AdGuard Home 0.107.76


公開日: 2026年5月21日
「壊れていないなら直すな」(“if it ain't broke don't fix it”)という英語のことわざがありますが、もし実際に壊れていたらどうでしょう?例えば、前回のアップデートでうっかりキャッシュ関連が壊れてしまったような場合です。そんな時には、ホットフィックス!AdGuard Homeのキャッシュを修復するには、ぜひ今回のアップデートをインストールしてください。
AdGuard Home 0.107.75


公開日: 2026年5月19日
今回のアップデートでは、AdGuard Homeのセキュリティが大幅に強化されました。イメージとしては、全てのドアの鍵をしっかりとかけ直し、鍵がかかっていることを徹底的に再確認した、という風にお考えください。
DNS-over-QUICおよびDNS-over-HTTPSに影響を及ぼし、DNSのプライバシーを脅かすリスクがあった重大な脆弱性を修正しました。これで、暗号化された通信は再び、しっかりと保護されたトンネルを通って送信されるようになっています。
また、Goを最新バージョンに更新することで、既知のGoライブラリ内脆弱性を一掃しました。
AdGuard Home 0.107.74


公開日: 2026年4月16日
人生のあらゆることに対して言えることですが、最高のものが最高であるのは、平凡なものが存在するおかげでもあるのです。平凡なものがなければ、非凡なものも存在し得ないでしょう。
何を申し上げたいかと言いますと、今回のAdGuard Homeのアップデートは、主にバグ修正やセキュリティ系更新を中心とした「地味な」ものだというわけです。このようなアップデートがあるからこそ、新機能などが追加された時は新鮮でワクワクするような感情をお届けできるのではないかと考えております!
AdGuard Home 0.107.73


公開日: 2026年3月10日
本ホットフィックスは、最近発見された重大な脆弱性を修正するものです。この脆弱性により、ユーザーが認証をバイパスし、有効な認証情報なしでAdGuard Homeへのフルアクセスを取得することが可能になっていた可能性があります。お使いのAdGuard Homeクライアントを直ちにアップデートされるよう強く推奨いたします。
AdGuard Home 0.107.72


公開日: 2026年2月25日
今年初のAdGuard Homeアップデートです。
2026年の幕開けは派手ではないですが、しっかりした変更内容でございます。本アプデには、TLS証明書更新の新たな処理方法、その他いくつかのマイナーな新機能、設定変更、重要な修正数点、そして恒例のセキュリティ系更新が含まれています。
今後はさらなる機能を準備しておりますのでご期待ください!
AdGuard Home 0.107.69


公開日: 2025年10月30日
AdGuard Home v0.107.69 の登場です。今回は、こっそり潜り込もうとしていた厄介なバグ2件を修正するための小休止アップデートです。新機能はありませんが、動作がよりスムーズになっているはずです。
AdGuard Home 0.107.68


公開日: 2025年10月23日
まずは「いつもの」お知らせです:セキュリティ更新を恒例通り実施しました。今回は、意外なことにバグ修正なしで乗り越えることもできました。
では、本題に入りたいと思います。DNS rewrite (DNS書き換え)ルールの有効化/無効化を可能にする新機能を導入しました。
これは初期の機能リクエストの一つであり、ようやく皆様に提供できることを嬉しく思います。DNS書き換えルールは一括で有効化/無効化できるほか、個々のルール単位での操作も可能です。いずれの場合も、UI経由でもYAMLファイルの編集でも有効化/無効化を行うことができます。
AdGuard Home 0.107.66


公開日: 2025年9月15日
世界最高のソフトウェアを持っていても、ユーザーがアクセスできなければ意味ないですよね。今回のアップデートでは、認証エラーを最優先課題とし修正いたしました。これにより、問題なくログインしてAdGuard Homeを最大限に活用できるようになっています。また、いつも通りのセキュリティ系更新とその他の変更を追加したところで、今回のバージョン0.107.66が完成となりました。
AdGuard Home 0.107.64


公開日: 2025年7月29日
あらゆるニーズに対応したバグ修正を行いました。セキュリティバグ修正、キャッシュ応答TTLバグ修正、DNSCrypt証明書バグ修正など、すべてが今回のAdGuard Homeの新バージョンに入っております。
AdGuard Home 0.107.63


公開日: 2025年6月30日
アップデートは大きな問題修正ばかりではありません。時には、全体的な安定性を向上させるためのちょっとした修正や調整が必要になることもあります。
AdGuard Home 0.107.62


公開日: 2025年5月29日
多くの企業が「client-oriented」(顧客中心)を謳っていますが、AdGuard Home は「
$client-oriented」でもあることを誇りに思っています。今回のアップデートでは、client修飾子を含むルールが機能しなかったバグを修正しました。また、Goのバージョンを更新し、既知の脆弱性をなくすことで、AdGuard Home のセキュリティをさらに向上させました。
AdGuard Home 0.107.60


公開日: 2025年4月17日
このアップデート内容に関する通知をお読みになっている方は、AdGuard Homeの真パワーユーザーであるに違いありません。今回のアップデートは、特に目立つ新機能はありませんが、Goの脆弱性に対するパッチ、UIとDockerの更新、およびいくつかのバグ修正が含まれています。
AdGuard Home 0.107.59


公開日: 2025年3月21日
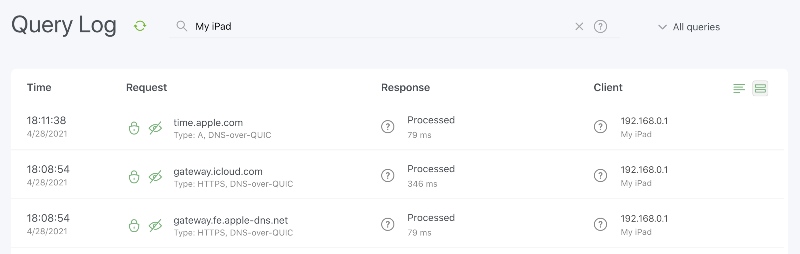
このhotfixは、前回のアップデートで出たバグ(クエリログの検索ボックスにユーザーが何も入力できないというバグ)に対処するものです。また、この機会を使って、クライアント修飾子の誤動作も修正しました。
謝辞
コミュニティモデレーターチーム@AdguardTeam/community-moderatorsの皆様、および問題を報告・調査したり、翻訳を追加したり、このリリースのテストを手伝ってくださったすべての方々に感謝いたします。
AdGuard Home 0.107.58


公開日: 2025年3月20日
哲学的な質問をさせてください。とあるアップデートに通常よりも多くのバグ修正が含まれている場合、それは良いことでしょうか、それとも悪いことでしょうか?🤔
幸いにも、私たちは開発者であって哲学者ではありません。ですから、いくつかの事実だけを述べて、思考実験は私たちよりも賢明な方々にお任せします。そして、その事実とは、今回のアップデートで多くのバグを修正しただけでなく、新機能も追加したということです。
DNS クエリを確認するためのツールを改善
プライバシーの保護と広告の対処に真剣に取り組んでいる場合、フィルタリングリストやカスタムルールセットの形で、大量のルールをお持ちのことでしょう。 今回で、フィルタリングを調整する際に、特定のDNSクエリがブロックされるかどうかを簡単に確認できるようになりました。 既存のツールを改良し、DNSレコードタイプと特定のクライアント(IPアドレスまたはClientID)を示すオプションを追加しました。 情報を入力すると、リクエストに一致するすべてのルールが表示されます。 ボーナス機能:その場で任意のドメインのブロックを解除もできます。
AdGuard Home 0.107.57


公開日: 2025年2月21日
本アップデートでは、Web UIでアップストリームタイムアウトの指定が可能になりました。また、バグ修正とセキュリティ系改善もいくつか行いました。
AdGuard Home 0.107.56


公開日: 2025年1月24日
今年初のアップデートです。バグ修正、新API、Goバージョンの更新が含まれています。後者は脆弱性対策に役立ちます。
AdGuard Home 0.107.55


公開日: 2024年12月12日
このアップデートで、Windowsユーザーの皆様にとっては、一部のWindowsインストールに影響を及ぼしているバグに対処しました。全てのAdGuard Home愛好家の皆様にとっては、Goのバージョンを更新することで、複数の脆弱性を補強していくつかのリークを修正しました。
AdGuard Home 0.107.54


公開日: 2024年11月6日
今回の AdGuard Home アップデートは、特に Windows ユーザーの皆様にとって興味深いものです。前バージョンでは実装する時間がなかった、Windows 用に必要なセキュリティ改善を行いました。しかし、今回の AdGuard Home アップデートには、Windows ユーザーのためだけでなく、全ユーザーのための改善ももちろん含まれています。
AdGuard Home 0.107.53


公開日: 2024年10月3日
AdGuard Home のアップデートを数ヶ月延期するのは久しぶりです。それにはもちろん、正当な理由がありました。コミュニティメンバーのご協力(いつも皆様に本当に感謝しております)により、2つの脆弱性を発見し、そのパッチ作成に取り組んでおりました。解決策のテストには予想より少し時間がかかりましたが、スピードよりも品質を重視しているため、時間を必要なだけかけました。
脆弱性のパッチやバグの修正以外に、いくつかの改善も行いました。例えば、64ビットのRISC-VアーキテクチャとEcosiaの検索エンジンをセーフサーチに追加しました。フル変更履歴は下記をご覧ください。
AdGuard Home 0.107.52


公開日: 2024年7月4日
このバージョンでは、多くのバグを修正し、フロントエンドをTypeScriptに移行し、フロントエンドのライブラリを更新したことで、開発の効率とユーザーインターフェースの質を向上させました。
AdGuard Home 0.107.51


公開日: 2024年6月6日
小さなバグフィックスとセキュリティ関連のアップデートです。今後のバージョンでの新機能実装の開発に取り組んでおります。
AdGuard Home 0.107.50


公開日: 2024年5月24日
前回の AdGuard Home のアップデートでごく一部のユーザが AdGuard Home を起動できなかった問題を、このホットフィックスで修正いたしました。
AdGuard Home 0.107.49


公開日: 2024年5月21日
Fast approaching summer promises everyone its warmth, and all kinds of bugs are crawling from under the rocks and twigs to enjoy the sun 🌞. Here's a patch to make sure that they stay in the grass and nowhere near AdGuard Home.
AdGuard Home 0.107.48


公開日: 2024年4月5日
前回のアップデート後、バンされているユーザーが暗号化されたプロトコルでDNSクエリを実行できるようになってしまいました。この動作はまったく意図したものではなく、今回のHotfixにより臨時修正いたしました。
このような見落としがあったことを深くお詫びいたします。今後このようなミスが発生しないよう、最善を尽くします。
AdGuard Home 0.107.47


公開日: 2024年4月4日
今回もセキュリティ関連とバグ修正のアップデートで、タイムゾーン選択の際の問題やその他のいくつかの厄介なバグを修正しました。
AdGuard Home 0.107.46


公開日: 2024年3月20日
前回のリリースノートで約束した通り、今回のアップデートには、いくつかのバグ修正と改善が含まれています。
AdGuard Home 0.107.45


公開日: 2024年3月7日
これはセキュリティのための更新といくつかの修正、そして小さな機能を含む小さなアップデートです。さらなるのものを準備中ですので楽しみにしてください。
AdGuard Home 0.107.44


公開日: 2024年2月6日
本日のアップデートは、新機能やその類で皆さんの度肝を抜くようなことはないですが、ちょっとした変更と様々なバグフィックスでメンテナンスを行いました
AdGuard Home 0.107.43


公開日: 2023年12月11日
Everybody needs something to keep themselves warm during the cold winter days ❄️. Many people opt for hot coffee ☕ or hot chocolate, but we at AdGuard prefer hotfixes 🔥.
AdGuard Home 0.107.42


公開日: 2023年12月7日
As the winter holidays approach, many of us begin to think about what gifts we will give and receive 🎁. With AdGuard, the holidays come early: we decided not to wait too long and present you with this new version of AdGuard Home today!
Among the long-awaited features in this release are the option to enable caching for persistent clients with custom DNS upstream configuration and the option to disable plain DNS for better security.
AdGuard Home 0.107.41


公開日: 2023年11月13日
季節が変わっても、バグが出てしまうことがあることには変わりありません。今回の新バージョンでは、かなり多くのバグを修正しただけでなく、AdGuard Home の設定をより簡単にし、DDoS攻撃から保護する機能も追加しました。
AdGuard Home 0.107.40


公開日: 2023年10月18日
インターネット利用を妨げるバグほど不気味なものがあるだろうか?このホットフィックスでこのようなバグを解消いたします!
AdGuard Home 0.107.39


公開日: 2023年10月11日
ハロウィンの季節がもうすぐやってきますが、私たちに全然怖くないのは、いくつかの新機能とバグフィックスを含む新バージョンをリリースすることです!
AdGuard Home 0.107.38


公開日: 2023年9月11日
新バージョンは果物のようなもので、おいしくてナチュラルなリンゴであればあるほど、どこかにバグ(虫)がある可能性が高い。そういう意味では、前バージョンはとても美味しかったみたいで、このHotfixでは、残っていたバグを修正いたしました。
AdGuard Home 0.107.37


公開日: 2023年9月9日
夏が過ぎ去りましたが、たまっていた待望の機能、改良、バグフィックスを含む新バージョンの時が来ました!
サービスブロックの一時停止スケジュール
サービスブロックフィルターの一時停止を簡単に設定できるようになりました。例えば、1日中SNSをブロックし、仕事終了後に30分間だけ許可する、という風に設定できます。
この機能は数ヶ月前から社内で開発中でしたが、今回のバージョンリリースでついにウェブUIで利用できるようになりました。
フォールバックサーバー
もう1つの待望の機能はフォールバックサーバーで、このサーバーはメインのアップストリームDNSサーバーに到達できない場合に使用されます。
構文はメインのアップストリーム入力と同じなので、ドメインごとに異なるフォールバックサーバーを設定することができます。
アップストリーム統計
DNSアップストリームに関連するもう1つの新機能は、ダッシュボードに表示される新しい「アップストリーム統計」です。
これにより、ユーザーはどのアップストリームが他よりも速いか、どのアップストリームが最も使用されているかを確認することができます。
謝辞
オープンソースのコントリビューターである @ssrahul96 さんをはじめ、問題の報告や検証、翻訳、本バージョンのテストにご協力いただいたすべての方々に感謝申し上げます!
AdGuard Home 0.107.36


公開日: 2023年8月2日
小さなバグフィックスとセキュリティ関連のアップデートです。今後のバージョンでの新機能実装の開発に取り組んでおります。
AdGuard Home 0.107.35


公開日: 2023年7月26日
前回のアップデートで、フィルタリングルールリストの更新を最適化し、場合によっては最大3倍のスピードアップを達成できました。しかし、新しいアルゴリズムは厳しすぎることが判明したので、今回のアップデートでは、より典型的なフィルタリングルールリストに対する最適化を維持しつつ、アルゴリズムによる検証を緩和しました。
いつも通り、この新バージョンには細かなバグ修正なども含まれています。
AdGuard Home 0.107.34


公開日: 2023年7月12日
このアップデートでは、AdGuard Home のセキュリティが改善され、いくつかの大きな問題が修正されました。
セーフブラウジングとCPUスパイク
6月に AdGuard Home のセキュリティアップデートをリリースし、いくつかのバグを修正しました。皮肉なことに、このアップデートは別のバグをもたらしました。それ以来、セーフブラウジングとペアレンタルコントロールが正しく動作せず、パフォーマンスの低下、不規則なクラッシュ、CPUのスパイクにつながるケースがありました。
真相究明には丸1ヶ月を要しましたが、素晴らしいコミュニティ・メンバーがいなければ、さらに時間がかかっていたに違いません。@bigwookieさん、@TheCableGuy99さん、そしてその他の方々のおかげでより早く解決を見つけることができました。"超大型バグ"の正体は大きく見える小さなバグであることが判明した。それらは今回のアップデートで容赦なく対処されました。
Docker の HEALTHCHECK
【Dockerユーザー向けお知らせ】Dockerの
HEALTHCHECK メカニズムが、特にPodmanや他の一般的なDockerツールと共に使用された場合に多くの問題を引き起こしていたため、削除いたしました。謝辞
オープンソースのコントリビューターである@Jiraiya8さんと、問題を提出し、検査し、翻訳を追加し、このバージョンのテストを手伝ってくれたすべての方々に感謝いたします!
AdGuard Home 0.107.33


公開日: 2023年7月3日
定期的なバグ修正🔧アップデートです。加えて、今後のバージョンで新機能を追加しやすくするための内部的な改善にも取り組んでいます。
AdGuard Home 0.107.32


公開日: 2023年6月13日
A hotfix release to fix a major issue in the previous release.
AdGuard Home 0.107.31


公開日: 2023年6月8日
A hotfix release to fix two major issues in the previous release.
AdGuard Home 0.107.30


公開日: 2023年6月7日
A small bugfix and security release. We are working on new features in future releases.
AdGuard Home 0.107.29


公開日: 2023年4月18日
前回のアップデートは国際有人宇宙飛行の日(英:International Day of Human Space Flight)に行われましたが、AdGuard Homeという私たちの宇宙船の打ち上げには少しうまくいかなかったところがあったようです。今回のバージョンでは、いくつかの厄介なバグを修正し、クライアント無視機能にも磨きをかけました。
AdGuard Home 0.107.28


公開日: 2023年4月12日
ついに、たくさんの新機能を備えたビッグアップデートの登場です 。その中でも、長い間要望の多かったいくつかのQOL(クオリティ・オブ・ライフ)変更に注目したいと思います。
グローバル保護の一時停止
30秒から丸1日まで、設定した期間の間保護を一時停止する方法が追加されました。これは、誤ってブロックされたサイトにアクセスする必要があるときや、AdGuard Homeを完全にオフにせずに一時的に無効にしたいときに便利です。
 一時停止時間が終了すると、AdGuard Homeは保護機能を自動的に再びオンにします。
一時停止時間が終了すると、AdGuard Homeは保護機能を自動的に再びオンにします。
 一時停止時間が終了すると、AdGuard Homeは保護機能を自動的に再びオンにします。
一時停止時間が終了すると、AdGuard Homeは保護機能を自動的に再びオンにします。セーフサーチのコントロールを改善
Google、Bing、YouTubeなど特定のサービスに対してセーフサーチの設定を有効・無効にすることで、セーフサーチの設定を細かく調整できるようになりました。
 同じことを、各クライアントレベルでも行うことができます。セーフサーチのもう一つの小さな改良点は、IPv6アドレスのサポートを改善したことです。
同じことを、各クライアントレベルでも行うことができます。セーフサーチのもう一つの小さな改良点は、IPv6アドレスのサポートを改善したことです。
 同じことを、各クライアントレベルでも行うことができます。セーフサーチのもう一つの小さな改良点は、IPv6アドレスのサポートを改善したことです。
同じことを、各クライアントレベルでも行うことができます。セーフサーチのもう一つの小さな改良点は、IPv6アドレスのサポートを改善したことです。
AdGuard Home 0.107.27


公開日: 2023年4月5日
このアップデートは、セキュリティとバグ修正のアップデートであり、Goプログラミング言語バージョンの更新といくつかの不具合の修正以外には、変更はありません。
より実質的な変更は、今後のアップデートに含まれる予定です。
AdGuard Home 0.107.26


公開日: 2023年3月9日
このアップデートでは、送信クエリのさらなるカスタマイズオプション、タイプに基づいてリクエストを拒否する新オプション、およびさまざまなバグフィックスを追加いたしました。
AdGuard Home 0.107.25


公開日: 2023年2月21日
このアップデートは、暗号化されていないDNS-over-HTTPを使用した場合の致命的エラーを防止するためのHotfixです。HTTPリバースプロキシの後ろでAdGuard Homeを実行している人がこの問題に直面していました。
AdGuard Home 0.107.24


公開日: 2023年2月16日
AdGuard Homeのこの新バージョンでは、クエリログや統計画面で特定のホスト名を除外する方法を追加しましたので、ブロックしたくないホスト名の指定がより便利になりました。
AdGuard Home 0.107.23


公開日: 2023年2月1日
バグフィックスや新機能をユーザーに届けるのが大好きです。
このアップデートには、ダークテーマの調整に加えて、 DNS64規格 のサポート、いくつかの新しいブロック可能なサービス、いくつかのバグ修正と内部改善が含まれています。
AdGuard Home 0.107.22


公開日: 2023年1月19日
夜に明るすぎるユーザーインターフェイスはみづらいですよね。今回のアップデートでは、最も一般的に要求された機能の 1 つであるダークテーマをAdGuard Homeに追加しました。
新しいダークテーマは現在まだ実験的で、粗削りな部分があったりします。それらを報告したい場合は、こちらのissueに書いてある手順をご利用ください。→ #5375
AdGuard Home 0.107.21


公開日: 2022年12月24日
冬を暖かくするホットフィックスです。
AdGuard Home 0.107.20


公開日: 2022年12月7日
W杯でゴールキーパーがゴールを守るように、私たちはユーザーの安全を守るために最善を尽くし、最新のセキュリティアップデーをできるだけ頻繁に受け取っていただけるよう努力しております。また、DNSキャッシュを簡単にクリアできる便利なボタンも追加しました。
AdGuard Home 0.107.19


公開日: 2022年11月23日
@sandervankasteelさんの貢献のおかげで、AdGuard Home は、いくつかの最も人気のあるMastodonインスタンスをブロックできるようになりました。
また、
--update コマンドラインオプションを追加しましたので、UIを操作することなく AdGuard Home を更新することも可能になりました。
AdGuard Home 0.107.17


公開日: 2022年11月2日
Despite this release appearing around Halloween, it shouldn't be spooky at all. The main novelty is that the list of services blockable with a single click is now synchronized with AdGuard DNS to make the user experience more unified across AdGuard services. We've also improved support for HTTP/3 as well as fixed a few annoying bugs.
AdGuard Home 0.107.16


公開日: 2022年10月7日
This is a security release. There are no new changes besides the update of the Go programming language version. More substantial changes are to come in the subsequent updates.
Full Changelog
Security
Go version has been updated to prevent the possibility of exploiting the CVE-2022-2879, CVE-2022-2880, and CVE-2022-41715 Go vulnerabilities fixed in Go 1.18.7.
AdGuard Home 0.107.15


公開日: 2022年10月3日
Sometimes, even a hotfix needs a hotfix. In the previous release, our mitigations turned out to be too restrictive, preventing some AdGuard Home features from working properly. In this release, we fix this along with a few other bugs.
We have also added experimental support for the HTTP/3 standard in the UI, DNS upstreams, and DNS clients!
Full Changelog
Security
As an additional CSRF protection measure, AdGuard Home now ensures that requests that change its state but have no body (such as POST /control/stats_reset requests) do not have a Content-Type header set on them #4970.
Added
Experimental HTTP/3 Support
See #3955 and the related issues for more details. These features are still experimental and may break or change in the future.
DNS-over-HTTP/3 DNS and web UI client request support. This feature must be explicitly enabled by setting the new property
dns.serve_http3 in the configuration file to true.DNS-over-HTTP upstreams can now upgrade to HTTP/3 if the new configuration file property
dns.use_http3_upstreams is set to true.Upstreams with forced DNS-over-HTTP/3 and no fallback to prior HTTP versions using the h3:// scheme.
Fixed
only application/json is allowed errors in various APIs #4970.
AdGuard Home 0.107.14


公開日: 2022年9月29日
This is a security release. Users are encouraged to update AdGuard Home as soon as possible.
Full Changelog
Security
A Cross-Site Request Forgery (CSRF) vulnerability has been discovered. The CVE number is to be assigned. We thank Daniel Elkabes from Mend for reporting this vulnerability to us.
SameSite PolicyThe
SameSite policy on the AdGuard Home session cookies has been upgraded to Lax. Which means that the only cross-site HTTP request for which the browser is allowed to send the session cookie is navigating to the AdGuard Home domain.Users are strongly advised to log out, clear browser cache, and log in again after updating.
Removal Of Plain-Text APIs (BREAKING API CHANGE)
We have implemented several measures to prevent such vulnerabilities in the future, but some of these measures break backwards compatibility for the sake of better protection.
The following APIs, which previously accepted or returned
text/plain data, now accept or return data as JSON. All new formats for the request and response bodies are documented in openapi/openapi.yaml and openapi/CHANGELOG.md.GET /control/i18n/current_language;POST /control/dhcp/find_active_dhcp;POST /control/filtering/set_rules;POST /control/i18n/change_language.Stricter
Content-Type Checks (BREAKING API CHANGE)All JSON APIs now check if the request actually has
Content-Type set to application/json.Other Security Changes
AdGuard Home 0.107.13


公開日: 2022年9月14日
In this hotfix release with the “lucky” patch number we have fixed a couple of issues that prevented some DHCP clients from receiving their assigned IP addresses. We've also added the new
dns.ipset_file setting, which should help users who maintain large ipsets, for example to use in firewall or VPN settings.Full Changelog
Added
The new optional
dns.ipset_file property, which can be set in the configuration file. It allows loading the ipset list from a file, just like dns.upstream_dns_file does for upstream servers #4686.Changed
The minimum DHCP message size is reassigned back to BOOTP's constraint of 300 bytes #4904.
Fixed
Panic when adding a static lease within the disabled DHCP server #4722.
AdGuard Home 0.107.12


公開日: 2022年9月7日
What better way is there to celebrate the coming of autumn than a patch release? In this new version, we have extended and significantly improved AdGuard Home's built-in DHCP server (fixing many bugs in the process) as well as improved our service blocking feature, thanks to many contributions from the community. As always, we have also updated our tooling to make sure that we use the latest versions without any known security issues.
Full Changelog
Security
Go version was updated to prevent the possibility of exploiting the CVE-2022-27664 and CVE-2022-32190 Go vulnerabilities fixed in Go 1.18.6.
Added
New
del DHCP option which removes the corresponding option from server's response #4337. See also a Wiki page.NOTE: This modifier affects all the parameters in the response and not only the requested ones.
A new HTTP API,
GET /control/blocked_services/services, that lists all available blocked services #4535.Changed
The DHCP options handling is now closer to the [RFC 2131][rfc-2131] (#4705).
When the DHCP server is enabled, queries for domain names under
dhcp.local_domain_name not pointing to real DHCP client hostnames are now processed by filters (#4865).The internal DNS client, used to resolve hostnames of external clients and also during automatic updates, now respects the upstream mode settings for the main DNS client #4403.
Deprecated
Ports 784 and 8853 for DNS-over-QUIC in Docker images. Users who still serve DoQ on these ports are encouraged to move to the standard port 853. These ports will be removed from the
EXPOSE section of our Dockerfile in a future release.Go 1.18 support. Future versions will require at least Go 1.19 to build.
Fixed
Dynamic leases created with empty hostnames #4745.
Unnecessary logging of non-critical statistics errors #4850.
AdGuard Home 0.107.11


公開日: 2022年8月19日
This hot summer is approaching its end, but hotfixes are still coming in! In this release, we have fixed configuration file migrations not working for people with AdGuard Home versions older than v0.107.7, as well as made a few minor improvements.
--
Full Changelog
--
Added
AdGuard Home 0.107.10


公開日: 2022年8月17日
In this new release, we add support for the new Discovery of Designated Resolvers DDR feature, which allows clients using plain DNS to automatically switch to secure protocols. As well as an Arabic localization and fixes for a couple of rather annoying bugs.
Full Changelog
Added
AdGuard Home 0.107.9


公開日: 2022年8月3日
Although not a lot of time has passed since the last release, this new one contains a security update, a new feature, a new platform, and some minor fixes :wrench:. It's always nice to have those!
Full Changelog
Security
Go version was updated to prevent the possibility of exploiting the CVE-2022-32189 Go vulnerability fixed in Go 1.18.5. Go 1.17 support has also been removed, as it has reached end of life and will not receive security updates.
Added
Domain-specific upstream servers test. If such test fails, a warning message is shown #4517.
windows/arm64 support #3057.
Changed
UI and update links have been changed to make them more resistant to DNS blocking.
Fixed
Go 1.17 support, as it has reached end of life.
AdGuard Home 0.107.8


公開日: 2022年7月19日
たまにどうしてもミスは起こるものです。今回のバグフィックスアップデートでは、ミスを修正しております。
フル変更ログ
セキュリティ
Go 1.17.12 で修正された
CVE-2022-1705, CVE-2022-32148, CVE-2022-30631 やその他のGo脆弱性を悪用される可能性を回避するために、Goバージョンを更新しました。修正
AdGuard Home 0.107.7


公開日: 2022年7月19日
AdGuard Homeの新バージョンのご紹介です。
DNS-over-QUIC: RFC 9250
待望のDNS-over-QUICプロトコルが、ついにドラフトから実際の標準規格であるRFC 9250へと卒業しました。このリリースでは、後方互換性のある方法で、最終バージョンの規格のサポートを追加しています。
アップストリームの制御を強化
ドメイン自体を除外しつつ、ドメインのすべてのサブドメインに対してアップストリームを指定できるようになりました。 例えば、
server-1.example.com に対する問い合わせは DNS サーバー 1.1.1.1 で解決させたいが、 example.com はデフォルトアップストリーム(この例では 94.140.14.14 )で解決させたい場合、以下を使用してください:94.140.14.14
[/*.example.com/]1.1.1.1また、プレーンDNSのアップストリームの正確なIPアドレスを覚えておく必要がなくなりました。ブートストラップサーバーがそれらを解決できる限り、新しい
udp:// アップストリームアドレススキームを使用して、アップストリームのアドレスを自動的に解決することができるのです:udp://one.one.one.one # Same as 1.1.1.1.その他の重要な変更点
ランタイムクライアント情報の収集方法をユーザーがよりコントロールできるようになりました(この機能を完全に無効にすることも可能に)。
クライアントのリクエストからのEDNSクライアントサブネット情報は、「クエリログ」ページに表示されるようになりました。
いつものように、ユーザーが脆弱性の餌食にならないよう、我々はツールを最新に保つよう努力しています。
さらに多くの小さな変更と修正がありますので、ぜひ以下のフル変更ログをご覧ください。
謝辞
オープンソースの貢献者である @Lanius-collaris さんと、問題を提出し、検証し、翻訳を追加し、このリリースのテストを手伝ってくれた皆さんに特別な感謝を捧げます。
フル変更ログ
セキュリティ
CVE-2022-29526, CVE-2022-30634, CVE-2022-30629, CVE-2022-30580とCVE-2022-29804の脆弱性が悪用される可能性を防止するため、Goバージョンを更新しました。.
パスワード強度ポリシーを導入 #3503.
追加済み
ドメインのサブドメイン用アップストリームのサポートを追加 #4503
clients.runtime_sources 設定オブジェクトにより、ランタイムクライアントの各ソースを個別に制御することが可能に #3020設定ファイルの新しいプロパティ
dns.private_networks を使って、プライベートとみなされるネットワークのセットをカスタマイズすることが可能に #3142クエリログレ記録のリクエスト詳細セクションにEDNS Client-Subnet情報を追加 #3978
プレーンUDPアップストリームサーバーのホスト名として
udp:// スキームが使用可能に #4166AdGuard Homeがサービスとしてインストールされている場合、デフォルトでFreeBSDおよびOpenBSDにおいてログを収集するようにしました。 #4213
変更済み
OpenBSDでは、デーモンスクリプトが
/bin/sh シェルではなく、推奨の /bin/ksh シェルを使うようになりました(#4533)。 この変更を適用するには、データをバックアップし、 AdGuardHome -s uninstall && AdGuardHome -s install を実行してください。ランタイムクライアントの情報源として、ARP近辺よりもReverse DNSの方が優先されるようになりました。
より回復力のあるARP処理によって、ランタイムクライアントの検出を改善しました。 #3597
Optimisticキャッシュから提供されるレスポンスのTTLが10秒に引き下げられました。
ドメイン固有のプライベートリバースDNSアップストリームサーバーは、 local-servedネットワークを指す
*.in-addr.arpa と *.ip6.arpa ドメインのみを許可するように検証されるようになりました(#3381)。 ※設定に無効なエントリが既にある場合、それらは基本的に何の効果もないため、手動で削除することを検討してください。応答のフィルタリングは、質問のタイプではなく、メッセージの回答セクションのレコードタイプを使用して行われるようになりました。 #4238
ビルド時刻の情報を追加する代わりに、ビルドスクリプトは標準化された環境変数 [
SOURCE_DATE_EPOCH][repr] を使って、バイナリがビルドされたコミットの日付を追加するようになりました(#4221)。これにより、パッケージメンテナやAdGuard Homeを自分でコンパイルする方々のために、再現性のあるビルドを簡素化することができます。設定ファイルの
dns.bogus_nxdomain プロパティは、IPアドレスとCIDR記法をサポートするようになりました。 #1730構成変更
本アップデートで、スキーマのバージョンが 12 から 14 に変更されました。
オブジェクト
clients は、スキーマのバージョン13以前では実際永続クライアントの配列でしたが、 persistent と runtime_sources のプロパティで構成されるようになりました:# BEFORE:
'clients':
- name: client-name
# …
# AFTER:
'clients':
'persistent':
- name: client-name
# …
'runtime_sources':
whois: true
arp: true
rdns: true
dhcp: true
hosts: trueclients.runtime_sources.rdns フィールドの値は、 dns.resolve_clients プロパティから取得されます。この変更をロールバックするには、runtime_sources プロパティを削除し、persistent の内容を clients 自体に移動し、 clients.runtime_sources.rdns の値を dns.resolve_clients に移動し、 schema_version を 13 に戻してください。プロパティ
local_domain_name は、スキーマのバージョン12以前では dns オブジェクトの一部でしたが、 dhcp オブジェクトの一部になりました:# BEFORE:
'dns':
# …
'local_domain_name': 'lan'
# AFTER:
'dhcp':
# …
'local_domain_name': 'lan'この変更をロールバックするには、本プロパティを
dns オブジェクトに戻し、schema_version を 12 に戻してください。廃止済み
no-etc-hosts
オプションを廃止しました。その機能は、clients.runtime_sources.hosts` という設定プロパティで制御されるようになりました。v0.109.0ではこのフラグは完全に削除されます。修正済み
AdGuard Home 0.107.6


公開日: 2022年4月14日
This is a small security-oriented update. This AdGuard Home version requires Go v1.17 and later to build, because older Go versions receive no further support, including security patches.
Aside from that, we've slightly updated
$dnsrewrite modifier to support the user-defined Discovery of Designated Resolvers (DDR). We are planning on continuing to make more improvements to it in the future updates, see #4463.The rest are minor changes and ever-present bugfixes.
Full Changelog
Security
User-Agent HTTP header removed from outgoing DNS-over-HTTPS requests.Go version was updated to prevent the possibility of exploiting the CVE-2022-24675, CVE-2022-27536, and CVE-2022-28327 vulnerabilities.
Added
Changed
Filtering rules with the dnsrewrite modifier that create SVCB or HTTPS responses should use ech instead of echconfig to conform with the latest drafts.
Deprecated
SVCB/HTTPS parameter name
echconfig in filtering rules with the dnsrewrite modifier. Use ech instead. v0.109.0 will remove support for the outdated name echconfig.Obsolete --no-mem-optimization option #4437. v0.109.0 will remove the flag completely.
Fixed
I/O timeout errors when checking for the presence of another DHCP server.
Network interfaces being incorrectly labeled as down during installation.
Rules for blocking the QQ service #3717.
Removed
Go 1.16 support, since that branch of the Go compiler has reached end of life and doesn't receive security updates anymore.
AdGuard Home 0.107.5


公開日: 2022年4月14日
This is a security release. There are no new changes besides the update of the Go programming language version.
More substantial changes are to come in the subsequent updates.
Full Changelog
Security
Go version was updated to prevent the possibility of exploiting the CVE-2022-24921 vulnerability. As the CVE page is still showing “reserved” at the time of publishing, see also golang/go#51112.
AdGuard Home 0.107.4


公開日: 2022年4月14日
A small update to fix a couple bugs and shore up some Go vulnerabilities.
More substantial changes are to come in the subsequent updates.
Full Changelog
Security
Go version was updated to prevent the possibility of exploiting the CVE-2022-23806, CVE-2022-23772, and CVE-2022-23773 vulnerabilities.
Changed
Minor UI improvements.
Fixed
AdGuard Home 0.107.3


公開日: 2022年2月3日
This version contains bug fixes and cleanups 🧹. Also, there is a new minor feature: now you can rewrite responses for domains using the response code
NOERROR. Similar rules will allow to get a successful response without records, e.g.:|example.com^$dnsrewrite=NOERRORFull Changelog
Added
AdGuard Home 0.107.2


公開日: 2022年1月12日
You know, it is very hard to break your bad habits. We're still struggling with one, the overwhelming need to roll out hotfixes to AdGuard Home releases 😢
Now this one is a hotfix release for a really critical CPU overconsumption bug in v0.107.1.
Please update asap and with this, we wish you happy holidays!🎄
Full Changelog
Fixed
Infinite loops when TCP connections time out (#4042).
AdGuard Home 0.107.1


公開日: 2022年1月12日
In a not-futile-at-all-we-swear 😅 attempt to fix all bugs before the New Year we're rolling out a hotfix to the recent v0.107.0. Hopefully, this time we got it all right. And if not, there are still a couple of sheets left on the calendar 📆 and the mug is still half-full with lukewarm coffee ☕
Acknowledgements
A special thanks to our open-source contributors: @Aikatsui and @mdawsonuk, as well as to everyone who filed and inspected issues, added translations, and helped us test this release!
Full Changelog
Changed
The validation error message for duplicated allow- and blocklists in DNS settings now shows the duplicated elements (#3975).
Fixed
ipset initialization bugs (#4027).Legacy DNS rewrites from a wildcard pattern to a subdomain (#4016).
Service not being stopped before running the
uninstall service action (#3868).Broken
reload service action on FreeBSD.Legacy DNS rewrites responding from upstream when a request other than
A or AAAA is received (#4008).Panic on port availability check during installation (#3987).
Incorrect application of rules from the OS's hosts files (#3998).
AdGuard Home 0.107.0


公開日: 2022年1月12日
We've had some big AdGuard Home updates in the past, but this one is to top them all. It's been brewing for almost eight months! 🙀 So no wonder there's heaps upon heaps of new features, improvements, bugfixes, and other changes. We'd better start listing them ASAP, or else we'll be risking missing the New Year's fireworks 🎆 🥂
Native Apple Silicon support
There's no shortage of killer features in this changelog, but this one takes the cake as the biggest of them all, without any doubt. You won't have to resort to Rosetta or any such solutions anymore if you want to configure AdGuard Home on a Mac with a Silicon chip.
RFC 9000 support In DNS-over-QUIC
It's not quite over nine thousand, but it'll do. The IETF has formalized QUIC this year with RFC 9000, and DNS-over-QUIC protocol finally supports it. If you haven't tried DoQ yet, consider this a sign.
$dnsrewrite rules and other DNS rewrites will now be applied even when protection is disabled (#1558)
Another popular demand. This change only makes sense, as DNS rewrites often carry a different purpose than simply blocking ads or trackers. You still can disable them by opening the admin panel, going to Settings → General settings, and removing the check mark from the Block domains using filters and hosts files box.
Note: rules contained in system hosts files (e.g.
/etc/hosts) now have higher priority. This may result in more rewrites appearing in your Query log. If some of these rewrites are invalid, remove the corresponding lines from your hosts files or comment them out.DNS-over-HTTPS queries now use the real IP address of the client instead of the address of the proxy (#2799)
Note that this change concerns only those proxies that you've added to the list of "Trusted proxies", otherwise it would be a major security risk. We wouldn't want anything of that sort to happen to you! 🙅♀️ Right now
trusted_proxies can only be configured in AdGuardHome.yaml, but that might change in the future.Optimistic DNS cache (#2145)
To reduce latency you may make AdGuard Home respond from the cache even when the stored entry is expired, while trying to refresh them at the same time🔄 This checkbox is located in Settings → DNS settings → DNS cache configuration and it's not ticked by default. Responses made from DNS cache are marked with a special label in the Query log.
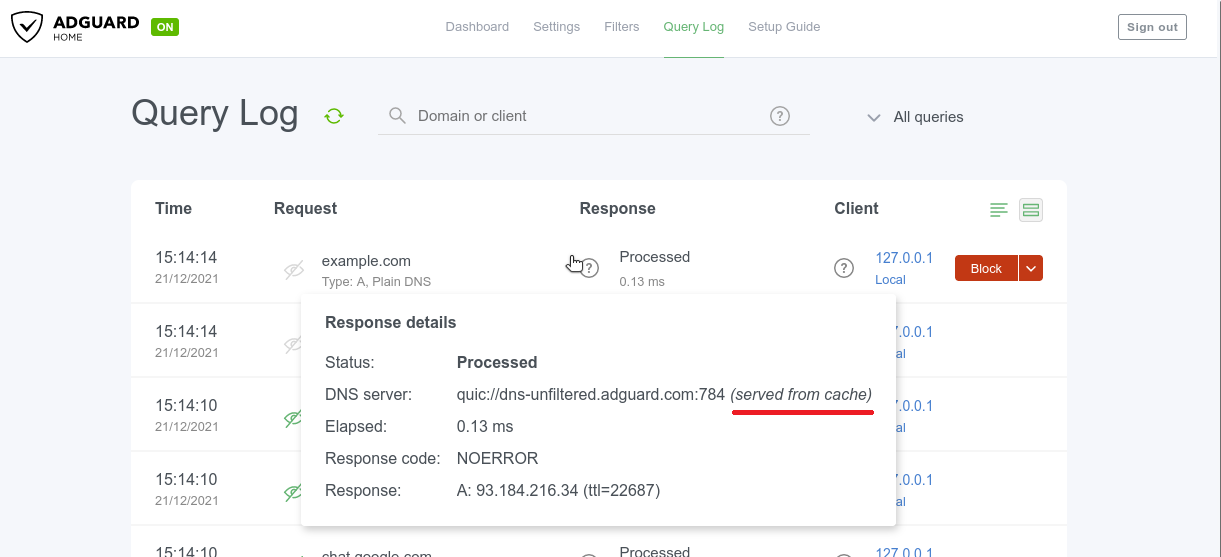
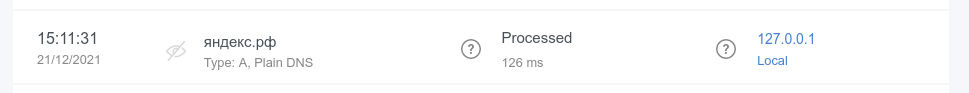
Query log search now supports internationalized domains (#3012)
Internationalized domain names (IDNAs) are domain names that contain symbols in non-Latin script/alphabet, such as
яндекс.рф or ουτοπία.δπθ.gr, for example. Previously, they were being converted to Unicode in AG Home Query log (xn--d1abqjx3f.xn--p1ai and xn--kxae4bafwg.xn--pxaix.gr in our examples), which is a detriment in most cases. Now IDNAs are displayed as is, and you can search for them without resorting to Unicode.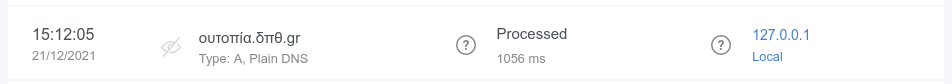
Acknowledgements
A special thanks to our open-source contributors: @Aikatsui, @anbraten, @bruvv, @DandelionSprout, @fvdm, @hnefatl, @markhicken, @p27877, and @systemcrash, as well as to everyone who filed and inspected issues, added translations, and helped us test this release! 🙏
Full Changelog
Added
Upstream server information for responses from cache (#3772). Note that old log entries concerning cached responses won't include that information.
Finnish and Ukrainian translations.
Setting the timeout for IP address pinging in the "Fastest IP address" mode through the new
fastest_timeout field in the configuration file (#1992).Static IP address detection on FreeBSD (#3289).
Optimistic cache (#2145).
New possible value of
6h for querylog_interval setting (#2504).Blocking access using client IDs (#2624, #3162).
source directives support in /etc/network/interfaces on Linux (#3257).RFC 9000 support in DNS-over-QUIC.
Completely disabling statistics by setting the statistics interval to zero (#2141).
The ability to completely purge DHCP leases (#1691).
Settable timeouts for querying the upstream servers (#2280).
Configuration file parameters to change group and user ID on startup on Unix (#2763).
Experimental OpenBSD support for AMD64 and 64-bit ARM CPUs (#2439, #3225, #3226).
Support for custom port in DNS-over-HTTPS profiles for Apple's devices (#3172).
darwin/arm64 support (#2443).freebsd/arm64 support (#2441).Output of the default addresses of the upstreams used for resolving PTRs for private addresses (#3136).
Detection and handling of recurrent PTR requests for locally-served addresses (#3185).
The ability to completely disable reverse DNS resolving of IPs from locally-served networks (#3184).
New flag
--local-frontend to serve dynamically changeable frontend files
from disk as opposed to the ones that were compiled into the binary.Changed
Port bindings are now checked for uniqueness (#3835).
The DNSSEC check now simply checks against the AD flag in the response (#3904).
Client objects in the configuration file are now sorted (#3933).
Responses from cache are now labeled (#3772).
Better error message for ED25519 private keys, which are not widely supported (#3737).
Cache now follows RFC more closely for negative answers (#3707).
$dnsrewrite rules and other DNS rewrites will now be applied even when the protection is disabled (#1558).DHCP gateway address, subnet mask, IP address range, and leases validations (#3529).
The
systemd service script will now create the /var/log directory when it doesn't exist (#3579).Items in allowed clients, disallowed clients, and blocked hosts lists are now required to be unique (#3419).
The TLS private key previously saved as a string isn't shown in API responses anymore (#1898).
Better OpenWrt detection (#3435).
DNS-over-HTTPS queries that come from HTTP proxies in the
trusted_proxies list now use the real IP address of the client instead of the address of the proxy (#2799).Clients who are blocked by access settings now receive a
REFUSED response when a protocol other than DNS-over-UDP and DNSCrypt is used.querylog_interval setting is now formatted in hours.Query log search now supports internationalized domains (#3012).
Internationalized domains are now shown decoded in the query log with the original encoded version shown in request details (#3013).
When /etc/hosts-type rules have several IPs for one host, all IPs are now returned instead of only the first one (#1381).
The setting
rlimit_nofile is now in the os block of the configuration file, together with the new group and user settings (#2763).Permissions on filter files are now
0o644 instead of 0o600 (#3198).Configuration Changes
In this release, the schema version has changed from
10 to 12.Parameter
dns.querylog_interval, which in schema versions 11 and earlier used to be an integer number of days, is now a string with a human-readable duration:# BEFORE:
'dns':
# …
'querylog_interval': 90
# AFTER:
'dns':
# …
'querylog_interval': '2160h'To rollback this change, convert the parameter back into days and change the
schema_version back to 11.Parameter
rlimit_nofile, which in schema versions 10 and earlier used to be on the top level, is now moved to the new os object:# BEFORE:
'rlimit_nofile': 42
# AFTER:
'os':
'group': ''
'rlimit_nofile': 42
'user': ''To rollback this change, move the parameter on the top level and change the
schema_version back to 10.Deprecated
Go 1.16 support. v0.108.0 will require at least Go 1.17 to build.
Fixed
EDNS0 TCP keepalive option handling (#3778).
Rules with the
$denyallow modifier applying to IP addresses when they shouldn't (#3175).The length of the EDNS0 client subnet option appearing too long for some upstream servers (#3887).
Invalid redirection to the HTTPS web interface after saving enabled encryption settings (#3558).
Incomplete propagation of the client's IP anonymization setting to the statistics (#3890).
Incorrect
$dnsrewrite results for entries from the operating system's hosts file (#3815).Matching against rules with
| at the end of the domain name (#3371).Incorrect assignment of explicitly configured DHCP options (#3744).
Occasional panic during shutdown (#3655).
Addition of IPs into only one as opposed to all matching ipsets on Linux (#3638).
Removal of temporary filter files (#3567).
Panic when an upstream server responds with an empty question section (#3551).
9GAG blocking (#3564).
DHCP now follows RFCs more closely when it comes to response sending and option selection (#3443, #3538).
Occasional panics when reading old statistics databases (#3506).
reload service action on macOS and FreeBSD (#3457).Inaccurate using of service actions in the installation script (#3450).
Client ID checking (#3437).
Discovering other DHCP servers on
darwin and freebsd (#3417).Switching listening address to unspecified one when bound to a single specified IPv4 address on Darwin (macOS) (#2807).
Incomplete HTTP response for static IP address.
DNSCrypt queries weren't appearing in query log (#3372).
Wrong IP address for proxied DNS-over-HTTPS queries (#2799).
Domain name letter case mismatches in DNS rewrites (#3351).
Conflicts between IPv4 and IPv6 DNS rewrites (#3343).
Letter case mismatches in
CNAME filtering (#3335).Occasional breakages on network errors with DNS-over-HTTP upstreams (#3217).
Errors when setting static IP on Linux (#3257).
Treatment of domain names and FQDNs in custom rules with
$dnsrewrite that use the PTR type (#3256).Redundant hostname generating while loading static leases with empty hostname (#3166).
Domain name case in responses (#3194).
Custom upstreams selection for clients with client IDs in DNS-over-TLS and DNS-over-HTTP (#3186).
Incorrect client-based filtering applying logic (#2875).
Removed
Go 1.15 support.
AdGuard Home 0.106.3


公開日: 2021年5月19日
More! More bugfixes! 🧟♀️
But this time, for a change, there's a couple of new minor features to go with them. Hope you don't mind 🤷♂️
A special thanks to our open-source contributor, @ashishwt, as well as to everyone who filed and inspected issues, added translations, and helped us to test this release!
Added
Changed
Add microseconds to log output.
Fixed
Intermittent "Warning: ID mismatch" errors #3087.
Error when using installation script on some ARMv7 devices #2542.
Local PTR request recursion in Docker containers #3064.
Ignoring client-specific filtering settings when filtering is disabled in general settings #2875.
Disallowed domains are now case-insensitive #3115.
Other minor fixes and improvements.
AdGuard Home 0.106.2


公開日: 2021年5月19日
It's not Friday? Not a problem! We defy the tradition of Friday hotfixes by rushing another one out a day earlier 🙌
A special thanks to our open-source contributor, @jankais3r, as well as to everyone who filed issues, added translations, and helped us to test this release!
Fixed
AdGuard Home 0.106.1


公開日: 2021年5月19日
We had a release a couple days ago. You all knew it would come to this. 🦸
It's Friday.
It's hotfix time! 🔥
Nothing serious though, we didn't even break anything. Just cleaning up some minor bugs. 🧹
Fixed
AdGuard Home 0.106.0


公開日: 2021年5月19日
Quite a lot of changes this time around, even if there aren't as many standouts as in some of the previous updates. We're sure that you'll be able to find a line or two in the changelog that speaks to you!
And one of the reasons for that is the constant support from the community. 👥👥 Special thanks to our open-source contributors: @jvoisin and @Paraphraser, as well as to everyone who filed issues, added translations, and helped us to test this release! 🙇
The ability to set up custom upstreams to resolve PTR queries for local addresses and to disable the automatic resolving of clients' addresses #2704
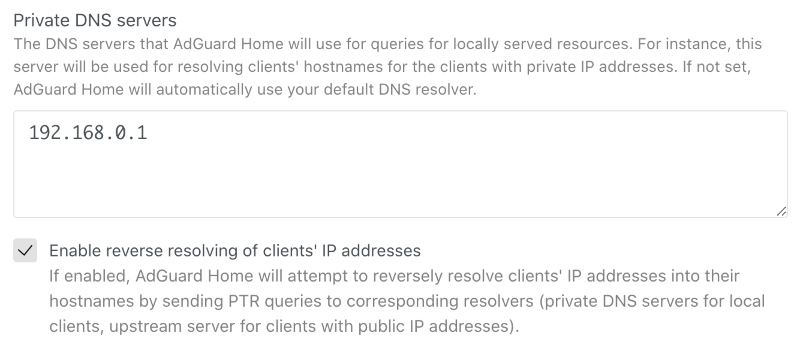
This option will improve your DNS privacy when it comes to addressing local resources. Give it a go unless you want to share your private data with googles of the world.
Search by clients' names in the query log #1273
There's not much that can be said about this feature, it's quite self-explanatory: now you can search up queries by specific clients. 🤷♀️
However, we wanted to highlight it anyway since so many of you have asked for it for quite a while. Hopefully, we delivered! 😅
Added
The ability to block user for login after configurable number of unsuccessful attempts for configurable time #2826.
$denyallow modifier for filters #2923.Hostname uniqueness validation in the DHCP server #2952.
Hostname generating for DHCP clients which don't provide their own #2723.
New flag
--no-etc-hosts to disable client domain name lookups in the operating system's /etc/hosts files #1947.Logging of the client's IP address after failed login attempts #2824.
Verbose version output with
-v --version#2416.The ability to serve DNS queries on multiple hosts and interfaces #1401.
Changed
Quality of logging #2954.
The access to the private hosts is now forbidden for users from external networks #2889.
The reverse lookup for local addresses is now performed via local resolvers #2704.
Stricter validation of the IP addresses of static leases in the DHCP server with regards to the netmask #2838.
Stricter validation of
$dnsrewrite filter modifier parameters #2498.New, more correct versioning scheme #2412.
Deprecated
Go 1.15 support. v0.107.0 will require at least Go 1.16 to build.
Fixed
Multiple answers for
$dnsrewrite rule matching requests with repeating patterns in it #2981.Root server resolving when custom upstreams for hosts are specified #2994.
Inconsistent resolving of DHCP clients when the DHCP server is disabled #2934.
Comment handling in clients' custom upstreams #2947.
Overwriting of DHCPv4 options when using the HTTP API #2927.
Assumption that MAC addresses always have the length of 6 octets #2828.
Support for more than one
/24 subnet in DHCP #2541.Invalid filenames in the
mobileconfig API responses #2835.Removed
Go 1.14 support.
AdGuard Home 0.105.2


公開日: 2021年3月15日
There are big flashy updates, and there are seemingly unassuming ones, which constitute, however, the backbone of any successful project. This is the latter, as you may have guessed. You'll find here a heap of bugfixes and a security update for CVE-2021-27935.
Security
Session token doesn't contain user's information anymore (#2470).
Fixed
Incomplete hostnames with trailing zero-bytes handling (#2582).
Wrong DNS-over-TLS ALPN configuration (#2681).
Inconsistent responses for messages with EDNS0 and AD when DNS caching is
enabled (#2600).
Incomplete OpenWrt detection (#2757).
DHCP lease's
expired field incorrect time format (#2692).Incomplete DNS upstreams validation (#2674).
Wrong parsing of DHCP options of the
ip type (#2688).
AdGuard Home v0.105.1


公開日: 2021年2月16日
Have you ever thought about why traditions are so important?🧙♂️ Traditions help us remember that we are part of a history that defines our past, shapes who we are today, and who we are likely to become. This is why we at AdGuard respect our traditions, and the most important one is pushing the inevitable hotfix right after every major update.🔥🔧
Jokes aside, here's the list of things fixed and improved in this hotfix.
Changed
"Permission denied" errors when checking if the machine has a static IP no
longer prevent the DHCP server from starting (#2667).
The server name sent by clients of TLS APIs is not only checked when
strict_sni_check is enabled (#2664).Fixed
Error when enabling the DHCP server when AdGuard Home couldn't determine if
the machine has a static IP.
Optical issue on custom rules (#2641).
Occasional crashes during startup.
The field
"range_start" in the GET /control/dhcp/status HTTP API response
is now correctly named again (#2678).DHCPv6 server's
ra_slaac_only and ra_allow_slaac settings aren't reset to
false on update any more (#2653).The
Vary header is now added along with Access-Control-Allow-Origin to
prevent cache-related and other issues in browsers (#2658).The request body size limit is now set for HTTPS requests as well.
Incorrect version tag in the Docker release (#2663).
DNSCrypt queries weren't marked as such in logs (#2662).
AdGuard Home 0.105.0


公開日: 2021年2月12日
We took our sweet time with this update, but you'll most certainly find it to be worth the wait. The changelog contains three absolute 💥bangers and a laundry list of lesser changes.
🕵️♂️ Client ID support for DNS-over-HTTPS, DNS-over-QUIC, and DNS-over-TLS #1387
This feature would be really useful to those of you who run an encrypted DNS resolver on a public server. In short, you can now identify your devices not just by their IP address (which is, frankly, not too useful in a public server scenario 🤷♀️), but by using a special "Client ID".

Here's how it works:
First, you add a client and specify an arbitrary string as its "Identifier", for instance,
my-iphone.On the client device you can now configure:
DNS-over-HTTPS: https://example.org/dns-query/my-iphoneQueries and stats are now properly attributed to your device.

🔐 AdGuard as a DNSCrypt-resolver #1361
DNSCrypt was the very first DNS encryption protocol that got some traction. It may not be as popular as DoH/DoT/DoQ now, but it is still viable. Moreover, performance-wise DNSCrypt is better than any of them. And now that v0.105.0 is out, AdGuard Home can be configured to work as a DNSCrypt resolver!
However, here goes the tricky part. We haven't yet exposed these settings to the Web admin panel so if you want to have DNSCrypt, you'll need to follow this instruction and do it via editing the configuration file (
AdGuardHome.yaml). Not that it would scare you off, would it? 🤓
Regarding DNSCrypt clients - AdGuard for Android, Windows and iOS support it, Mac will get its support pretty soon. Besides that, here is a long list of client software that supports it as well.
🆎 $dnsrewrite and $dnstype modifiers #2102#2337
AdGuard Home now supports two more powerful rule modifiers that will help blocklists' maintainers.
$dnstype lets you narrow down the rule scope and apply it only to queries of a specific type(s). For instance, Apple devices now support HTTPS DNS query type. While being generally a good thing, this new type may sometimes be harmful😲. By using $dnstype you can block it completely using a simple rule like this: $dnstype=HTTPS$dnsrewrite is another powerful modifier that allows you to modify DNS responses. Note that this modifier is much more powerful compared to something like a hosts file.Here are some examples:
||example.org^$dnsrewrite=SERVFAIL;; - return SERVFAIL for example.org and all it's subdomains|test.example.org^$dnsrewrite=NOERROR;TXT;hello_world - add a TXT record for test.example.org|example.org^$dnsrewrite=example.com - redirect example.org to example.com|example.org^$dnsrewrite=1.1.1.1 - redirect example.org to example.comYou can find more examples in the documentation.
Added
The host checking API and the query logs API can now return multiple matched rules #2102
Detecting of network interface configured to have static IP address via
/etc/network/interfaces#2302A 5 second wait period until a DHCP server's network interface gets an IP address #2304
HTTP API request body size limit #2305
Changed
Access-Control-Allow-Origin is now only set to the same origin as the domain, but with an HTTP scheme as opposed to *#2484workDir now supports symlinks.Stopped mounting together the directories
/opt/adguardhome/conf and /opt/adguardhome/work in our Docker images #2589When
dns.bogus_nxdomain option is used, the server will now transform responses if there is at least one bogus address instead of all of them #2394. The new behavior is the same as in dnsmasq.Made the mobileconfig HTTP API more robust and predictable, add parameters and improve error response #2358
Improved HTTP requests handling and timeouts #2343
Our snap package now uses the
core20 image as its base #2306Deprecated
Go 1.14 support. v0.106.0 will require at least Go 1.15 to build.
The
darwin/386 port. It will be removed in v0.106.0.The
"rule" and "filter_id" fields in GET /filtering/check_host and
GET /querylog responses. They will be removed in v0.106.0 #2102Fixed
Autoupdate bug in the Darwin (macOS) version #2630
Inability to set DNS cache TTL limits #2459
Possible freezes on slower machines #2225
A mitigation against records being shown in the wrong order on the query log page #2293
A JSON parsing error in query log #2345
Incorrect detection of the IPv6 address of an interface as well as another infinite loop in the
/dhcp/find_active_dhcp HTTP API #2355Removed
The undocumented ability to use hostnames as any of
bind_host values in the configuration. Documentation requires them to be valid IP addresses, and now the implementation makes sure that that is the case #2508Dockerfile#2276. Replaced with the script scripts/make/build-docker.sh which uses scripts/make/Dockerfile.Support for pre-v0.99.3 format of query logs #2102
AdGuard Home 0.104.3


公開日: 2021年2月12日
Bugfixes... 😌 There's something about them that we just can't resist. We always want more! 🧟
When there's nothing more to fix, we just roll out a new major update, introduce some fresh bugs and start all over. It's a circle of life ☯️
Luckily, there are still some to prey upon in v0.104. Have a look at what we've fixed this time:
Fixed
Don't expose the profiler HTTP API #2336
Load query logs from files after loading the ones buffered in memory #2325
Don't show Unnecessary errors in logs when switching between query log files #2324
Don't show
404 Not Found errors on the DHCP settings page on Windows. Show that DHCP is not currently available on that OS instead #2295Fix an infinite loop in the
/dhcp/find_active_dhcp HTTP API method #2301Various internal improvements
AdGuard Home 0.104.1


公開日: 2021年2月12日
Those who pay close attention to AdGuard Home releases know that we keep hotfixes close to our hearts 🔥♥️ This time we held for as long as we could, but ultimately gave in to the urge 😔
Here's a patch to v0.104 with some fixes and minor improvements.
Fixed
Solve the
permission denied error when launching a DHCP server on Linux using Snap#2228. Users experiencing this issue should refresh their snap and call:
snap connect adguard-home:network-controlThis won't be required in the future versions.
Use matching fonts in the Custom Filters textarea #2254
Show the correct query type for DNS-over-QUIC queries in query log #2241
Increase the default number of simultaneous requests to improve performance #2257
Always set a secondary DNS in DHCP #1708
Improve stability on DNS proxy restart #2242
Improve logging on DNS proxy restart #2252
Don't show a “Loading” message and don't rerequest logs once we've reached the end of logs on the query log page #2229
Various internal improvements.
AdGuard Home 0.104.0


公開日: 2021年2月12日
We have something special for y'all today. Not just an implementation of a new feature but the first ever implementation of a new feature! 😮 This is about DNS-over-QUIC, a new DNS encryption protocol — read on to learn more.
Ah, yes, there's also a bunch of other good stuff, too: DHCP-related changes, a .mobileconfig generator for iOS and macOS, and a handful of other enhancements and bugfixes.
DNS-over-QUIC support #2049
AdGuard Home now natively supports a new DNS encryption protocol called DNS-over-QUIC. DoQ standard is currently in the draft state, and AdGuard Home (and dnsproxy) is it's first open-source implementation.🥇

So what's good about it? 🤔 Unlike DoH and DoT, it uses QUIC as a transport protocol and finally brings DNS back to its roots — working over UDP. It brings all the good things that QUIC has to offer — out-of-the-box encryption, reduced connection times, better performance when data packets are lost. Also, QUIC is supposed to be a transport-level protocol and there are no risks of metadata leaks that could happen with DoH. 🔒
At this moment, the only major public DNS resolver that provides DNS-over-QUIC is AdGuard DNS. 😎 Use
quic://dns-unfiltered.adguard.com in the upstreams settings to start using AdGuard DNS "Non-Filtering".DHCP rework: DHCP6 support, custom DHCP options
We did a huge rework of our DHCP server implementation. Thanks to it, AdGuard Home now supports DHCP6 and allows setting custom DHCP options.
Please note that in order to set DHCP options, you'll need to edit the configuration file.
Add support for DHCPv6: #779
DHCPv6 RA+SLAAC: #2076
DHCP: automatic hostnames: #1956
Add DHCP Options: #1585
iOS and MacOS .mobileconfig generator: #2110
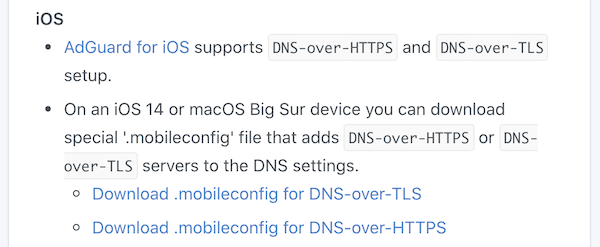
iOS 14 and macOS Big Sur natively support DNS-over-HTTPS and DNS-over-TLS. However, it's not that simple to configure them — you need to install a special "configuration profile" for that. 🤯 In order to make things easier, AdGuard Home can generate these configuration profiles for you. Just head to "Setup Guide" -> "DNS Privacy" and scroll to iOS.
Binary transparency
AdGuard Home binaries are now signed with our GPG key and you can now easily verify that they really come from us: https://github.com/AdguardTeam/AdGuardHome/wiki/Verify-Releases
Other improvements
Allow entering comments to the Upstreams box: #2083
Load upstreams list from a file: #1680
Add ARMv8 to future releases, potentially append a v8 binary to the most recent non-beta release: #2125
Redesign query logs block/unblock buttons: #2050
Treat entries starting with "/" as "://" under specific circumstances: #1950
Use "Null IP" instead of NXDOMAIN by default: #1914
Bootstrap with TCP upstreams: #1843
Add block and unblock buttons to 'check the filtering' result: #1734
ipset feature support: #1191
Add Belarusian and Chinese Traditional HK languages: #2106
Add new language: en-silk: #1796
Use DOH or DOT as bootstrap: #960
Fixed
Reverse lookups return empty answers for hosts from /etc/hosts: #2085
Static lease hostnames are overridden by client-identifier: #2040
Query log doesn't display name for blocked services: #2038
Custom filter editor works with delay: #1657
Incorrect link address: #2209
Smartphone compatible design for user interface: #2152
Misleading information during service installation: #2128
Remove the limit on cache-min-ttl, 3600: #2094
Cannot change minimum TTL override in UI: #2091
Optical Issue on mobile phone: #2090
Setting a large DNS Cache Size in the Web GUI will exceed the unit32 range.: #2056
Clients requests aren't counted properly: #2037
Publish privacy policy on front page (README.md): #1960
Sorting various IP Address Columns in the UI (eg in dhcp static leases) does not sort correctly. They are treated as strings instead of numeric.: #1877
Requests count for clients with CIDR IP addresses: #1824



