AdGuard Home 0.107.76


Veröffentlicht am: 21. Mai 2026
Es heißt ja: Repariere nichts, was nicht kaputt ist. Aber was, wenn es das eben doch ist? Zum Beispiel, weil der Cache beim letzten Update unbeabsichtigt beschädigt wurde. Genau für solche Fälle sind Hotfixes da! Bitte installieren Sie das heutige Update, um den Cache in Ihrem AdGuard Home zu reparieren.
AdGuard Home 0.107.75


Veröffentlicht am: 19. Mai 2026
🔒 Dieses Update bringt AdGuard Home ein starkes Sicherheits-Upgrade — quasi wie neue Schlösser und doppelt verriegelte Türen.
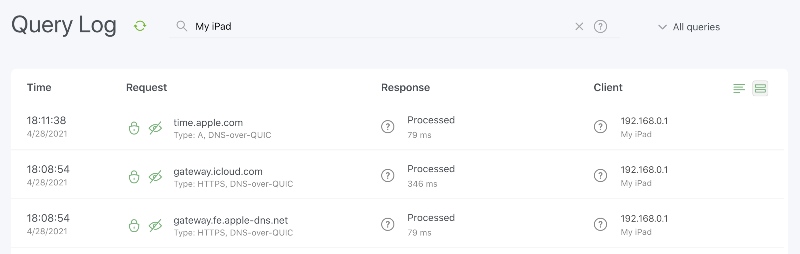
Wir haben eine kritische Sicherheitslücke bei DNS-over-QUIC und DNS-over-HTTPS behoben, die Ihre DNS-Privatsphäre gefährden konnte. Die Lücke ist geschlossen. Ihr verschlüsselter Datenverkehr läuft wieder durch einen rundum geschützten Tunnel.
Zudem haben wir Go auf die neueste Version aktualisiert, um bekannte Sicherheitslücken in den Bibliotheken zu beseitigen.
AdGuard Home 0.107.74


Veröffentlicht am: 16. April 2026
Wie bei allem im Leben gilt: Das Besondere sticht nur deshalb hervor, weil es sich vom Alltäglichen abhebt. Ohne die Routine gäbe es keine Highlights.
… Lange Rede, kurzer Sinn: Dieses Update für AdGuard Home ist genau das — unser „Alltägliches“. Wir haben uns auf Bugfixes und Sicherheit konzentriert, um das Fundament zu stärken, damit sich das nächste große Feature wieder so richtig besonders anfühlt.
AdGuard Home 0.107.73


Veröffentlicht am: 10. März 2026
Wichtiges Sicherheits-Update: Wir haben eine schwerwiegende Lücke geschlossen. Diese hätte es ermöglichen können, die Anmeldung zu umgehen und vollen Zugriff auf AdGuard Home zu erhalten — auch ohne gültige Zugangsdaten. Wir raten Ihnen, AdGuard Home umgehend zu aktualisieren.
AdGuard Home 0.107.72


Veröffentlicht am: 25. Februar 2026
Das erste Release des Jahres ist immer wichtig, da es den Ton für die kommenden Monate setzt 📆
Das Jahr 2026 beginnt zwar nicht mit einem großen Knall, aber es bietet eine solide Mischung: eine neue Methode zur Verwaltung von TLS-Zertifikatsaktualisierungen, einige kleinere neue Funktionen, ein paar Konfigurationsänderungen, wichtige Bugfixes und das übliche Sicherheitsupdate.
Bleiben Sie dran — weitere Highlights folgen!
AdGuard Home 0.107.69


Veröffentlicht am: 30. Oktober 2025
AdGuard Home v0.107.69 ist da — ein kleiner Zwischenstopp, um zwei hartnäckige Fehler zu beheben, die sich eingeschlichen hatten. Neue Funktionen gibt es diesmal nicht, aber alles sollte jetzt etwas reibungsloser laufen — die Bugs wurden hinauskomplimentiert.
AdGuard Home 0.107.68


Veröffentlicht am: 23. Oktober 2025
Lassen Sie uns das Übliche zuerst erledigen: Wir haben einige Sicherheitsupdates durchgeführt, wie immer, und diesmal sogar ohne Fehlerbehebungen, zum Guten oder zum Schlechten. Aber lassen Sie uns zum Wesentlichen kommen: eine neue Option zum Aktivieren und Deaktivieren von DNS-Umschreibregeln 🚦
Dies war eine der früheren Funktionsanfragen, und wir freuen uns, diese nun endlich umzusetzen. Sie können DNS-Umschreibregeln entweder alle auf einmal aktivieren oder deaktivieren oder dies für einzelne Umschreibungen tun — entweder durch Bearbeiten von YAML-Dateien oder über die Benutzeroberfläche.
AdGuard Home 0.107.66


Veröffentlicht am: 15. September 2025
Sie können die beste Software der Welt haben, aber wenn Sie nicht darauf zugreifen können, ist sie praktisch nutzlos. Deshalb haben wir im heutigen Update ein paar Authentifizierungsfehler behoben – so können Sie sich immer einloggen und AdGuard Home in vollem Umfang nutzen. Dazu kommen die üblichen Sicherheitsupdates und ein paar kleine Änderungen — fertig ist Version v0.107.66! 🙌
AdGuard Home 0.107.64


Veröffentlicht am: 29. Juli 2025
Anders als bei Hühnern und Eiern kommen bei Bugs und Bugfixes leider immer zuerst die Bugs. Zumindest gibt es jetzt ein neues Update, das sie alle behebt! 🥚🐔
Heute haben wir Bugfixes für jeden Geschmack: Sicherheits-Bugfixes, Bugfixes für Cache-Antworten-TTL und sogar Bugfixes für DNSCrypt-Zertifikate. Und Sie müssen sich nicht einmal entscheiden — mit dieser neuen Version von AdGuard Home können Sie alle haben.
AdGuard Home 0.107.63


Veröffentlicht am: 30. Juni 2025
Manchmal braucht es keine großen Neuerungen — schon kleine Verbesserungen und Bugfixes sorgen für mehr Stabilität 🔩
AdGuard Home 0.107.62


Veröffentlicht am: 29. Mai 2025
In diesem Update haben wir unter anderem den Fehler behoben, der dazu führte, dass Regeln mit dem
client-Modifikator nicht mehr funktionierten.Außerdem haben wir die Sicherheit von AdGuard Home verbessert, indem wir die Go-Version aktualisiert und einige Sicherheitslücken geschlossen haben, wie üblich.
AdGuard Home 0.107.60


Veröffentlicht am: 17. April 2025
Wenn Sie diese Release Notes lesen, dann gehören Sie eindeutig zur Kategorie „Power-User“ von AdGuard Home — denn dieses Update ist definitiv kein Feuerwerk an neuen Features. Es gibt keine spektakulären Neuerungen, dafür aber Patches für Go-Sicherheitslücken, ein paar UI- und Docker-Updates sowie einige Bugfixes.
AdGuard Home 0.107.59


Veröffentlicht am: 21. März 2025
Dieser Hotfix behebt den Fehler, der mit dem letzten Update auftrat und die Eingabe in das Suchfeld des Abfrageprotokolls verhinderte. Gleichzeitig haben wir auch die fehlerhafte Funktion des Client-Modifikators korrigiert.
Dankeschön
Ein besonderer Dank geht an unser Community-Team @AdguardTeam/community-moderators und an alle, die uns beim Melden von Problemen, Prüfen, Übersetzen und Testen dieser Version unterstützt haben!
AdGuard Home 0.107.58


Veröffentlicht am: 20. März 2025
Hier ist eine philosophische Frage für Sie: Wenn ein Release mehr Bugfixes als üblich enthält, ist das ein Fortschritt oder eher ein Rückschritt? 🤔
Zum Glück konzentrieren wir uns auf die Entwicklung und nicht auf die Lösung philosophischer Dilemmata. Daher überlassen wir diese Gedankenspiele denjenigen, die mehr Weisheit besitzen als wir. Was wir jedoch sicher sagen können, sind die Fakten: In diesem Update haben wir mehrere Fehler behoben und eine nützliche neue Funktion hinzugefügt, die wir Ihnen gerne genauer vorstellen möchten.
Ein verbessertes Tool zur DNS-Anfrageüberprüfung
Wenn Sie es mit Ihrer Privatsphäre und der Bekämpfung von Werbung ernst meinen, dann haben Sie sicherlich viele Regeln im Einsatz, sowohl aus Filterlisten als auch aus eigenen Regeln. Um Ihnen die Anpassung Ihres Filterarsenals zu erleichtern, haben wir das bestehende Tool erweitert. Ab jetzt können Sie den DNS-Datensatztyp und einen bestimmten Client nach IP-Adresse oder ClientID angeben, um schnell zu überprüfen, ob eine Anfrage blockiert wird. Geben Sie einfach die gewünschten Informationen ein und sehen Sie die entsprechenden Regeln. Und als Bonus: Sie können jede Domain direkt wieder entsperren. Viel Spaß beim Blockieren!
AdGuard Home 0.107.57


Veröffentlicht am: 21. Februar 2025
Das Jahr 2025 hat gerade erst begonnen, aber einige von uns brauchen jetzt schon ein Timeout 🕙 Apropos Timeout: In der neuen Version haben wir neben einigen Fehlerbehebungen und Sicherheitsupdates die Möglichkeit hinzugefügt, das Upstream-Timeout direkt in der Web-UI festzulegen.
AdGuard Home 0.107.56


Veröffentlicht am: 24. Januar 2025
Wir legen im neuen Jahr richtig los und starten mit diesem kleinen Update. 🏃 Es enthält ein paar Bugfixes, eine neue API und eine aktualisierte Go-Version, um einige Schwachstellen zu beseitigen.
AdGuard Home 0.107.55


Veröffentlicht am: 12. Dezember 2024
Dieses Release behebt einen Fehler, der einige Windows-Installationen beeinträchtigt hat. Außerdem haben wir einige Schwachstellen mit der neuesten Version von Go behoben und uns um einige Lecks gekümmert 🚰
AdGuard Home 0.107.54


Veröffentlicht am: 6. November 2024
Dieses AdGuard Home-Update ist besonders wichtig für alle, die Windows verwenden. Wir haben die notwendigen Sicherheitsverbesserungen für Windows vorgenommen, für die in der letzten Version keine Zeit war. Bei AdGuard Home-Updates ist aber immer etwas für alle dabei: Die Filter funktionieren jetzt besser, und natürlich haben wir auch eine ganze Reihe von Fehlern behoben.
AdGuard Home 0.107.53


Veröffentlicht am: 3. Oktober 2024
Wir haben uns angewöhnt, das nächste Update von AdGuard Home ein paar Monate aufzuschieben. Aber das hatte einen guten Grund: Dank der Community (ein großes Dankeschön an alle! 🙏) haben wir zwei Sicherheitslücken entdeckt und an deren Behebung gearbeitet. Das Testen der Lösungen hat etwas länger gedauert als geplant, aber wir setzen auf Qualität vor Schnelligkeit.
Glücklicherweise geht es nicht nur darum, Sicherheitslücken zu schließen und Fehler zu beheben — wir haben auch einige Verbesserungen vorgenommen. So haben wir beispielsweise die Unterstützung der 64-Bit RISC-V-Architektur hinzugefügt und die Ecosia-Suchmaschine in Sichere Suche integriert. Das vollständige Änderungsprotokoll findet ihr weiter unten.
AdGuard Home 0.107.52


Veröffentlicht am: 4. Juli 2024
In dieser Version haben wir eine Reihe von Fehlern behoben, das Frontend auf TypeScript migriert und die Frontend-Bibliotheken aktualisiert. Jetzt sollte das Coden für uns einfacher und AdGuard Home für Sie noch bequemer sein.
AdGuard Home 0.107.51


Veröffentlicht am: 6. Juni 2024
Kleines Update zur Behebung von Fehlern und Erhöhung der Sicherheit. Wir arbeiten an neuen Funktionen für zukünftige Versionen.
AdGuard Home 0.107.50


Veröffentlicht am: 24. Mai 2024
Beim letzten Update von AdGuard Home gab es leider Probleme: Einige wenige Nutzer:innen konnten AdGuard Home gar nicht starten. Daher veröffentlichen wir diesen Hotfix.
AdGuard Home 0.107.49


Veröffentlicht am: 21. Mai 2024
Der Sommer naht und verspricht Wärme für alle, auch für die Bugs, die unter Steinen hervorkriechen, um die Sonne zu genießen 🌞. Hier ist ein Patch, der sicherstellt, dass diese Bugs nicht in die Nähe von AdGuard Home kommen.
AdGuard Home 0.107.48


Veröffentlicht am: 5. April 2024
Nach dem letzten Update war es gesperrten Benutzer:innen möglich, DNS-Anfragen über verschlüsselte Protokolle zu stellen. Dieses Verhalten war natürlich nicht beabsichtigt und wird mit diesem Hotfix behoben.
Wir werden unser Bestes tun, um solche Fehler in Zukunft zu vermeiden.
AdGuard Home 0.107.47


Veröffentlicht am: 4. April 2024
Wir haben ein weiteres Update veröffentlicht, um die Sicherheit zu verbessern. Diesmal haben wir auch Probleme mit der Zeitzonenauswahl und einige andere ärgerliche Fehler behoben
AdGuard Home 0.107.46


Veröffentlicht am: 20. März 2024
Wie beim letzten Release versprochen, bringt diese Version Qualitätsverbesserungen und Bugfixes 🔧.
AdGuard Home 0.107.45


Veröffentlicht am: 7. März 2024
Dies ist ein kleines Release, das ein Sicherheitsupdate, einige Fehlerbehebungen und eine kleine neue Funktion enthält. Mehr kommt bald!
AdGuard Home 0.107.44


Veröffentlicht am: 6. Februar 2024
Wenn man seine Arbeit gut macht, merkt es niemand. Wir hoffen, dass dies wirklich der Fall ist, denn das heutige Update wird Sie nicht mit neuen Funktionen überraschen. Stattdessen „ölen wir das Getriebe“ mit kleineren Änderungen und Behebungen 🔧.
AdGuard Home 0.107.43


Veröffentlicht am: 11. Dezember 2023
Everybody needs something to keep themselves warm during the cold winter days ❄️. Many people opt for hot coffee ☕ or hot chocolate, but we at AdGuard prefer hotfixes 🔥.
AdGuard Home 0.107.42


Veröffentlicht am: 7. Dezember 2023
As the winter holidays approach, many of us begin to think about what gifts we will give and receive 🎁. With AdGuard, the holidays come early: we decided not to wait too long and present you with this new version of AdGuard Home today!
Among the long-awaited features in this release are the option to enable caching for persistent clients with custom DNS upstream configuration and the option to disable plain DNS for better security.
AdGuard Home 0.107.41


Veröffentlicht am: 13. November 2023
Wie der Wechsel der Jahreszeiten 📆 sind Fehler unvermeidlich. In dieser Version haben wir nicht nur einige davon behoben, sondern auch neue Funktionen hinzugefügt, die die Konfiguration von AdGuard Home erleichtern und Ihr Gerät vor DDoS-Angriffen schützen.
AdGuard Home 0.107.40


Veröffentlicht am: 18. Oktober 2023
Haben Sie Angst vor lästigen Fehlern beim Surfen? Zum Glück wurden sie in diesem Hotfix behoben!
AdGuard Home 0.107.39


Veröffentlicht am: 11. Oktober 2023
Obwohl die gruselige Saison schon vor der Tür steht 🎃, zögern wir nicht, eine neue Version mit neuen Funktionen und ein paar Fehlerbehebungen zu veröffentlichen!
AdGuard Home 0.107.38


Veröffentlicht am: 11. September 2023
Releases sind wie Obst: Wenn der Apfel gut schmeckt, ist es wahrscheinlich, dass irgendwo ein Bug versteckt ist. Es stellte sich heraus, dass unsere vorherige Version sehr lecker war! In diesem Hotfix wurden nun alle verbleibenden Fehler behoben.
AdGuard Home 0.107.37


Veröffentlicht am: 9. September 2023
Der Sommer ist gekommen und gegangen und hat eine reichliche Ernte von lang ersehnten Funktionen und Verbesserungen hinterlassen, garniert mit einer Portion Fehlerbehebungen.
Pausenplan für die Dienstblockierung
Nutzer:innen können nun den Dienstblockierungsfilter individuell anpassen. Zum Beispiel können Sie soziale Netzwerke den ganzen Tag über blockieren, sich aber 30 Minuten nach der Arbeit erlauben.
Wir freuen uns, dass wir die Funktion endlich in der Weboberfläche vorstellen können, obwohl sie schon seit einigen Monaten in der internen Entwicklung ist.
Fallback-Server
Eine weitere lang erwartete Funktion — die Fallback-Server — kommt zum Einsatz, wenn die primären Upstream-DNS-Server nicht erreichbar sind.
Die Syntax ist dieselbe wie bei der Eingabe im Upstream-Server, so dass Sie verschiedene Fallback-Server für verschiedene Domains festlegen können.
Upstream-Statistiken
Eine weitere nützliche Funktion im Zusammenhang mit DNS-Upstreams sind die neuen Upstream-Statistiken, die auf dem Dashboard angezeigt werden. Dadurch können Nutzer:innen ganz einfach erkennen, welche Upstreams schneller sind als andere und welche am meisten genutzt werden.
Danksagungen
Ein besonderer Dank geht an unseren Open-Source-Beitragenden @ssrahul96 sowie an alle, die Probleme gemeldet und überprüft, Übersetzungen hinzugefügt und uns bei der Testung dieser Version geholfen haben!
AdGuard Home 0.107.36


Veröffentlicht am: 2. August 2023
Kleines Update zur Behebung von Fehlern und Erhöhung der Sicherheit. Wir arbeiten an neuen Funktionen für zukünftige Versionen.
AdGuard Home 0.107.35


Veröffentlicht am: 26. Juli 2023
In der vorherigen Version haben wir die Aktualisierung von Filterregeln optimiert und in einigen Fällen sogar eine bis zu dreifache Geschwindigkeit erreicht. Allerdings erwies sich der neue Algorithmus als zu streng. Deswegen haben wir in dieser Version die Validierungen gelockert, während wir die Optimierung für typische Filterregel-Listen beibehalten haben 🏎️
Wie immer wurden auch in dieser Version weitere kleinere Fehler behoben.
AdGuard Home 0.107.34


Veröffentlicht am: 12. Juli 2023
Mit dieser Version wurde die Sicherheit von AdGuard Home verbessert und ein paar größere Probleme behoben.
Safe Browsing and CPU spikes
Back in June we released a security update to AdGuard Home with a few bug fixes. Ironically, it brought about another bug. Safe Browsing and Parental Control weren't working properly since then, which in some cases led to lowered performance, random crashes, and huge CPU spikes.
It took us an entire month to get to the bottom of this, and it certainly would have taken even longer if not for the awesome community members: @bigwookie, @TheCableGuy99, and others. It turned out that “The Big Bug” was, in fact, three smaller bugs in a trenchcoat. And they were all mercilessly dealt with in this update.
Docker HEALTHCHECK
Docker users should note that the Docker
HEALTHCHECK mechanism has been removed, since it was causing a lot of issues, especially when used with Podman and other popular Docker tools.Acknowledgements
A special thanks to our open-source contributor, @Jiraiya8, as well as to everyone who filed and inspected issues, added translations, and helped us test this release!
AdGuard Home 0.107.33


Veröffentlicht am: 3. Juli 2023
Bugs need to be fixed, and that's just what we did in this release 🔧. Besides that, we've been working on internal improvements that will make it easier to add new features in future releases.
AdGuard Home 0.107.32


Veröffentlicht am: 13. Juni 2023
A hotfix release to fix a major issue in the previous release.
AdGuard Home 0.107.31


Veröffentlicht am: 8. Juni 2023
A hotfix release to fix two major issues in the previous release.
AdGuard Home 0.107.30


Veröffentlicht am: 7. Juni 2023
A small bugfix and security release. We are working on new features in future releases.
AdGuard Home 0.107.29


Veröffentlicht am: 18. April 2023
Unser letztes Release fand am Internationalen Tag der bemannten Raumfahrt statt, aber es scheint, dass unsere Rakete nicht reibungslos abheben konnte. In dieser Version beheben wir ein paar lästige Fehler und verbessern die Funktion zum Ignorieren des Clients.
AdGuard Home 0.107.28


Veröffentlicht am: 12. April 2023
Ein großes Update mit vielen neuen Funktionen ist endlich da! Unter anderem möchten wir einige bemerkenswerte Änderungen hervorheben, auf die Sie vielleicht gewartet haben.
Pause für globalen Schutz
Sie können nun den Schutz für 30 Sekunden oder den ganzen Tag unterbrechen. Dies ist nützlich, wenn eine fälschlicherweise blockierte Website zugreifen oder AdGuard Home vorübergehend deaktivieren möchten, ohne es komplett abzuschalten.
 Sobald die Pausenzeit abgelaufen ist, schaltet AdGuard Home den Schutz wieder ein.
Sobald die Pausenzeit abgelaufen ist, schaltet AdGuard Home den Schutz wieder ein.
 Sobald die Pausenzeit abgelaufen ist, schaltet AdGuard Home den Schutz wieder ein.
Sobald die Pausenzeit abgelaufen ist, schaltet AdGuard Home den Schutz wieder ein.Bessere Steuerung der Sicheren Suche
Außerdem können Sie nun die Sichere Suche präziser einstellen, indem Sie diese für bestimmte Dienste ein- oder ausschalten — zum Beispiel, Google, Bing oder YouTube.
 Das Gleiche können Sie für jeden Client tun. Eine weitere kleinere Verbesserung der Sicheren Suche ist die bessere Unterstützung von IPv6-Adressen.
Das Gleiche können Sie für jeden Client tun. Eine weitere kleinere Verbesserung der Sicheren Suche ist die bessere Unterstützung von IPv6-Adressen.
 Das Gleiche können Sie für jeden Client tun. Eine weitere kleinere Verbesserung der Sicheren Suche ist die bessere Unterstützung von IPv6-Adressen.
Das Gleiche können Sie für jeden Client tun. Eine weitere kleinere Verbesserung der Sicheren Suche ist die bessere Unterstützung von IPv6-Adressen.
AdGuard Home 0.107.27


Veröffentlicht am: 5. April 2023
Bei dieser Version handelt es sich um Sicherheit und Fehlerbehebungen. Wir haben nur die Programmiersprache Go aktualisiert. Größere Änderungen folgen in den nächsten Updates.
AdGuard Home 0.107.26


Veröffentlicht am: 9. März 2023
Das heutige Update enthält neue Optionen für die Konfiguration ausgehender Anfragen, eine neue Option zur Ablehnung von Anfragen nach ihrem Typ sowie zahlreiche Fehlerbehebungen.
AdGuard Home 0.107.25


Veröffentlicht am: 21. Februar 2023
Wir haben diesen Hotfix veröffentlicht, um fatale Fehler bei der Verwendung von unverschlüsseltem DNS-over-HTTPS zu verhindern. Diese Fehler traten bei Benutzer:innen auf, die AdGuard Home hinter einem Reverse-HTTP-Proxy konfiguriert haben.
AdGuard Home 0.107.24


Veröffentlicht am: 16. Februar 2023
Es kann schwierig sein, redselige Kolleg:innen im realen Leben zu ignorieren 🤫. Zum Glück gibt es in der digitalen Welt mehr Möglichkeiten. Die neue Version von AdGuard Home bietet die Möglichkeit, bestimmte Hostnamen aus dem Anfrageprotokoll und den Statistiken auszuschließen, was bei Geräten und Apps helfen kann, die gerne zu viel reden.
AdGuard Home 0.107.23


Veröffentlicht am: 1. Februar 2023
Schriftarten! Farben! Schaltflächen! Jeder diskutiert gerne über das Design einer Benutzeroberfläche, aber noch mehr freuen wir uns, wenn wir unseren Benutzer:innen Fehlerbehebungen und neue Funktionen zur Verfügung stellen können 🚢.
Neben den Anpassungen am dunklen Thema enthält diese Version Unterstützung für den DNS64-Standard, einige neue blockierbare Dienste sowie einige Fehlerbehebungen und interne Verbesserungen.
AdGuard Home 0.107.22


Veröffentlicht am: 19. Januar 2023
Eine Sache, die niemand in langen Nächten mag, ist eine Benutzeroberfläche, die viel zu hell ist 🔦. In dieser Version liefert AdGuard Home endlich eine der am häufigsten geforderten Funktionen: das dunkle Thema!
Das neue dunkle Thema ist derzeit noch experimentell, und es gibt da einige Mängel. Wenn Sie diese melden möchten, folgen Sie bitte den Anweisungen in Ausgabe [#5375] (https://github.com/AdguardTeam/AdGuardHome/issues/5375).
AdGuard Home 0.107.21


Veröffentlicht am: 24. Dezember 2022
Ein Hotfix zur kalten Jahreszeit
AdGuard Home 0.107.20


Veröffentlicht am: 7. Dezember 2022
Wir tun unser Bestes, um unsere Nutzer:innen zu schützen und sicherzustellen, dass sie die neuesten Sicherheitsupdates 🛡️ so bald wie möglich erhalten. Als Bonus haben wir außerdem eine Schaltfläche hinzugefügt, mit der Sie den DNS-Cache ganz einfach löschen können.
AdGuard Home 0.107.19


Veröffentlicht am: 23. November 2022
Twitter mag zwar in Flammen stehen 🔥, aber man kann trotzdem nicht so einfach von den sozialen Medien loskommen. Doch dank der Hilfe von @sandervankasteel ist es jetzt ein wenig einfacher: AdGuard Home kann jetzt einige der beliebtesten Instanzen von Mastodon blockieren. Machen Sie eine Pause vom Doomscrolling, Sie haben es sich verdient!
Wir haben auch die Kommandozeilen-Option
--update hinzugefügt, um AdGuard Home zu aktualisieren, ohne sich mit der Benutzeroberfläche auseinandersetzen zu müssen.
AdGuard Home 0.107.17


Veröffentlicht am: 2. November 2022
Despite this release appearing around Halloween, it shouldn't be spooky at all. The main novelty is that the list of services blockable with a single click is now synchronized with AdGuard DNS to make the user experience more unified across AdGuard services. We've also improved support for HTTP/3 as well as fixed a few annoying bugs.
AdGuard Home 0.107.16


Veröffentlicht am: 7. Oktober 2022
This is a security release. There are no new changes besides the update of the Go programming language version. More substantial changes are to come in the subsequent updates.
Full Changelog
Security
Go version has been updated to prevent the possibility of exploiting the CVE-2022-2879, CVE-2022-2880, and CVE-2022-41715 Go vulnerabilities fixed in Go 1.18.7.
AdGuard Home 0.107.15


Veröffentlicht am: 3. Oktober 2022
Sometimes, even a hotfix needs a hotfix. In the previous release, our mitigations turned out to be too restrictive, preventing some AdGuard Home features from working properly. In this release, we fix this along with a few other bugs.
We have also added experimental support for the HTTP/3 standard in the UI, DNS upstreams, and DNS clients!
Full Changelog
Security
As an additional CSRF protection measure, AdGuard Home now ensures that requests that change its state but have no body (such as POST /control/stats_reset requests) do not have a Content-Type header set on them #4970.
Added
Experimental HTTP/3 Support
See #3955 and the related issues for more details. These features are still experimental and may break or change in the future.
DNS-over-HTTP/3 DNS and web UI client request support. This feature must be explicitly enabled by setting the new property
dns.serve_http3 in the configuration file to true.DNS-over-HTTP upstreams can now upgrade to HTTP/3 if the new configuration file property
dns.use_http3_upstreams is set to true.Upstreams with forced DNS-over-HTTP/3 and no fallback to prior HTTP versions using the h3:// scheme.
Fixed
only application/json is allowed errors in various APIs #4970.
AdGuard Home 0.107.14


Veröffentlicht am: 29. September 2022
This is a security release. Users are encouraged to update AdGuard Home as soon as possible.
Full Changelog
Security
A Cross-Site Request Forgery (CSRF) vulnerability has been discovered. The CVE number is to be assigned. We thank Daniel Elkabes from Mend for reporting this vulnerability to us.
SameSite PolicyThe
SameSite policy on the AdGuard Home session cookies has been upgraded to Lax. Which means that the only cross-site HTTP request for which the browser is allowed to send the session cookie is navigating to the AdGuard Home domain.Users are strongly advised to log out, clear browser cache, and log in again after updating.
Removal Of Plain-Text APIs (BREAKING API CHANGE)
We have implemented several measures to prevent such vulnerabilities in the future, but some of these measures break backwards compatibility for the sake of better protection.
The following APIs, which previously accepted or returned
text/plain data, now accept or return data as JSON. All new formats for the request and response bodies are documented in openapi/openapi.yaml and openapi/CHANGELOG.md.GET /control/i18n/current_language;POST /control/dhcp/find_active_dhcp;POST /control/filtering/set_rules;POST /control/i18n/change_language.Stricter
Content-Type Checks (BREAKING API CHANGE)All JSON APIs now check if the request actually has
Content-Type set to application/json.Other Security Changes
AdGuard Home 0.107.13


Veröffentlicht am: 14. September 2022
In this hotfix release with the “lucky” patch number we have fixed a couple of issues that prevented some DHCP clients from receiving their assigned IP addresses. We've also added the new
dns.ipset_file setting, which should help users who maintain large ipsets, for example to use in firewall or VPN settings.Full Changelog
Added
The new optional
dns.ipset_file property, which can be set in the configuration file. It allows loading the ipset list from a file, just like dns.upstream_dns_file does for upstream servers #4686.Changed
The minimum DHCP message size is reassigned back to BOOTP's constraint of 300 bytes #4904.
Fixed
Panic when adding a static lease within the disabled DHCP server #4722.
AdGuard Home 0.107.12


Veröffentlicht am: 7. September 2022
What better way is there to celebrate the coming of autumn than a patch release? In this new version, we have extended and significantly improved AdGuard Home's built-in DHCP server (fixing many bugs in the process) as well as improved our service blocking feature, thanks to many contributions from the community. As always, we have also updated our tooling to make sure that we use the latest versions without any known security issues.
Full Changelog
Security
Go version was updated to prevent the possibility of exploiting the CVE-2022-27664 and CVE-2022-32190 Go vulnerabilities fixed in Go 1.18.6.
Added
New
del DHCP option which removes the corresponding option from server's response #4337. See also a Wiki page.NOTE: This modifier affects all the parameters in the response and not only the requested ones.
A new HTTP API,
GET /control/blocked_services/services, that lists all available blocked services #4535.Changed
The DHCP options handling is now closer to the [RFC 2131][rfc-2131] (#4705).
When the DHCP server is enabled, queries for domain names under
dhcp.local_domain_name not pointing to real DHCP client hostnames are now processed by filters (#4865).The internal DNS client, used to resolve hostnames of external clients and also during automatic updates, now respects the upstream mode settings for the main DNS client #4403.
Deprecated
Ports 784 and 8853 for DNS-over-QUIC in Docker images. Users who still serve DoQ on these ports are encouraged to move to the standard port 853. These ports will be removed from the
EXPOSE section of our Dockerfile in a future release.Go 1.18 support. Future versions will require at least Go 1.19 to build.
Fixed
Dynamic leases created with empty hostnames #4745.
Unnecessary logging of non-critical statistics errors #4850.
AdGuard Home 0.107.11


Veröffentlicht am: 19. August 2022
This hot summer is approaching its end, but hotfixes are still coming in! In this release, we have fixed configuration file migrations not working for people with AdGuard Home versions older than v0.107.7, as well as made a few minor improvements.
--
Full Changelog
--
Added
AdGuard Home 0.107.10


Veröffentlicht am: 17. August 2022
In this new release, we add support for the new Discovery of Designated Resolvers DDR feature, which allows clients using plain DNS to automatically switch to secure protocols. As well as an Arabic localization and fixes for a couple of rather annoying bugs.
Full Changelog
Added
AdGuard Home 0.107.9


Veröffentlicht am: 3. August 2022
Although not a lot of time has passed since the last release, this new one contains a security update, a new feature, a new platform, and some minor fixes :wrench:. It's always nice to have those!
Full Changelog
Security
Go version was updated to prevent the possibility of exploiting the CVE-2022-32189 Go vulnerability fixed in Go 1.18.5. Go 1.17 support has also been removed, as it has reached end of life and will not receive security updates.
Added
Domain-specific upstream servers test. If such test fails, a warning message is shown #4517.
windows/arm64 support #3057.
Changed
UI and update links have been changed to make them more resistant to DNS blocking.
Fixed
Go 1.17 support, as it has reached end of life.
AdGuard Home 0.107.8


Veröffentlicht am: 19. Juli 2022
Fehler entstehen ganz plötzlich, aber glücklicherweise können wir sie fast immer beheben. Und genau das haben wir in diesem Bugfix-Release getan.
Vollständiges Änderungsprotokoll
Sicherheit
Die Go-Version wurde aktualisiert, um die Möglichkeit zu verhindern, die
CVE-2022-1705, CVE-2022-32148, CVE-2022-30631 und andere Go-Schwachstellen, die in [Go 1.17.12] (https://groups.google.com/g/golang-announce/c/nqrv9fbR0zE) behoben wurden, auszunutzen.Behoben
DHCP-Lease-Validierung lässt Benutzer:innen fälschlicherweise die IP-Adresse des Gateways als Adresse des Leases zuweisen #4698.
*Updater erwartet nicht mehr einen hartkodierten Namen für die ausführbare Datei
AdGuardHome#4219.Inkonsistente Namen von Laufzeit-Clients aus Hosts-Dateien #4683.
PTR-Anfragen für von DHCP geleaste Adressen werden jetzt in Hostnamen unter
dhcp.local_domain_name aufgelöst #4699.Fehlerhafte Dienstinstallation bei OpenWrt #4677.
AdGuard Home 0.107.7


Veröffentlicht am: 19. Juli 2022
Der Sommer ist endlich da und damit auch eine neue Version von AdGuard Home!
DNS-over-QUIC: RFC 9250
Das lang erwartete DNS-over-QUIC-Protokoll ist endlich von einem Entwurf zu einem echten Standard geworden, RFC 9250. In dieser Version fügen wir Unterstützung für die endgültige Standardversion in einer rückwärtskompatiblen Weise hinzu.
Mehr Kontrolle über Upstreams
Sie können jetzt einen Upstream-Server für alle Unterdomains einer Domain angeben, während Sie die Domains selbst ausschließen. Wenn Sie zum Beispiel möchten, dass Anfragen für „server-1.example.com“ vom DNS-Server „1.1.1.1“ aufgelöst werden, aber „example.com“ von Ihrem Standard-Upstream (in diesem Beispiel „94.140.14.14“) aufgelöst wird, verwenden Sie:
94.140.14.14
[/*.example.com/]1.1.1.1Apropos Upstreams. Jetzt müssen Sie sich nicht mehr die genauen IP-Adressen der einfachen DNS-Upstreams merken. Solange Ihre Bootstrap-Server sie auflösen können, können Sie das neue Upstream-Adressschema
udp:// verwenden, um die Adressen der Upstreams automatisch aufzulösen:udp://one.one.one.one # Same as 1.1.1.1.Andere wichtige Änderungen
Die Benutzer:innen haben jetzt mehr Kontrolle darüber, wie Laufzeit-Client-Informationen gesammelt werden, einschließlich der Möglichkeit, diese Funktion vollständig zu deaktivieren.
Die EDNS-Client-Subnetzinformationen von Client-Anfragen werden jetzt auf der Seite Anfrageprotokoll angezeigt.
Wie immer bemühen wir uns, unsere Tools auf dem neuesten Stand zu halten, um sicherzustellen, dass unsere Nutzer:innen nicht auf Sicherheitslücken stoßen.
Es gibt noch viele weitere kleinere Änderungen und Fehlerbehebungen; sehen Sie sich einfach das vollständige Änderungsprotokoll unten an!
Danksagungen
Ein besonderer Dank geht an unseren Open-Source-Mitarbeiter @Lanius-collaris sowie an alle, die Probleme gemeldet und geprüft, Übersetzungen hinzugefügt und uns beim Testen dieser Version geholfen haben.
Vollständiges Änderungsprotokoll
Sicherheit
Die Go-Version wurde aktualisiert, um die Möglichkeit der Ausnutzung der CVE-2022-29526, CVE-2022-30634, CVE-2022-30629, CVE-2022-30580, und CVE-2022-29804 Sicherheitslücken zu verhindern.
Richtlinie zur Erzwingung der Passwortstärke #3503.
Hinzugefügt
Upstream-Unterstützung nur für Subdomains einer Domain #4503.
Die Möglichkeit, jede Quelle von Laufzeit-Clients separat über das Konfigurationsobjekt
clients.runtime_sources zu steuern #3020.Die Möglichkeit, die Menge der Netzwerke, die als privat gelten, durch die neue Eigenschaft
dns.private_networks in der Konfigurationsdatei anzupassen #3142.EDNS-Client-Subnetz-Informationen im Anfragedetails-Abschnitt eines Abfrageprotokollsatzes #3978.
Unterstützung für Hostnamen für einfache UDP-Upstream-Server, die das Schema
udp:// verwenden #4166.Protokolle werden nun standardmäßig unter FreeBSD und OpenBSD gesammelt, wenn AdGuard Home als Dienst installiert ist #4213.
Verändert
Unter OpenBSD verwendet das Daemon-Skript nun die empfohlene
/bin/ksh-Shell anstelle der /bin/sh-Shell #4533. Um diese Änderung anzuwenden, sichern Sie Ihre Daten und führen Sie AdGuardHome -s uninstall && AdGuardHome -s install aus.Reverse DNS hat nun eine höhere Priorität wie Quelle für die Informationen der Laufzeit-Clients als die ARP-Nachbarschaft.
Verbesserte Erkennung von Laufzeit-Clients durch belastbarere ARP-Verarbeitung #3597.
Die TTL von Antworten aus dem Cache wird jetzt auf 10 Sekunden gesenkt.
Domainspezifische private Reverse-DNS-Upstream-Server werden jetzt validiert, um nur
*.in-addr.arpa und *.ip6.arpa-Domains zuzulassen, die auf lokal versorgte Netzwerke verweisen #3381. Hinweis: Wenn Sie bereits ungültige Einträge in Ihrer Konfiguration haben, sollten Sie diese manuell entfernen, da sie im Grunde keine Auswirkungen haben.Die Filterung von Antworten erfolgt nun anhand der Datensatztypen im Antwortabschnitt von Nachrichten und nicht mehr anhand des Fragetyps #4238.
Anstatt die Information über die Erstellungszeit hinzuzufügen, verwenden die Erstellungsskripte nun die standardisierte Umgebungsvariable [
SOURCE_DATE_EPOCH][repr], um das Datum der Übergabe hinzuzufügen, von der die Binärdatei erstellt wurde #4221. Dies sollte reproduzierbare Builds für Paketbetreuer und diejenigen, die ihr eigenes AdGuard Home kompilieren, vereinfachen.Die Eigenschaft
local_domain_name befindet sich jetzt im dhcp-Objekt in der Konfigurationsdatei, um Verwechslungen zu vermeiden #3367.Die Eigenschaft
dns.bogus_nxdomain in der Konfigurationsdatei unterstützt jetzt neben IP-Adressen auch die CIDR-Notation #1730.Konfigurationsänderungen
In dieser Version hat sich die Schemaversion von 12 auf 14 geändert.
Das Objekt
clients, das in den Schemaversionen 13 und früher ein Array von tatsächlichen persistenten Clients war, besteht jetzt aus den Eigenschaften persistent und runtime_sources:# BEFORE:
'clients':
- name: client-name
# …
# AFTER:
'clients':
'persistent':
- name: client-name
# …
'runtime_sources':
whois: true
arp: true
rdns: true
dhcp: true
hosts: trueDer Wert für das Feld
clients.runtime_sources.rdns wird von der Eigenschaft dns.resolve_clients übernommen. Um diese Änderung rückgängig zu machen, entfernen Sie die Eigenschaft runtime_sources, verschieben Sie den Inhalt von persistent in die clients selbst, den Wert von clients.runtime_sources.rdns in die dns.resolve_clients und ändern Sie die schema_version zurück auf 13.Die Eigenschaft
local_domain_name, die in den Schema-Versionen 12 und früher Teil des dns-Objekts war, ist jetzt Teil des dhcp-Objekts:# BEFORE:
'dns':
# …
'local_domain_name': 'lan'
# AFTER:
'dhcp':
# …
'local_domain_name': 'lan'Um diese Änderung rückgängig zu machen, verschieben Sie die Eigenschaft zurück in das
dns-Objekt und ändern Sie die schema_version zurück auf 12.Abgelehnt
Die Option
-no-etc-hosts. Ihre Funktionalität wird nun durch die Konfigurationseigenschaft clients.runtime_sources.hosts gesteuert. v0.109.0 wird das Flag vollständig entfernen.Behoben
Anfrageprotokoll geht gelegentlich in eine Dauerschleife über
#4591.
Dienststart beim Booten auf Systemen mit SysV-init #4480.
Erkennung des Status von gestoppten Diensten auf macOS und Linux #4273.
Groß-/Kleinschreibung beachten ClientID #4542.
Langsame Anfragen zur Versionsaktualisierung, die andere HTTP-APIs unempfindlich machen #4499.
ARP-Tabellen-Aktualisierungsprozess verursacht übermäßige PTR-Anfragen #3157.
AdGuard Home 0.107.6


Veröffentlicht am: 14. April 2022
This is a small security-oriented update. This AdGuard Home version requires Go v1.17 and later to build, because older Go versions receive no further support, including security patches.
Aside from that, we've slightly updated
$dnsrewrite modifier to support the user-defined Discovery of Designated Resolvers (DDR). We are planning on continuing to make more improvements to it in the future updates, see #4463.The rest are minor changes and ever-present bugfixes.
Full Changelog
Security
User-Agent HTTP header removed from outgoing DNS-over-HTTPS requests.Go version was updated to prevent the possibility of exploiting the CVE-2022-24675, CVE-2022-27536, and CVE-2022-28327 vulnerabilities.
Added
Changed
Filtering rules with the dnsrewrite modifier that create SVCB or HTTPS responses should use ech instead of echconfig to conform with the latest drafts.
Deprecated
SVCB/HTTPS parameter name
echconfig in filtering rules with the dnsrewrite modifier. Use ech instead. v0.109.0 will remove support for the outdated name echconfig.Obsolete --no-mem-optimization option #4437. v0.109.0 will remove the flag completely.
Fixed
I/O timeout errors when checking for the presence of another DHCP server.
Network interfaces being incorrectly labeled as down during installation.
Rules for blocking the QQ service #3717.
Removed
Go 1.16 support, since that branch of the Go compiler has reached end of life and doesn't receive security updates anymore.
AdGuard Home 0.107.5


Veröffentlicht am: 14. April 2022
This is a security release. There are no new changes besides the update of the Go programming language version.
More substantial changes are to come in the subsequent updates.
Full Changelog
Security
Go version was updated to prevent the possibility of exploiting the CVE-2022-24921 vulnerability. As the CVE page is still showing “reserved” at the time of publishing, see also golang/go#51112.
AdGuard Home 0.107.4


Veröffentlicht am: 14. April 2022
A small update to fix a couple bugs and shore up some Go vulnerabilities.
More substantial changes are to come in the subsequent updates.
Full Changelog
Security
Go version was updated to prevent the possibility of exploiting the CVE-2022-23806, CVE-2022-23772, and CVE-2022-23773 vulnerabilities.
Changed
Minor UI improvements.
Fixed
AdGuard Home 0.107.3


Veröffentlicht am: 3. Februar 2022
This version contains bug fixes and cleanups 🧹. Also, there is a new minor feature: now you can rewrite responses for domains using the response code
NOERROR. Similar rules will allow to get a successful response without records, e.g.:|example.com^$dnsrewrite=NOERRORFull Changelog
Added
AdGuard Home 0.107.2


Veröffentlicht am: 12. Januar 2022
You know, it is very hard to break your bad habits. We're still struggling with one, the overwhelming need to roll out hotfixes to AdGuard Home releases 😢
Now this one is a hotfix release for a really critical CPU overconsumption bug in v0.107.1.
Please update asap and with this, we wish you happy holidays!🎄
Full Changelog
Fixed
Infinite loops when TCP connections time out (#4042).
AdGuard Home 0.107.1


Veröffentlicht am: 12. Januar 2022
In a not-futile-at-all-we-swear 😅 attempt to fix all bugs before the New Year we're rolling out a hotfix to the recent v0.107.0. Hopefully, this time we got it all right. And if not, there are still a couple of sheets left on the calendar 📆 and the mug is still half-full with lukewarm coffee ☕
Acknowledgements
A special thanks to our open-source contributors: @Aikatsui and @mdawsonuk, as well as to everyone who filed and inspected issues, added translations, and helped us test this release!
Full Changelog
Changed
The validation error message for duplicated allow- and blocklists in DNS settings now shows the duplicated elements (#3975).
Fixed
ipset initialization bugs (#4027).Legacy DNS rewrites from a wildcard pattern to a subdomain (#4016).
Service not being stopped before running the
uninstall service action (#3868).Broken
reload service action on FreeBSD.Legacy DNS rewrites responding from upstream when a request other than
A or AAAA is received (#4008).Panic on port availability check during installation (#3987).
Incorrect application of rules from the OS's hosts files (#3998).
AdGuard Home 0.107.0


Veröffentlicht am: 12. Januar 2022
We've had some big AdGuard Home updates in the past, but this one is to top them all. It's been brewing for almost eight months! 🙀 So no wonder there's heaps upon heaps of new features, improvements, bugfixes, and other changes. We'd better start listing them ASAP, or else we'll be risking missing the New Year's fireworks 🎆 🥂
Native Apple Silicon support
There's no shortage of killer features in this changelog, but this one takes the cake as the biggest of them all, without any doubt. You won't have to resort to Rosetta or any such solutions anymore if you want to configure AdGuard Home on a Mac with a Silicon chip.
RFC 9000 support In DNS-over-QUIC
It's not quite over nine thousand, but it'll do. The IETF has formalized QUIC this year with RFC 9000, and DNS-over-QUIC protocol finally supports it. If you haven't tried DoQ yet, consider this a sign.
$dnsrewrite rules and other DNS rewrites will now be applied even when protection is disabled (#1558)
Another popular demand. This change only makes sense, as DNS rewrites often carry a different purpose than simply blocking ads or trackers. You still can disable them by opening the admin panel, going to Settings → General settings, and removing the check mark from the Block domains using filters and hosts files box.
Note: rules contained in system hosts files (e.g.
/etc/hosts) now have higher priority. This may result in more rewrites appearing in your Query log. If some of these rewrites are invalid, remove the corresponding lines from your hosts files or comment them out.DNS-over-HTTPS queries now use the real IP address of the client instead of the address of the proxy (#2799)
Note that this change concerns only those proxies that you've added to the list of "Trusted proxies", otherwise it would be a major security risk. We wouldn't want anything of that sort to happen to you! 🙅♀️ Right now
trusted_proxies can only be configured in AdGuardHome.yaml, but that might change in the future.Optimistic DNS cache (#2145)
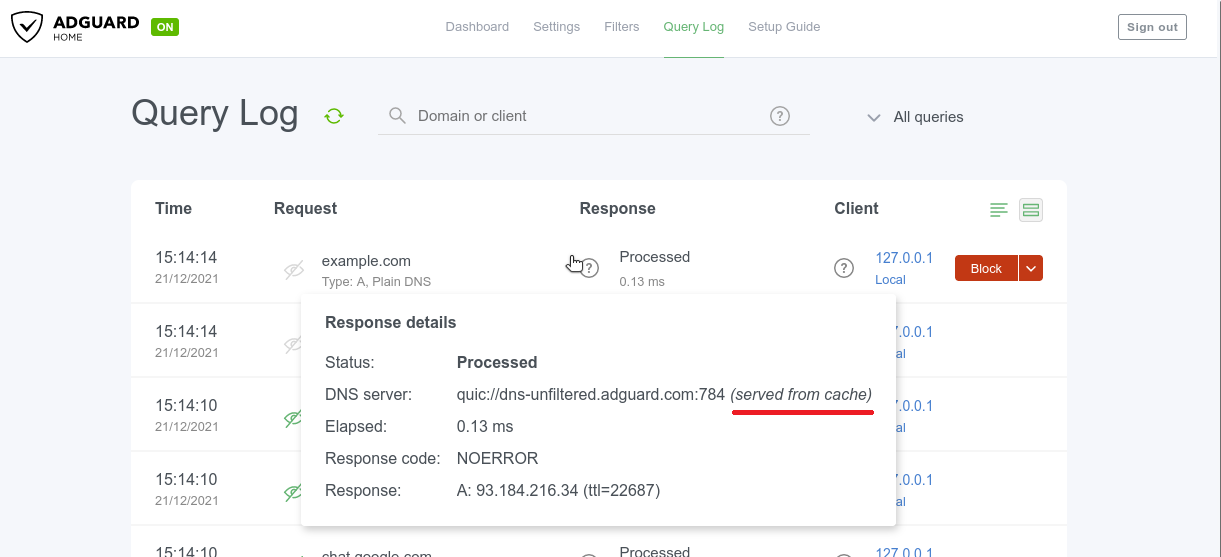
To reduce latency you may make AdGuard Home respond from the cache even when the stored entry is expired, while trying to refresh them at the same time🔄 This checkbox is located in Settings → DNS settings → DNS cache configuration and it's not ticked by default. Responses made from DNS cache are marked with a special label in the Query log.
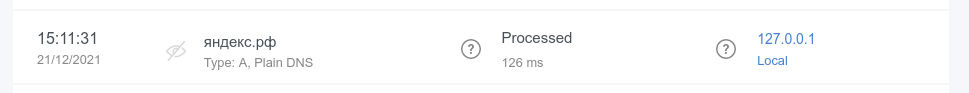
Query log search now supports internationalized domains (#3012)
Internationalized domain names (IDNAs) are domain names that contain symbols in non-Latin script/alphabet, such as
яндекс.рф or ουτοπία.δπθ.gr, for example. Previously, they were being converted to Unicode in AG Home Query log (xn--d1abqjx3f.xn--p1ai and xn--kxae4bafwg.xn--pxaix.gr in our examples), which is a detriment in most cases. Now IDNAs are displayed as is, and you can search for them without resorting to Unicode.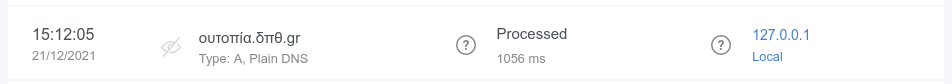
Acknowledgements
A special thanks to our open-source contributors: @Aikatsui, @anbraten, @bruvv, @DandelionSprout, @fvdm, @hnefatl, @markhicken, @p27877, and @systemcrash, as well as to everyone who filed and inspected issues, added translations, and helped us test this release! 🙏
Full Changelog
Added
Upstream server information for responses from cache (#3772). Note that old log entries concerning cached responses won't include that information.
Finnish and Ukrainian translations.
Setting the timeout for IP address pinging in the "Fastest IP address" mode through the new
fastest_timeout field in the configuration file (#1992).Static IP address detection on FreeBSD (#3289).
Optimistic cache (#2145).
New possible value of
6h for querylog_interval setting (#2504).Blocking access using client IDs (#2624, #3162).
source directives support in /etc/network/interfaces on Linux (#3257).RFC 9000 support in DNS-over-QUIC.
Completely disabling statistics by setting the statistics interval to zero (#2141).
The ability to completely purge DHCP leases (#1691).
Settable timeouts for querying the upstream servers (#2280).
Configuration file parameters to change group and user ID on startup on Unix (#2763).
Experimental OpenBSD support for AMD64 and 64-bit ARM CPUs (#2439, #3225, #3226).
Support for custom port in DNS-over-HTTPS profiles for Apple's devices (#3172).
darwin/arm64 support (#2443).freebsd/arm64 support (#2441).Output of the default addresses of the upstreams used for resolving PTRs for private addresses (#3136).
Detection and handling of recurrent PTR requests for locally-served addresses (#3185).
The ability to completely disable reverse DNS resolving of IPs from locally-served networks (#3184).
New flag
--local-frontend to serve dynamically changeable frontend files
from disk as opposed to the ones that were compiled into the binary.Changed
Port bindings are now checked for uniqueness (#3835).
The DNSSEC check now simply checks against the AD flag in the response (#3904).
Client objects in the configuration file are now sorted (#3933).
Responses from cache are now labeled (#3772).
Better error message for ED25519 private keys, which are not widely supported (#3737).
Cache now follows RFC more closely for negative answers (#3707).
$dnsrewrite rules and other DNS rewrites will now be applied even when the protection is disabled (#1558).DHCP gateway address, subnet mask, IP address range, and leases validations (#3529).
The
systemd service script will now create the /var/log directory when it doesn't exist (#3579).Items in allowed clients, disallowed clients, and blocked hosts lists are now required to be unique (#3419).
The TLS private key previously saved as a string isn't shown in API responses anymore (#1898).
Better OpenWrt detection (#3435).
DNS-over-HTTPS queries that come from HTTP proxies in the
trusted_proxies list now use the real IP address of the client instead of the address of the proxy (#2799).Clients who are blocked by access settings now receive a
REFUSED response when a protocol other than DNS-over-UDP and DNSCrypt is used.querylog_interval setting is now formatted in hours.Query log search now supports internationalized domains (#3012).
Internationalized domains are now shown decoded in the query log with the original encoded version shown in request details (#3013).
When /etc/hosts-type rules have several IPs for one host, all IPs are now returned instead of only the first one (#1381).
The setting
rlimit_nofile is now in the os block of the configuration file, together with the new group and user settings (#2763).Permissions on filter files are now
0o644 instead of 0o600 (#3198).Configuration Changes
In this release, the schema version has changed from
10 to 12.Parameter
dns.querylog_interval, which in schema versions 11 and earlier used to be an integer number of days, is now a string with a human-readable duration:# BEFORE:
'dns':
# …
'querylog_interval': 90
# AFTER:
'dns':
# …
'querylog_interval': '2160h'To rollback this change, convert the parameter back into days and change the
schema_version back to 11.Parameter
rlimit_nofile, which in schema versions 10 and earlier used to be on the top level, is now moved to the new os object:# BEFORE:
'rlimit_nofile': 42
# AFTER:
'os':
'group': ''
'rlimit_nofile': 42
'user': ''To rollback this change, move the parameter on the top level and change the
schema_version back to 10.Deprecated
Go 1.16 support. v0.108.0 will require at least Go 1.17 to build.
Fixed
EDNS0 TCP keepalive option handling (#3778).
Rules with the
$denyallow modifier applying to IP addresses when they shouldn't (#3175).The length of the EDNS0 client subnet option appearing too long for some upstream servers (#3887).
Invalid redirection to the HTTPS web interface after saving enabled encryption settings (#3558).
Incomplete propagation of the client's IP anonymization setting to the statistics (#3890).
Incorrect
$dnsrewrite results for entries from the operating system's hosts file (#3815).Matching against rules with
| at the end of the domain name (#3371).Incorrect assignment of explicitly configured DHCP options (#3744).
Occasional panic during shutdown (#3655).
Addition of IPs into only one as opposed to all matching ipsets on Linux (#3638).
Removal of temporary filter files (#3567).
Panic when an upstream server responds with an empty question section (#3551).
9GAG blocking (#3564).
DHCP now follows RFCs more closely when it comes to response sending and option selection (#3443, #3538).
Occasional panics when reading old statistics databases (#3506).
reload service action on macOS and FreeBSD (#3457).Inaccurate using of service actions in the installation script (#3450).
Client ID checking (#3437).
Discovering other DHCP servers on
darwin and freebsd (#3417).Switching listening address to unspecified one when bound to a single specified IPv4 address on Darwin (macOS) (#2807).
Incomplete HTTP response for static IP address.
DNSCrypt queries weren't appearing in query log (#3372).
Wrong IP address for proxied DNS-over-HTTPS queries (#2799).
Domain name letter case mismatches in DNS rewrites (#3351).
Conflicts between IPv4 and IPv6 DNS rewrites (#3343).
Letter case mismatches in
CNAME filtering (#3335).Occasional breakages on network errors with DNS-over-HTTP upstreams (#3217).
Errors when setting static IP on Linux (#3257).
Treatment of domain names and FQDNs in custom rules with
$dnsrewrite that use the PTR type (#3256).Redundant hostname generating while loading static leases with empty hostname (#3166).
Domain name case in responses (#3194).
Custom upstreams selection for clients with client IDs in DNS-over-TLS and DNS-over-HTTP (#3186).
Incorrect client-based filtering applying logic (#2875).
Removed
Go 1.15 support.
AdGuard Home 0.106.3


Veröffentlicht am: 19. Mai 2021
More! More bugfixes! 🧟♀️
But this time, for a change, there's a couple of new minor features to go with them. Hope you don't mind 🤷♂️
A special thanks to our open-source contributor, @ashishwt, as well as to everyone who filed and inspected issues, added translations, and helped us to test this release!
Added
Changed
Add microseconds to log output.
Fixed
Intermittent "Warning: ID mismatch" errors #3087.
Error when using installation script on some ARMv7 devices #2542.
Local PTR request recursion in Docker containers #3064.
Ignoring client-specific filtering settings when filtering is disabled in general settings #2875.
Disallowed domains are now case-insensitive #3115.
Other minor fixes and improvements.
AdGuard Home 0.106.2


Veröffentlicht am: 19. Mai 2021
It's not Friday? Not a problem! We defy the tradition of Friday hotfixes by rushing another one out a day earlier 🙌
A special thanks to our open-source contributor, @jankais3r, as well as to everyone who filed issues, added translations, and helped us to test this release!
Fixed
AdGuard Home 0.106.1


Veröffentlicht am: 19. Mai 2021
We had a release a couple days ago. You all knew it would come to this. 🦸
It's Friday.
It's hotfix time! 🔥
Nothing serious though, we didn't even break anything. Just cleaning up some minor bugs. 🧹
Fixed
AdGuard Home 0.106.0


Veröffentlicht am: 19. Mai 2021
Quite a lot of changes this time around, even if there aren't as many standouts as in some of the previous updates. We're sure that you'll be able to find a line or two in the changelog that speaks to you!
And one of the reasons for that is the constant support from the community. 👥👥 Special thanks to our open-source contributors: @jvoisin and @Paraphraser, as well as to everyone who filed issues, added translations, and helped us to test this release! 🙇
The ability to set up custom upstreams to resolve PTR queries for local addresses and to disable the automatic resolving of clients' addresses #2704
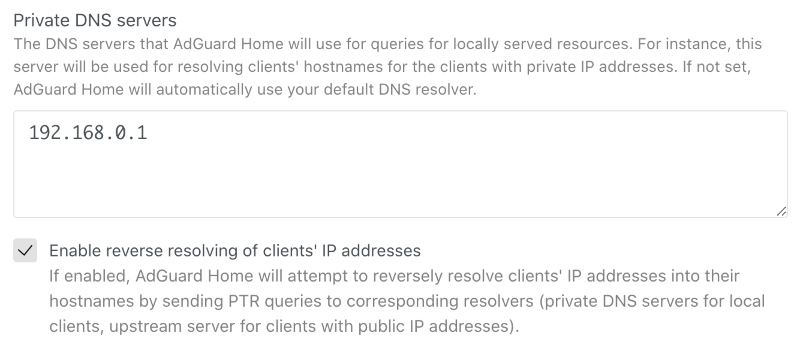
This option will improve your DNS privacy when it comes to addressing local resources. Give it a go unless you want to share your private data with googles of the world.
Search by clients' names in the query log #1273
There's not much that can be said about this feature, it's quite self-explanatory: now you can search up queries by specific clients. 🤷♀️
However, we wanted to highlight it anyway since so many of you have asked for it for quite a while. Hopefully, we delivered! 😅
Added
The ability to block user for login after configurable number of unsuccessful attempts for configurable time #2826.
$denyallow modifier for filters #2923.Hostname uniqueness validation in the DHCP server #2952.
Hostname generating for DHCP clients which don't provide their own #2723.
New flag
--no-etc-hosts to disable client domain name lookups in the operating system's /etc/hosts files #1947.Logging of the client's IP address after failed login attempts #2824.
Verbose version output with
-v --version#2416.The ability to serve DNS queries on multiple hosts and interfaces #1401.
Changed
Quality of logging #2954.
The access to the private hosts is now forbidden for users from external networks #2889.
The reverse lookup for local addresses is now performed via local resolvers #2704.
Stricter validation of the IP addresses of static leases in the DHCP server with regards to the netmask #2838.
Stricter validation of
$dnsrewrite filter modifier parameters #2498.New, more correct versioning scheme #2412.
Deprecated
Go 1.15 support. v0.107.0 will require at least Go 1.16 to build.
Fixed
Multiple answers for
$dnsrewrite rule matching requests with repeating patterns in it #2981.Root server resolving when custom upstreams for hosts are specified #2994.
Inconsistent resolving of DHCP clients when the DHCP server is disabled #2934.
Comment handling in clients' custom upstreams #2947.
Overwriting of DHCPv4 options when using the HTTP API #2927.
Assumption that MAC addresses always have the length of 6 octets #2828.
Support for more than one
/24 subnet in DHCP #2541.Invalid filenames in the
mobileconfig API responses #2835.Removed
Go 1.14 support.
AdGuard Home 0.105.2


Veröffentlicht am: 15. März 2021
There are big flashy updates, and there are seemingly unassuming ones, which constitute, however, the backbone of any successful project. This is the latter, as you may have guessed. You'll find here a heap of bugfixes and a security update for CVE-2021-27935.
Security
Session token doesn't contain user's information anymore (#2470).
Fixed
Incomplete hostnames with trailing zero-bytes handling (#2582).
Wrong DNS-over-TLS ALPN configuration (#2681).
Inconsistent responses for messages with EDNS0 and AD when DNS caching is
enabled (#2600).
Incomplete OpenWrt detection (#2757).
DHCP lease's
expired field incorrect time format (#2692).Incomplete DNS upstreams validation (#2674).
Wrong parsing of DHCP options of the
ip type (#2688).
AdGuard Home v0.105.1


Veröffentlicht am: 16. Februar 2021
Have you ever thought about why traditions are so important?🧙♂️ Traditions help us remember that we are part of a history that defines our past, shapes who we are today, and who we are likely to become. This is why we at AdGuard respect our traditions, and the most important one is pushing the inevitable hotfix right after every major update.🔥🔧
Jokes aside, here's the list of things fixed and improved in this hotfix.
Changed
"Permission denied" errors when checking if the machine has a static IP no
longer prevent the DHCP server from starting (#2667).
The server name sent by clients of TLS APIs is not only checked when
strict_sni_check is enabled (#2664).Fixed
Error when enabling the DHCP server when AdGuard Home couldn't determine if
the machine has a static IP.
Optical issue on custom rules (#2641).
Occasional crashes during startup.
The field
"range_start" in the GET /control/dhcp/status HTTP API response
is now correctly named again (#2678).DHCPv6 server's
ra_slaac_only and ra_allow_slaac settings aren't reset to
false on update any more (#2653).The
Vary header is now added along with Access-Control-Allow-Origin to
prevent cache-related and other issues in browsers (#2658).The request body size limit is now set for HTTPS requests as well.
Incorrect version tag in the Docker release (#2663).
DNSCrypt queries weren't marked as such in logs (#2662).
AdGuard Home 0.105.0


Veröffentlicht am: 12. Februar 2021
We took our sweet time with this update, but you'll most certainly find it to be worth the wait. The changelog contains three absolute 💥bangers and a laundry list of lesser changes.
🕵️♂️ Client ID support for DNS-over-HTTPS, DNS-over-QUIC, and DNS-over-TLS #1387
This feature would be really useful to those of you who run an encrypted DNS resolver on a public server. In short, you can now identify your devices not just by their IP address (which is, frankly, not too useful in a public server scenario 🤷♀️), but by using a special "Client ID".

Here's how it works:
First, you add a client and specify an arbitrary string as its "Identifier", for instance,
my-iphone.On the client device you can now configure:
DNS-over-HTTPS: https://example.org/dns-query/my-iphoneQueries and stats are now properly attributed to your device.

🔐 AdGuard as a DNSCrypt-resolver #1361
DNSCrypt was the very first DNS encryption protocol that got some traction. It may not be as popular as DoH/DoT/DoQ now, but it is still viable. Moreover, performance-wise DNSCrypt is better than any of them. And now that v0.105.0 is out, AdGuard Home can be configured to work as a DNSCrypt resolver!
However, here goes the tricky part. We haven't yet exposed these settings to the Web admin panel so if you want to have DNSCrypt, you'll need to follow this instruction and do it via editing the configuration file (
AdGuardHome.yaml). Not that it would scare you off, would it? 🤓
Regarding DNSCrypt clients - AdGuard for Android, Windows and iOS support it, Mac will get its support pretty soon. Besides that, here is a long list of client software that supports it as well.
🆎 $dnsrewrite and $dnstype modifiers #2102#2337
AdGuard Home now supports two more powerful rule modifiers that will help blocklists' maintainers.
$dnstype lets you narrow down the rule scope and apply it only to queries of a specific type(s). For instance, Apple devices now support HTTPS DNS query type. While being generally a good thing, this new type may sometimes be harmful😲. By using $dnstype you can block it completely using a simple rule like this: $dnstype=HTTPS$dnsrewrite is another powerful modifier that allows you to modify DNS responses. Note that this modifier is much more powerful compared to something like a hosts file.Here are some examples:
||example.org^$dnsrewrite=SERVFAIL;; - return SERVFAIL for example.org and all it's subdomains|test.example.org^$dnsrewrite=NOERROR;TXT;hello_world - add a TXT record for test.example.org|example.org^$dnsrewrite=example.com - redirect example.org to example.com|example.org^$dnsrewrite=1.1.1.1 - redirect example.org to example.comYou can find more examples in the documentation.
Added
The host checking API and the query logs API can now return multiple matched rules #2102
Detecting of network interface configured to have static IP address via
/etc/network/interfaces#2302A 5 second wait period until a DHCP server's network interface gets an IP address #2304
HTTP API request body size limit #2305
Changed
Access-Control-Allow-Origin is now only set to the same origin as the domain, but with an HTTP scheme as opposed to *#2484workDir now supports symlinks.Stopped mounting together the directories
/opt/adguardhome/conf and /opt/adguardhome/work in our Docker images #2589When
dns.bogus_nxdomain option is used, the server will now transform responses if there is at least one bogus address instead of all of them #2394. The new behavior is the same as in dnsmasq.Made the mobileconfig HTTP API more robust and predictable, add parameters and improve error response #2358
Improved HTTP requests handling and timeouts #2343
Our snap package now uses the
core20 image as its base #2306Deprecated
Go 1.14 support. v0.106.0 will require at least Go 1.15 to build.
The
darwin/386 port. It will be removed in v0.106.0.The
"rule" and "filter_id" fields in GET /filtering/check_host and
GET /querylog responses. They will be removed in v0.106.0 #2102Fixed
Autoupdate bug in the Darwin (macOS) version #2630
Inability to set DNS cache TTL limits #2459
Possible freezes on slower machines #2225
A mitigation against records being shown in the wrong order on the query log page #2293
A JSON parsing error in query log #2345
Incorrect detection of the IPv6 address of an interface as well as another infinite loop in the
/dhcp/find_active_dhcp HTTP API #2355Removed
The undocumented ability to use hostnames as any of
bind_host values in the configuration. Documentation requires them to be valid IP addresses, and now the implementation makes sure that that is the case #2508Dockerfile#2276. Replaced with the script scripts/make/build-docker.sh which uses scripts/make/Dockerfile.Support for pre-v0.99.3 format of query logs #2102
AdGuard Home 0.104.3


Veröffentlicht am: 12. Februar 2021
Bugfixes... 😌 There's something about them that we just can't resist. We always want more! 🧟
When there's nothing more to fix, we just roll out a new major update, introduce some fresh bugs and start all over. It's a circle of life ☯️
Luckily, there are still some to prey upon in v0.104. Have a look at what we've fixed this time:
Fixed
Don't expose the profiler HTTP API #2336
Load query logs from files after loading the ones buffered in memory #2325
Don't show Unnecessary errors in logs when switching between query log files #2324
Don't show
404 Not Found errors on the DHCP settings page on Windows. Show that DHCP is not currently available on that OS instead #2295Fix an infinite loop in the
/dhcp/find_active_dhcp HTTP API method #2301Various internal improvements
AdGuard Home 0.104.1


Veröffentlicht am: 12. Februar 2021
Those who pay close attention to AdGuard Home releases know that we keep hotfixes close to our hearts 🔥♥️ This time we held for as long as we could, but ultimately gave in to the urge 😔
Here's a patch to v0.104 with some fixes and minor improvements.
Fixed
Solve the
permission denied error when launching a DHCP server on Linux using Snap#2228. Users experiencing this issue should refresh their snap and call:
snap connect adguard-home:network-controlThis won't be required in the future versions.
Use matching fonts in the Custom Filters textarea #2254
Show the correct query type for DNS-over-QUIC queries in query log #2241
Increase the default number of simultaneous requests to improve performance #2257
Always set a secondary DNS in DHCP #1708
Improve stability on DNS proxy restart #2242
Improve logging on DNS proxy restart #2252
Don't show a “Loading” message and don't rerequest logs once we've reached the end of logs on the query log page #2229
Various internal improvements.
AdGuard Home 0.104.0


Veröffentlicht am: 12. Februar 2021
We have something special for y'all today. Not just an implementation of a new feature but the first ever implementation of a new feature! 😮 This is about DNS-over-QUIC, a new DNS encryption protocol — read on to learn more.
Ah, yes, there's also a bunch of other good stuff, too: DHCP-related changes, a .mobileconfig generator for iOS and macOS, and a handful of other enhancements and bugfixes.
DNS-over-QUIC support #2049
AdGuard Home now natively supports a new DNS encryption protocol called DNS-over-QUIC. DoQ standard is currently in the draft state, and AdGuard Home (and dnsproxy) is it's first open-source implementation.🥇

So what's good about it? 🤔 Unlike DoH and DoT, it uses QUIC as a transport protocol and finally brings DNS back to its roots — working over UDP. It brings all the good things that QUIC has to offer — out-of-the-box encryption, reduced connection times, better performance when data packets are lost. Also, QUIC is supposed to be a transport-level protocol and there are no risks of metadata leaks that could happen with DoH. 🔒
At this moment, the only major public DNS resolver that provides DNS-over-QUIC is AdGuard DNS. 😎 Use
quic://dns-unfiltered.adguard.com in the upstreams settings to start using AdGuard DNS "Non-Filtering".DHCP rework: DHCP6 support, custom DHCP options
We did a huge rework of our DHCP server implementation. Thanks to it, AdGuard Home now supports DHCP6 and allows setting custom DHCP options.
Please note that in order to set DHCP options, you'll need to edit the configuration file.
Add support for DHCPv6: #779
DHCPv6 RA+SLAAC: #2076
DHCP: automatic hostnames: #1956
Add DHCP Options: #1585
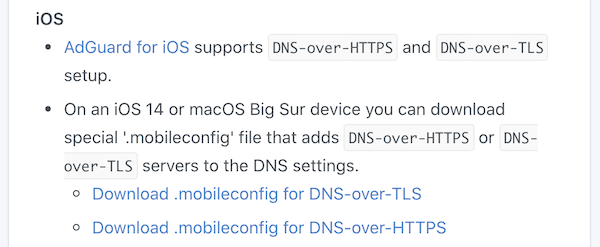
iOS and MacOS .mobileconfig generator: #2110
iOS 14 and macOS Big Sur natively support DNS-over-HTTPS and DNS-over-TLS. However, it's not that simple to configure them — you need to install a special "configuration profile" for that. 🤯 In order to make things easier, AdGuard Home can generate these configuration profiles for you. Just head to "Setup Guide" -> "DNS Privacy" and scroll to iOS.
Binary transparency
AdGuard Home binaries are now signed with our GPG key and you can now easily verify that they really come from us: https://github.com/AdguardTeam/AdGuardHome/wiki/Verify-Releases
Other improvements
Allow entering comments to the Upstreams box: #2083
Load upstreams list from a file: #1680
Add ARMv8 to future releases, potentially append a v8 binary to the most recent non-beta release: #2125
Redesign query logs block/unblock buttons: #2050
Treat entries starting with "/" as "://" under specific circumstances: #1950
Use "Null IP" instead of NXDOMAIN by default: #1914
Bootstrap with TCP upstreams: #1843
Add block and unblock buttons to 'check the filtering' result: #1734
ipset feature support: #1191
Add Belarusian and Chinese Traditional HK languages: #2106
Add new language: en-silk: #1796
Use DOH or DOT as bootstrap: #960
Fixed
Reverse lookups return empty answers for hosts from /etc/hosts: #2085
Static lease hostnames are overridden by client-identifier: #2040
Query log doesn't display name for blocked services: #2038
Custom filter editor works with delay: #1657
Incorrect link address: #2209
Smartphone compatible design for user interface: #2152
Misleading information during service installation: #2128
Remove the limit on cache-min-ttl, 3600: #2094
Cannot change minimum TTL override in UI: #2091
Optical Issue on mobile phone: #2090
Setting a large DNS Cache Size in the Web GUI will exceed the unit32 range.: #2056
Clients requests aren't counted properly: #2037
Publish privacy policy on front page (README.md): #1960
Sorting various IP Address Columns in the UI (eg in dhcp static leases) does not sort correctly. They are treated as strings instead of numeric.: #1877
Requests count for clients with CIDR IP addresses: #1824



