAG blocking (#3564).
DHCP now follows RFCs more closely when it comes to response sending and option selection (#3443, #3538).
Occasional panics when reading old statistics databases (#3506).
reload service action on macOS and FreeBSD (#3457).Inaccurate using of service actions in the installation script (#3450).
Client ID checking (#3437).
Discovering other DHCP servers on
darwin and freebsd (#3417).Switching listening address to unspecified one when bound to a single specified IPv4 address on Darwin (macOS) (#2807).
Incomplete HTTP response for static IP address.
DNSCrypt queries weren't appearing in query log (#3372).
Wrong IP address for proxied DNS-over-HTTPS queries (#2799).
Domain name letter case mismatches in DNS rewrites (#3351).
Conflicts between IPv4 and IPv6 DNS rewrites (#3343).
Letter case mismatches in
CNAME filtering (#3335).Occasional breakages on network errors with DNS-over-HTTP upstreams (#3217).
Errors when setting static IP on Linux (#3257).
Treatment of domain names and FQDNs in custom rules with
$dnsrewrite that use the PTR type (#3256).Redundant hostname generating while loading static leases with empty hostname (#3166).
Domain name case in responses (#3194).
Custom upstreams selection for clients with client IDs in DNS-over-TLS and DNS-over-HTTP (#3186).
Incorrect client-based filtering applying logic (#2875).
Removed
Go 1.15 support.
AdGuard Home 0.106.3


更新日期:2021年5月19日
More! More bugfixes! 🧟♀️
But this time, for a change, there's a couple of new minor features to go with them. Hope you don't mind 🤷♂️
A special thanks to our open-source contributor, @ashishwt, as well as to everyone who filed and inspected issues, added translations, and helped us to test this release!
Added
Changed
Add microseconds to log output.
Fixed
Intermittent "Warning: ID mismatch" errors #3087.
Error when using installation script on some ARMv7 devices #2542.
Local PTR request recursion in Docker containers #3064.
Ignoring client-specific filtering settings when filtering is disabled in general settings #2875.
Disallowed domains are now case-insensitive #3115.
Other minor fixes and improvements.
AdGuard Home 0.106.2


更新日期:2021年5月19日
It's not Friday? Not a problem! We defy the tradition of Friday hotfixes by rushing another one out a day earlier 🙌
A special thanks to our open-source contributor, @jankais3r, as well as to everyone who filed issues, added translations, and helped us to test this release!
Fixed
AdGuard Home 0.106.1


更新日期:2021年5月19日
We had a release a couple days ago. You all knew it would come to this. 🦸
It's Friday.
It's hotfix time! 🔥
Nothing serious though, we didn't even break anything. Just cleaning up some minor bugs. 🧹
Fixed
AdGuard Home 0.106.0


更新日期:2021年5月19日
Quite a lot of changes this time around, even if there aren't as many standouts as in some of the previous updates. We're sure that you'll be able to find a line or two in the changelog that speaks to you!
And one of the reasons for that is the constant support from the community. 👥👥 Special thanks to our open-source contributors: @jvoisin and @Paraphraser, as well as to everyone who filed issues, added translations, and helped us to test this release! 🙇
The ability to set up custom upstreams to resolve PTR queries for local addresses and to disable the automatic resolving of clients' addresses #2704
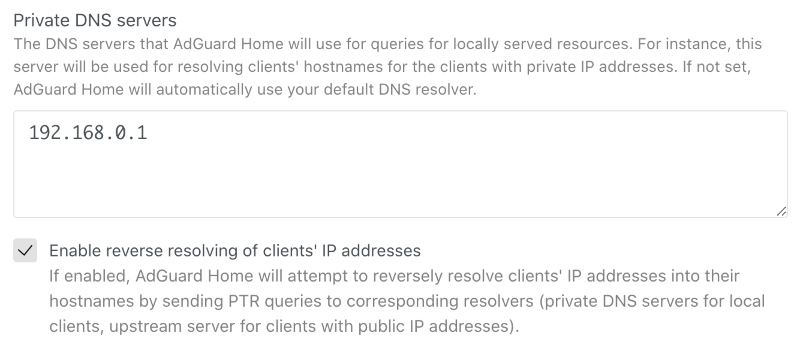
This option will improve your DNS privacy when it comes to addressing local resources. Give it a go unless you want to share your private data with googles of the world.
Search by clients' names in the query log #1273
There's not much that can be said about this feature, it's quite self-explanatory: now you can search up queries by specific clients. 🤷♀️
However, we wanted to highlight it anyway since so many of you have asked for it for quite a while. Hopefully, we delivered! 😅
Added
The ability to block user for login after configurable number of unsuccessful attempts for configurable time #2826.
$denyallow modifier for filters #2923.Hostname uniqueness validation in the DHCP server #2952.
Hostname generating for DHCP clients which don't provide their own #2723.
New flag
--no-etc-hosts to disable client domain name lookups in the operating system's /etc/hosts files #1947.Logging of the client's IP address after failed login attempts #2824.
Verbose version output with
-v --version#2416.The ability to serve DNS queries on multiple hosts and interfaces #1401.
Changed
Quality of logging #2954.
The access to the private hosts is now forbidden for users from external networks #2889.
The reverse lookup for local addresses is now performed via local resolvers #2704.
Stricter validation of the IP addresses of static leases in the DHCP server with regards to the netmask #2838.
Stricter validation of
$dnsrewrite filter modifier parameters #2498.New, more correct versioning scheme #2412.
Deprecated
Go 1.15 support. v0.107.0 will require at least Go 1.16 to build.
Fixed
Multiple answers for
$dnsrewrite rule matching requests with repeating patterns in it #2981.Root server resolving when custom upstreams for hosts are specified #2994.
Inconsistent resolving of DHCP clients when the DHCP server is disabled #2934.
Comment handling in clients' custom upstreams #2947.
Overwriting of DHCPv4 options when using the HTTP API #2927.
Assumption that MAC addresses always have the length of 6 octets #2828.
Support for more than one
/24 subnet in DHCP #2541.Invalid filenames in the
mobileconfig API responses #2835.Removed
Go 1.14 support.
AdGuard Home 0.105.2


更新日期:2021年3月15日
There are big flashy updates, and there are seemingly unassuming ones, which constitute, however, the backbone of any successful project. This is the latter, as you may have guessed. You'll find here a heap of bugfixes and a security update for CVE-2021-27935.
Security
Session token doesn't contain user's information anymore (#2470).
Fixed
Incomplete hostnames with trailing zero-bytes handling (#2582).
Wrong DNS-over-TLS ALPN configuration (#2681).
Inconsistent responses for messages with EDNS0 and AD when DNS caching is
enabled (#2600).
Incomplete OpenWrt detection (#2757).
DHCP lease's
expired field incorrect time format (#2692).Incomplete DNS upstreams validation (#2674).
Wrong parsing of DHCP options of the
ip type (#2688).
AdGuard Home v0.105.1


更新日期:2021年2月16日
Have you ever thought about why traditions are so important?🧙♂️ Traditions help us remember that we are part of a history that defines our past, shapes who we are today, and who we are likely to become. This is why we at AdGuard respect our traditions, and the most important one is pushing the inevitable hotfix right after every major update.🔥🔧
Jokes aside, here's the list of things fixed and improved in this hotfix.
Changed
"Permission denied" errors when checking if the machine has a static IP no
longer prevent the DHCP server from starting (#2667).
The server name sent by clients of TLS APIs is not only checked when
strict_sni_check is enabled (#2664).Fixed
Error when enabling the DHCP server when AdGuard Home couldn't determine if
the machine has a static IP.
Optical issue on custom rules (#2641).
Occasional crashes during startup.
The field
"range_start" in the GET /control/dhcp/status HTTP API response
is now correctly named again (#2678).DHCPv6 server's
ra_slaac_only and ra_allow_slaac settings aren't reset to
false on update any more (#2653).The
Vary header is now added along with Access-Control-Allow-Origin to
prevent cache-related and other issues in browsers (#2658).The request body size limit is now set for HTTPS requests as well.
Incorrect version tag in the Docker release (#2663).
DNSCrypt queries weren't marked as such in logs (#2662).
AdGuard Home 0.105.0


更新日期:2021年2月12日
We took our sweet time with this update, but you'll most certainly find it to be worth the wait. The changelog contains three absolute 💥bangers and a laundry list of lesser changes.
🕵️♂️ Client ID support for DNS-over-HTTPS, DNS-over-QUIC, and DNS-over-TLS #1387
This feature would be really useful to those of you who run an encrypted DNS resolver on a public server. In short, you can now identify your devices not just by their IP address (which is, frankly, not too useful in a public server scenario 🤷♀️), but by using a special "Client ID".

Here's how it works:
First, you add a client and specify an arbitrary string as its "Identifier", for instance,
my-iphone.On the client device you can now configure:
DNS-over-HTTPS: https://example.org/dns-query/my-iphoneQueries and stats are now properly attributed to your device.

🔐 AdGuard as a DNSCrypt-resolver #1361
DNSCrypt was the very first DNS encryption protocol that got some traction. It may not be as popular as DoH/DoT/DoQ now, but it is still viable. Moreover, performance-wise DNSCrypt is better than any of them. And now that v0.105.0 is out, AdGuard Home can be configured to work as a DNSCrypt resolver!
However, here goes the tricky part. We haven't yet exposed these settings to the Web admin panel so if you want to have DNSCrypt, you'll need to follow this instruction and do it via editing the configuration file (
AdGuardHome.yaml). Not that it would scare you off, would it? 🤓
Regarding DNSCrypt clients - AdGuard for Android, Windows and iOS support it, Mac will get its support pretty soon. Besides that, here is a long list of client software that supports it as well.
🆎 $dnsrewrite and $dnstype modifiers #2102#2337
AdGuard Home now supports two more powerful rule modifiers that will help blocklists' maintainers.
$dnstype lets you narrow down the rule scope and apply it only to queries of a specific type(s). For instance, Apple devices now support HTTPS DNS query type. While being generally a good thing, this new type may sometimes be harmful😲. By using $dnstype you can block it completely using a simple rule like this: $dnstype=HTTPS$dnsrewrite is another powerful modifier that allows you to modify DNS responses. Note that this modifier is much more powerful compared to something like a hosts file.Here are some examples:
||example.org^$dnsrewrite=SERVFAIL;; - return SERVFAIL for example.org and all it's subdomains|test.example.org^$dnsrewrite=NOERROR;TXT;hello_world - add a TXT record for test.example.org|example.org^$dnsrewrite=example.com - redirect example.org to example.com|example.org^$dnsrewrite=1.1.1.1 - redirect example.org to example.comYou can find more examples in the documentation.
Added
The host checking API and the query logs API can now return multiple matched rules #2102
Detecting of network interface configured to have static IP address via
/etc/network/interfaces#2302A 5 second wait period until a DHCP server's network interface gets an IP address #2304
HTTP API request body size limit #2305
Changed
Access-Control-Allow-Origin is now only set to the same origin as the domain, but with an HTTP scheme as opposed to *#2484workDir now supports symlinks.Stopped mounting together the directories
/opt/adguardhome/conf and /opt/adguardhome/work in our Docker images #2589When
dns.bogus_nxdomain option is used, the server will now transform responses if there is at least one bogus address instead of all of them #2394. The new behavior is the same as in dnsmasq.Made the mobileconfig HTTP API more robust and predictable, add parameters and improve error response #2358
Improved HTTP requests handling and timeouts #2343
Our snap package now uses the
core20 image as its base #2306Deprecated
Go 1.14 support. v0.106.0 will require at least Go 1.15 to build.
The
darwin/386 port. It will be removed in v0.106.0.The
"rule" and "filter_id" fields in GET /filtering/check_host and
GET /querylog responses. They will be removed in v0.106.0 #2102Fixed
Autoupdate bug in the Darwin (macOS) version #2630
Inability to set DNS cache TTL limits #2459
Possible freezes on slower machines #2225
A mitigation against records being shown in the wrong order on the query log page #2293
A JSON parsing error in query log #2345
Incorrect detection of the IPv6 address of an interface as well as another infinite loop in the
/dhcp/find_active_dhcp HTTP API #2355Removed
The undocumented ability to use hostnames as any of
bind_host values in the configuration. Documentation requires them to be valid IP addresses, and now the implementation makes sure that that is the case #2508Dockerfile#2276. Replaced with the script scripts/make/build-docker.sh which uses scripts/make/Dockerfile.Support for pre-v0.99.3 format of query logs #2102
AdGuard Home 0.104.3


更新日期:2021年2月12日
Bugfixes... 😌 There's something about them that we just can't resist. We always want more! 🧟
When there's nothing more to fix, we just roll out a new major update, introduce some fresh bugs and start all over. It's a circle of life ☯️
Luckily, there are still some to prey upon in v0.104. Have a look at what we've fixed this time:
Fixed
Don't expose the profiler HTTP API #2336
Load query logs from files after loading the ones buffered in memory #2325
Don't show Unnecessary errors in logs when switching between query log files #2324
Don't show
404 Not Found errors on the DHCP settings page on Windows. Show that DHCP is not currently available on that OS instead #2295Fix an infinite loop in the
/dhcp/find_active_dhcp HTTP API method #2301Various internal improvements
AdGuard Home 0.104.1


更新日期:2021年2月12日
Those who pay close attention to AdGuard Home releases know that we keep hotfixes close to our hearts 🔥♥️ This time we held for as long as we could, but ultimately gave in to the urge 😔
Here's a patch to v0.104 with some fixes and minor improvements.
Fixed
Solve the
permission denied error when launching a DHCP server on Linux using Snap#2228. Users experiencing this issue should refresh their snap and call:
snap connect adguard-home:network-controlThis won't be required in the future versions.
Use matching fonts in the Custom Filters textarea #2254
Show the correct query type for DNS-over-QUIC queries in query log #2241
Increase the default number of simultaneous requests to improve performance #2257
Always set a secondary DNS in DHCP #1708
Improve stability on DNS proxy restart #2242
Improve logging on DNS proxy restart #2252
Don't show a “Loading” message and don't rerequest logs once we've reached the end of logs on the query log page #2229
Various internal improvements.
AdGuard Home 0.104.0


更新日期:2021年2月12日
We have something special for y'all today. Not just an implementation of a new feature but the first ever implementation of a new feature! 😮 This is about DNS-over-QUIC, a new DNS encryption protocol — read on to learn more.
Ah, yes, there's also a bunch of other good stuff, too: DHCP-related changes, a .mobileconfig generator for iOS and macOS, and a handful of other enhancements and bugfixes.
DNS-over-QUIC support #2049
AdGuard Home now natively supports a new DNS encryption protocol called DNS-over-QUIC. DoQ standard is currently in the draft state, and AdGuard Home (and dnsproxy) is it's first open-source implementation.🥇

So what's good about it? 🤔 Unlike DoH and DoT, it uses QUIC as a transport protocol and finally brings DNS back to its roots — working over UDP. It brings all the good things that QUIC has to offer — out-of-the-box encryption, reduced connection times, better performance when data packets are lost. Also, QUIC is supposed to be a transport-level protocol and there are no risks of metadata leaks that could happen with DoH. 🔒
At this moment, the only major public DNS resolver that provides DNS-over-QUIC is AdGuard DNS. 😎 Use
quic://dns-unfiltered.adguard.com in the upstreams settings to start using AdGuard DNS "Non-Filtering".DHCP rework: DHCP6 support, custom DHCP options
We did a huge rework of our DHCP server implementation. Thanks to it, AdGuard Home now supports DHCP6 and allows setting custom DHCP options.
Please note that in order to set DHCP options, you'll need to edit the configuration file.
Add support for DHCPv6: #779
DHCPv6 RA+SLAAC: #2076
DHCP: automatic hostnames: #1956
Add DHCP Options: #1585
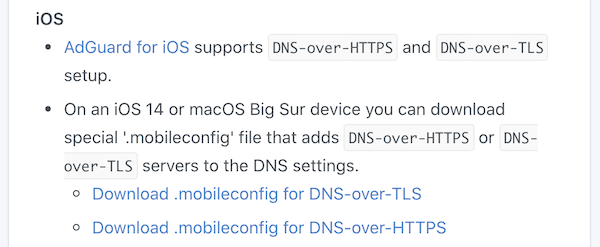
iOS and MacOS .mobileconfig generator: #2110
iOS 14 and macOS Big Sur natively support DNS-over-HTTPS and DNS-over-TLS. However, it's not that simple to configure them — you need to install a special "configuration profile" for that. 🤯 In order to make things easier, AdGuard Home can generate these configuration profiles for you. Just head to "Setup Guide" -> "DNS Privacy" and scroll to iOS.
Binary transparency
AdGuard Home binaries are now signed with our GPG key and you can now easily verify that they really come from us: https://github.com/AdguardTeam/AdGuardHome/wiki/Verify-Releases
Other improvements
Allow entering comments to the Upstreams box: #2083
Load upstreams list from a file: #1680
Add ARMv8 to future releases, potentially append a v8 binary to the most recent non-beta release: #2125
Redesign query logs block/unblock buttons: #2050
Treat entries starting with "/" as "://" under specific circumstances: #1950
Use "Null IP" instead of NXDOMAIN by default: #1914
Bootstrap with TCP upstreams: #1843
Add block and unblock buttons to 'check the filtering' result: #1734
ipset feature support: #1191
Add Belarusian and Chinese Traditional HK languages: #2106
Add new language: en-silk: #1796
Use DOH or DOT as bootstrap: #960
Fixed
Reverse lookups return empty answers for hosts from /etc/hosts: #2085
Static lease hostnames are overridden by client-identifier: #2040
Query log doesn't display name for blocked services: #2038
Custom filter editor works with delay: #1657
Incorrect link address: #2209
Smartphone compatible design for user interface: #2152
Misleading information during service installation: #2128
Remove the limit on cache-min-ttl, 3600: #2094
Cannot change minimum TTL override in UI: #2091
Optical Issue on mobile phone: #2090
Setting a large DNS Cache Size in the Web GUI will exceed the unit32 range.: #2056
Clients requests aren't counted properly: #2037
Publish privacy policy on front page (README.md): #1960
Sorting various IP Address Columns in the UI (eg in dhcp static leases) does not sort correctly. They are treated as strings instead of numeric.: #1877
Requests count for clients with CIDR IP addresses: #1824



