AdGuard Home 0.107.76


Release date: May 21, 2026
They say: don’t fix it if it’s not broken. But what if it is, in fact, broken? Like the cache we may have accidentally messed up during the last update? For such cases, there are hotfixes! Make sure to install today’s update in order to fix the cache on your AdGuard Home.
AdGuard Home 0.107.75


Release date: May 19, 2026
🔒 This update gives AdGuard Home a solid security upgrade — think of it as tightening the locks and double-checking the doors.
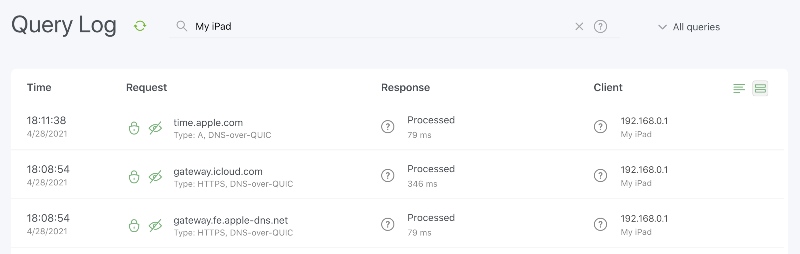
We’ve fixed a critical vulnerability affecting DNS-over-QUIC and DNS-over-HTTPS that could put your DNS privacy at risk. The gap is now closed, and your encrypted traffic is back to traveling through a properly armored tunnel.
We also updated Go to the latest version, sweeping out known vulnerabilities in its libraries.
AdGuard Home 0.107.74


Release date: April 16, 2026
As with everything in life, the best things are only the best because they stand out from the mundane. Without regular there would be no exceptional.
… all these words to say that this AdGuard Home update is the ‘boring’ one, with mostly bug fixes and security updates — so that the next time we add something new, it would feel fresh and exciting!
AdGuard Home 0.107.73


Release date: March 10, 2026
We are releasing this hotfix to address a recently discovered critical vulnerability that could allow users to bypass authentication and gain full access to AdGuard Home without valid credentials. We strongly recommend updating your AdGuard Home clients immediately.
AdGuard Home 0.107.72


Release date: February 25, 2026
The first release of the year is always important — it sets the tone for the months ahead 📆
The way we kick things off in 2026 may not be flashy, but it’s a solid mix: the new way of handling TLS certificate updates, a couple of other, minor new features, some configuration changes, a couple of key fixes, and the usual security update.
Stay tuned for more goodies to come!
AdGuard Home 0.107.69


Release date: October 30, 2025
AdGuard Home v0.107.69 is here — just a quick pit stop to fix two pesky bugs that tried to sneak past us. No new features this time, but everything should now run a bit smoother (and those bugs have been shown the door).
AdGuard Home 0.107.68


Release date: October 23, 2025
Let's get “the usual” out of the way: we’ve made some security updates, as we always do, and even managed to make do without any bug fixes this time, for better or for worse. But let’s focus on the main course: new option to enable and disable DNS rewrite rules 🚦
This was one of the earlier feature requests, and we are happy to finally deliver. You can enable and disable DNS rewrite rules all at once or do so on an individual rewrite basis — both by editing YAML files or via UI.
AdGuard Home 0.107.66


Release date: September 15, 2025
You may have the best software in the world, but if people can’t access it, it’s as good as useless. This is why in today’s update we made it a priority to fix a couple of authentication errors — so that you can always log in and use AdGuard Home to its fullest. Couple it with the usual security updates and a pinch of other changes, and you have v0.107.66 on your hands! 🙌
AdGuard Home 0.107.64


Release date: July 29, 2025
Unlike with chickens and eggs, with bugs and bugfixes, unfortunately, the bugs always come first. At least the new update is here to fix them all! 🥚🐔
Today we have bugfixes for every taste: security bugfixes, cache responses TTL bugfixes, even DNSCrypt certificates bugfixes. And you don't even have to choose — you can have them all with this new version of AdGuard Home.
AdGuard Home 0.107.63


Release date: June 30, 2025
It’s not always the big issues: sometimes what you need is a few fixes and tweaks to pump up the overall stability 🔩
AdGuard Home 0.107.62


Release date: May 29, 2025
Many claim to be client-oriented; we're proud to say that AdGuard Home is
$client-oriented, as in this update we've fixed (among others) the bug that prevented the rules containing the client modifier from working. 👥We have also improved AdGuard Home's security by updating the Go version to shore up some vulnerabilities, as usual.
AdGuard Home 0.107.60


Release date: April 17, 2025
If you are reading through these release notes, you must be a true power user of AdGuard Home, as this update isn’t the most flashy one. There are no exciting new features, but there are patches to Go vulnerabilities, UI and docker updates, and a couple of bugfixes.
AdGuard Home 0.107.59


Release date: March 21, 2025
This hotfix addresses the bug that was introduced with the previous update, namely the bug that prevented users from entering anything into the search box in the Query log. We also took this opportunity to include another fix for the incorrect functioning of the client modifier.
Acknowledgments
A special thanks to our community moderators team, @AdguardTeam/community-moderators, as well as to everyone who filed and inspected issues, added translations, and helped us test this release!
AdGuard Home 0.107.58


Release date: March 20, 2025
Here’s a philosophical question for you: if a release contains more bugfixes than usual, is it good or is it bad? 🤔
Luckily, we are developers and not philosophers, so let’s state some facts and leave thought experiments to those wiser than us. And the facts are, we’ve fixed a bunch of bugs in this update, but also added a neat little feature that we’d like to elaborate on.
An improved tool to check DNS queries
If you are serious about protecting your privacy and dealing with ads, chances are you have loads of rules, both as filter lists and as parts of a custom ruleset. Now, any time you’re tweaking your filter arsenal, there is an easy way to check if a certain DNS query will be blocked. We’ve built upon the already-existing tool and added options to indicate DNS record type and specific client, either by IP address or by ClientID. Enter the information and behold all the rules that match your request. Bonus feature: you can unblock any domain right then and there. Happy blocking!
AdGuard Home 0.107.57


Release date: February 21, 2025
The year 2025 is only picking up steam, but some of us already need a time out 🕙 Speaking of timeouts, in the new version we've added the ability to specify the upstream timeout in the Web UI, alongside with some bug fixes and security updates.
AdGuard Home 0.107.56


Release date: January 24, 2025
We are steadily picking up the pace in the new year, starting with this small update. 🏃 Inside are some fresh bugfixes, a new API, and an updated Go version to shore up some vulnerabilities.
AdGuard Home 0.107.55


Release date: December 12, 2024
Time for another release! We encourage all Windows users to play close attention as it addresses a bug that has been affecting some Windows installations. For the rest of AdGuard Home aficionados, we've updated Go version to shore up some vulnerabilities and have dealt with a couple leaks 🚰
AdGuard Home 0.107.54


Release date: November 6, 2024
This AdGuard Home update will be of particular interest to Windows users. We've made the necessary security improvements for Windows that we didn’t have time to implement in the previous version. But there’s always something for everyone in AdGuard Home updates, not just for Windows enjoyers: filters perform better now and, of course, we've done our fair share of bug fixing.
AdGuard Home 0.107.53


Release date: October 3, 2024
It's been a while since we postponed the next AdGuard Home update for a few months. But of course, we had a good reason for it: with the help of community members (we are very thankful to you! 🙏), we discovered two vulnerabilities and have been working on patching them. Testing the solutions took a bit longer than expected, but in the end, we believe in quality over speed.
Luckily, it's not all patching vulnerabilities and fixing bugs; we've made some improvements, too. For example, we've added support for 64-bit RISC-V architecture and Ecosia search engine to Safe Search. Find the complete changelog below.
AdGuard Home 0.107.52


Release date: July 4, 2024
In this release we have fixed a number of bugs, migrated our front-end to TypeScript and updated our front-end libraries to improve the quality of development and your user experience.
AdGuard Home 0.107.51


Release date: June 6, 2024
A small bugfix and security release. We are working on new features in future releases.
AdGuard Home 0.107.50


Release date: May 24, 2024
They say, if it isn't broken — don't fix it. Unfortunately, this is not the case with the last AdGuard Home update 😓 A small portion of users haven't been able to start AdGuard Home at all, and so we are rolling out this hotfix.
AdGuard Home 0.107.49


Release date: May 21, 2024
Fast approaching summer promises everyone its warmth, and all kinds of bugs are crawling from under the rocks and twigs to enjoy the sun 🌞. Here's a patch to make sure that they stay in the grass and nowhere near AdGuard Home.
AdGuard Home 0.107.48


Release date: April 5, 2024
After the last update it became possible for banned users to make DNS queries over encrypted protocols. This behavior, of course, was not intended, and is fixed by this hotfix.
We apologize for this oversight and will do our best to avoid repeating such mistakes in the future.
AdGuard Home 0.107.47


Release date: April 4, 2024
Another security and bug fix update, but this time we also fix a time zone selection issue and a few other annoying bugs!
AdGuard Home 0.107.46


Release date: March 20, 2024
As promised in the notes for the previous release, this update brings some quality-of-life improvements as well as a few bug fixes 🔧.
AdGuard Home 0.107.45


Release date: March 7, 2024
This is a small release containing a security update, a few fixes, and a small feature. More to come soon!
AdGuard Home 0.107.44


Release date: February 6, 2024
They say, when you do your job well, nobody ever notices it. We'd like to believe this is the case, as today's update won't knock your socks off with any new major features or anything of the sort. Instead, we “oil the gears” with spot changes and assorted bugfixes 🔧.
AdGuard Home 0.107.43


Release date: December 11, 2023
Everybody needs something to keep themselves warm during the cold winter days ❄️. Many people opt for hot coffee ☕ or hot chocolate, but we at AdGuard prefer hotfixes 🔥.
AdGuard Home 0.107.42


Release date: December 7, 2023
As the winter holidays approach, many of us begin to think about what gifts we will give and receive 🎁. With AdGuard, the holidays come early: we decided not to wait too long and present you with this new version of AdGuard Home today!
Among the long-awaited features in this release are the option to enable caching for persistent clients with custom DNS upstream configuration and the option to disable plain DNS for better security.
AdGuard Home 0.107.41


Release date: November 13, 2023
Bugs are as certain as the change of the seasons 📆. However, in this release we have not only fixed quite a few of them, but also added some features that will make it easier to configure AdGuard Home and protect it from DDoS attacks!
AdGuard Home 0.107.40


Release date: October 18, 2023
What could be spookier than bugs preventing people from using their networks? Luckily, we’re here to bust them with this hotfix release!
AdGuard Home 0.107.39


Release date: October 11, 2023
The spooky season may soon be upon us 🎃, but we’re not afraid to ship a new release with some new features and a few bug fixes!
AdGuard Home 0.107.38


Release date: September 11, 2023
Releases are like fruit: the tastier the apple, the more likely there’s a bug in it somewhere. It turns out that our previous release was quite delicious! This hotfix is meant to deal with all the remaining bugs.
AdGuard Home 0.107.37


Release date: September 9, 2023
The summer has come and gone, leaving behind a decent harvest of long-awaited features and improvements, with a side order of bug fixes!
Service blocking pause schedule
Users can now easily set pauses for the service blocking filter. For example, you can block social networks throughout the day, but allow yourself 30 minutes after work.
While this feature has been in internal development for several months, in this release we are glad to finally present it in the web UI.
Fallback servers
Another long-awaited feature is the fallback servers, which are used when the main upstream DNS servers cannot be reached.
The syntax there is the same as for the main upstream input, so you can set different fallback servers for different domains.
Upstream statistics
Another feature related to DNS upstreams is the new upstream statistics shown on the dashboard.
These allow users to see which upstreams are faster than others, as well as which upstreams are being used the most.
Acknowledgements
A special thanks to our open-source contributor, @ssrahul96, as well as to everyone who filed and inspected issues, added translations, and helped us test this release!
AdGuard Home 0.107.36


Release date: August 2, 2023
A small bugfix and security release. We are working on new features in future releases.
AdGuard Home 0.107.35


Release date: July 26, 2023
In the previous release, we optimized the filtering-rule list updates, achieving up to three times speedup in some cases. However, the new algorithm proved to be too strict, so in this release we have relaxed its validations while maintaining the optimization for more typical filtering-rule lists 🏎️
As always, there are other minor bug fixes in this release as well.
AdGuard Home 0.107.34


Release date: July 12, 2023
This release improves the security of AdGuard Home and fixes a few larger issues.
Safe Browsing and CPU spikes
Back in June we released a security update to AdGuard Home with a few bug fixes. Ironically, it brought about another bug. Safe Browsing and Parental Control weren't working properly since then, which in some cases led to lowered performance, random crashes, and huge CPU spikes.
It took us an entire month to get to the bottom of this, and it certainly would have taken even longer if not for the awesome community members: @bigwookie, @TheCableGuy99, and others. It turned out that “The Big Bug” was, in fact, three smaller bugs in a trenchcoat. And they were all mercilessly dealt with in this update.
Docker HEALTHCHECK
Docker users should note that the Docker
HEALTHCHECK mechanism has been removed, since it was causing a lot of issues, especially when used with Podman and other popular Docker tools.Acknowledgements
A special thanks to our open-source contributor, @Jiraiya8, as well as to everyone who filed and inspected issues, added translations, and helped us test this release!
AdGuard Home 0.107.33


Release date: July 3, 2023
Bugs need to be fixed, and that's just what we did in this release 🔧. Besides that, we've been working on internal improvements that will make it easier to add new features in future releases.
AdGuard Home 0.107.32


Release date: June 13, 2023
A hotfix release to fix a major issue in the previous release.
AdGuard Home 0.107.31


Release date: June 8, 2023
A hotfix release to fix two major issues in the previous release.
AdGuard Home 0.107.30


Release date: June 7, 2023
A small bugfix and security release. We are working on new features in future releases.
AdGuard Home 0.107.29


Release date: April 18, 2023
Our previous release took place on the International Day of Human Space Flight, but it seems like our rocket was not able to take off smoothly. In this release, we’re fixing a few annoying bugs as well as putting a shine on the client ignoring feature.
AdGuard Home 0.107.28


Release date: April 12, 2023
Finally, a nice big update with lots of new features :relieved:. Among them, we want to highlight a couple of noticeable quality-of-life changes that have been requested for a long time.
Global protection pause
First of all, there's now a way to pause protection for a set period, ranging from 30 seconds to an entire day. This is great for when you need to access a site that's mistakenly blocked, or when you want to temporarily disable AdGuard Home without turning it off completely.
 Once the pause time is out, AdGuard Home will switch protection back on.
Once the pause time is out, AdGuard Home will switch protection back on.Better Safe Search controls
Secondly, you can now fine-tune Safe Search settings by enabling or disabling it for specific services like Google, Bing, YouTube, and more.

The same can be done on a per-client basis as well. Another minor improvement to the Safe Search is better support for IPv6 addresses.
AdGuard Home 0.107.27


Release date: April 5, 2023
This is a security and bugfix release. There are no changes besides the update of the Go programming language version and fixes to a few bugs. More substantial changes are to come in the subsequent updates.
AdGuard Home 0.107.26


Release date: March 9, 2023
Today’s one features further customization options for outbound queries, new option to drop requests based on their question types, and various bugfixes.
AdGuard Home 0.107.25


Release date: February 21, 2023
This is a hotfix release to prevent panics when using unencrypted DNS-over-HTTP, which affected people running AdGuard Home behind an HTTP reverse proxy.
AdGuard Home 0.107.24


Release date: February 16, 2023
Ignoring talkative colleagues can be tough in real life 🤫. Fortunately, there are more options in the digital world. This new release of AdGuard Home adds a way to exclude certain hostnames from the query log and statistics, which can help with devices and apps that like to talk too much.
AdGuard Home 0.107.23


Release date: February 1, 2023
Fonts! Сolors! Buttons! Everybody likes to discuss the design of a user interface, but we like to ship bug fixes and new features to our users even more 🚢.
Besides the tweaks in the dark theme, this release includes support for the DNS64 standard, a couple of new blockable services, as well as a few bug fixes and internal improvements.
AdGuard Home 0.107.22


Release date: January 19, 2023
One thing that nobody likes during long nights is a user interface that is way too bright to look at 🔦. In this release, AdGuard Home finally delivers one of its most commonly requested features: the dark theme!
The new dark theme is currently still experimental, and there are a few rough edges here and there. If you want to report them, please follow the instructions in issue #5375.
AdGuard Home 0.107.21


Release date: December 24, 2022
A hotfix for the cold season ⛄.
AdGuard Home 0.107.20


Release date: December 7, 2022
While the goalkeepers at the World Cup are doing their best to keep their goal safe, we’re doing our best to keep our users safe and making sure they receive the latest security updates 🛡️ as soon as possible. As a nice bonus, we have also added a button to easily clear the DNS cache.
AdGuard Home 0.107.19


Release date: November 23, 2022
Twitter may be in flames 🔥, but you can't get away from social media just as easily. Well, maybe it's become a little easier now, thanks to the contribution from @sandervankasteel: AdGuard Home can now block a few most popular Mastodon instances. Take a break from doomscrolling, you deserve it!
We've also added the --update command-line option to update AdGuard Home without the need to deal with the UI.
AdGuard Home 0.107.17


Release date: November 2, 2022
Despite this release appearing around Halloween, it shouldn't be spooky at all. The main novelty is that the list of services blockable with a single click is now synchronized with AdGuard DNS to make the user experience more unified across AdGuard services. We've also improved support for HTTP/3 as well as fixed a few annoying bugs.
AdGuard Home 0.107.16


Release date: October 7, 2022
This is a security release. There are no new changes besides the update of the Go programming language version. More substantial changes are to come in the subsequent updates.
Full Changelog
Security
Go version has been updated to prevent the possibility of exploiting the CVE-2022-2879, CVE-2022-2880, and CVE-2022-41715 Go vulnerabilities fixed in Go 1.18.7.
AdGuard Home 0.107.15


Release date: October 3, 2022
Sometimes, even a hotfix needs a hotfix. In the previous release, our mitigations turned out to be too restrictive, preventing some AdGuard Home features from working properly. In this release, we fix this along with a few other bugs.
We have also added experimental support for the HTTP/3 standard in the UI, DNS upstreams, and DNS clients!
Full Changelog
Security
As an additional CSRF protection measure, AdGuard Home now ensures that requests that change its state but have no body (such as POST /control/stats_reset requests) do not have a Content-Type header set on them #4970.
Added
Experimental HTTP/3 Support
See #3955 and the related issues for more details. These features are still experimental and may break or change in the future.
DNS-over-HTTP/3 DNS and web UI client request support. This feature must be explicitly enabled by setting the new property
dns.serve_http3 in the configuration file to true.DNS-over-HTTP upstreams can now upgrade to HTTP/3 if the new configuration file property
dns.use_http3_upstreams is set to true.Upstreams with forced DNS-over-HTTP/3 and no fallback to prior HTTP versions using the h3:// scheme.
Fixed
only application/json is allowed errors in various APIs #4970.
AdGuard Home 0.107.14


Release date: September 29, 2022
This is a security release. Users are encouraged to update AdGuard Home as soon as possible.
Full Changelog
Security
A Cross-Site Request Forgery (CSRF) vulnerability has been discovered. The CVE number is to be assigned. We thank Daniel Elkabes from Mend for reporting this vulnerability to us.
SameSite PolicyThe
SameSite policy on the AdGuard Home session cookies has been upgraded to Lax. Which means that the only cross-site HTTP request for which the browser is allowed to send the session cookie is navigating to the AdGuard Home domain.Users are strongly advised to log out, clear browser cache, and log in again after updating.
Removal Of Plain-Text APIs (BREAKING API CHANGE)
We have implemented several measures to prevent such vulnerabilities in the future, but some of these measures break backwards compatibility for the sake of better protection.
The following APIs, which previously accepted or returned
text/plain data, now accept or return data as JSON. All new formats for the request and response bodies are documented in openapi/openapi.yaml and openapi/CHANGELOG.md.GET /control/i18n/current_language;POST /control/dhcp/find_active_dhcp;POST /control/filtering/set_rules;POST /control/i18n/change_language.Stricter
Content-Type Checks (BREAKING API CHANGE)All JSON APIs now check if the request actually has
Content-Type set to application/json.Other Security Changes
AdGuard Home 0.107.13


Release date: September 14, 2022
In this hotfix release with the “lucky” patch number we have fixed a couple of issues that prevented some DHCP clients from receiving their assigned IP addresses. We've also added the new
dns.ipset_file setting, which should help users who maintain large ipsets, for example to use in firewall or VPN settings.Full Changelog
Added
The new optional
dns.ipset_file property, which can be set in the configuration file. It allows loading the ipset list from a file, just like dns.upstream_dns_file does for upstream servers #4686.Changed
The minimum DHCP message size is reassigned back to BOOTP's constraint of 300 bytes #4904.
Fixed
Panic when adding a static lease within the disabled DHCP server #4722.
AdGuard Home 0.107.12


Release date: September 7, 2022
What better way is there to celebrate the coming of autumn than a patch release? In this new version, we have extended and significantly improved AdGuard Home's built-in DHCP server (fixing many bugs in the process) as well as improved our service blocking feature, thanks to many contributions from the community. As always, we have also updated our tooling to make sure that we use the latest versions without any known security issues.
Full Changelog
Security
Go version was updated to prevent the possibility of exploiting the CVE-2022-27664 and CVE-2022-32190 Go vulnerabilities fixed in Go 1.18.6.
Added
New
del DHCP option which removes the corresponding option from server's response #4337. See also a Wiki page.NOTE: This modifier affects all the parameters in the response and not only the requested ones.
A new HTTP API,
GET /control/blocked_services/services, that lists all available blocked services #4535.Changed
The DHCP options handling is now closer to the [RFC 2131][rfc-2131] (#4705).
When the DHCP server is enabled, queries for domain names under
dhcp.local_domain_name not pointing to real DHCP client hostnames are now processed by filters (#4865).The internal DNS client, used to resolve hostnames of external clients and also during automatic updates, now respects the upstream mode settings for the main DNS client #4403.
Deprecated
Ports 784 and 8853 for DNS-over-QUIC in Docker images. Users who still serve DoQ on these ports are encouraged to move to the standard port 853. These ports will be removed from the
EXPOSE section of our Dockerfile in a future release.Go 1.18 support. Future versions will require at least Go 1.19 to build.
Fixed
Dynamic leases created with empty hostnames #4745.
Unnecessary logging of non-critical statistics errors #4850.
AdGuard Home 0.107.11


Release date: August 19, 2022
This hot summer is approaching its end, but hotfixes are still coming in! In this release, we have fixed configuration file migrations not working for people with AdGuard Home versions older than v0.107.7, as well as made a few minor improvements.
--
Full Changelog
--
Added
AdGuard Home 0.107.10


Release date: August 17, 2022
In this new release, we add support for the new Discovery of Designated Resolvers DDR feature, which allows clients using plain DNS to automatically switch to secure protocols. As well as an Arabic localization and fixes for a couple of rather annoying bugs.
Full Changelog
Added
AdGuard Home 0.107.9


Release date: August 3, 2022
Although not a lot of time has passed since the last release, this new one contains a security update, a new feature, a new platform, and some minor fixes :wrench:. It's always nice to have those!
Full Changelog
Security
Go version was updated to prevent the possibility of exploiting the CVE-2022-32189 Go vulnerability fixed in Go 1.18.5. Go 1.17 support has also been removed, as it has reached end of life and will not receive security updates.
Added
Domain-specific upstream servers test. If such test fails, a warning message is shown #4517.
windows/arm64 support #3057.
Changed
UI and update links have been changed to make them more resistant to DNS blocking.
Fixed
Go 1.17 support, as it has reached end of life.
AdGuard Home 0.107.8


Release date: July 19, 2022
Just like a sudden burst of rain during an otherwise hot and sunny summer day, mistakes happen. But unlike rain, we can fix them! Which is exactly what we did in this bugfix release.
Full Changelog
Security
Go version was updated to prevent the possibility of exploiting the CVE-2022-1705, CVE-2022-32148, CVE-2022-30631, and other Go vulnerabilities fixed in Go 1.17.12.
Fixed
DHCP lease validation incorrectly letting users assign the IP address of the gateway as the address of the lease #4698.
Updater no longer expects a hardcoded name for
AdGuardHome executable #4219.Inconsistent names of runtime clients from hosts files #4683.
PTR requests for addresses leased by DHCP will now be resolved into hostnames under
dhcp.local_domain_name#4699.Broken service installation on OpenWrt #4677.
AdGuard Home 0.107.7


Release date: July 19, 2022
The summer is finally here and with it comes a new version of AdGuard Home!
DNS-over-QUIC: RFC 9250
The long-awaited DNS-over-QUIC protocol has finally graduated from a draft to being a real standard, RFC 9250. In this release, we add support for the final version of the standard in a backwards-compatible way.
More Control Over Upstreams
You can now specify an upstream for all subdomains of a domain while excluding the domain itself. For example, if you want queries for
server-1.example.com to be resolved by DNS server 1.1.1.1, but leave example.com to be resolved by your default upstream (in this example, 94.140.14.14), use:94.140.14.14
[/*.example.com/]1.1.1.1Speaking of upstreams. Now you don't have to remember precise IP addresses of plain DNS upstreams. As long as your bootstrap servers can resolve them, you can use the new
udp:// upstream address scheme to resolve upstreams' addresses automatically:udp://one.one.one.one # Same as 1.1.1.1.Other Notable Changes
Users now have more control over how runtime client information is gathered, including the ability to completely disable this feature.
The EDNS Client Subnet information from clients' requests is now shown on the Query log page.
As usual, we strive to keep our tools up-to-date in order to make sure that our users don't fall prey to vulnerabilities.
There are many more smaller changes and fixes; just look at the full changelog below!
Acknowledgements
A special thanks to our open-source contributor, @Lanius-collaris, as well as to everyone who filed and inspected issues, added translations, and helped us test this release!
Full Changelog
Security
Go version was updated to prevent the possibility of exploiting the CVE-2022-29526, CVE-2022-30634, CVE-2022-30629, CVE-2022-30580, and CVE-2022-29804 vulnerabilities.
Enforced password strength policy #3503.
Added
Support upstreams for subdomains of a domain only #4503.
The ability to control each source of runtime clients separately via
clients.runtime_sources configuration object #3020.The ability to customize the set of networks that are considered private through the new
dns.private_networks property in the configuration file #3142.EDNS Client-Subnet information in the request details section of a query log record #3978.
Support for hostnames for plain UDP upstream servers using the
udp:// scheme #4166.Logs are now collected by default on FreeBSD and OpenBSD when AdGuard Home is installed as a service #4213.
Changed
On OpenBSD, the daemon script now uses the recommended
/bin/ksh shell instead of the /bin/sh one #4533. To apply this change, backup your data and run AdGuardHome -s uninstall && AdGuardHome -s install.Reverse DNS now has a greater priority as the source of runtime clients' information than ARP neighborhood.
Improved detection of runtime clients through more resilient ARP processing #3597.
The TTL of responses served from the optimistic cache is now lowered to 10 seconds.
Domain-specific private reverse DNS upstream servers are now validated to allow only
*.in-addr.arpa and *.ip6.arpa domains pointing to locally-served networks #3381. Note: If you already have invalid entries in your configuration, consider removing them manually, since they essentially had no effect.Response filtering is now performed using the record types of the answer section of messages as opposed to the type of the question #4238.
Instead of adding the build time information, the build scripts now use the standardized environment variable [
SOURCE_DATE_EPOCH][repr] to add the date of the commit from which the binary was built #4221. This should simplify reproducible builds for package maintainers and those who compile their own AdGuard Home.The property
local_domain_name is now in the dhcp object in the configuration file to avoid confusion #3367.The
dns.bogus_nxdomain property in the configuration file now supports CIDR notation alongside IP addresses #1730.Configuration Changes
In this release, the schema version has changed from 12 to 14.
Object
clients, which in schema versions 13 and earlier was an array of actual persistent clients, is now consist of persistent and runtime_sources properties:# BEFORE:
'clients':
- name: client-name
# …
# AFTER:
'clients':
'persistent':
- name: client-name
# …
'runtime_sources':
whois: true
arp: true
rdns: true
dhcp: true
hosts: trueThe value for
clients.runtime_sources.rdns field is taken from dns.resolve_clients property. To rollback this change, remove the runtime_sources property, move the contents of persistent into the clients itself, the value of clients.runtime_sources.rdns into the dns.resolve_clients, and change the schema_version back to 13.Property
local_domain_name, which in schema versions 12 and earlier used to be a part of the dns object, is now a part of the dhcp object:# BEFORE:
'dns':
# …
'local_domain_name': 'lan'
# AFTER:
'dhcp':
# …
'local_domain_name': 'lan'To rollback this change, move the property back into the
dns object and change the schema_version back to 12.Deprecated
The
--no-etc-hosts option. Its functionality is now controlled by clients.runtime_sources.hosts configuration property. v0.109.0 will remove the flag completely.Fixed
Query log occasionally going into an infinite loop #4591.
Service startup on boot on systems using SysV-init #4480.
Detection of the stopped service status on macOS and Linux #4273.
Case-sensitive ClientID #4542.
Slow version update queries making other HTTP APIs unresponsive #4499.
ARP tables refreshing process causing excessive PTR requests #3157.
AdGuard Home 0.107.6


Release date: April 14, 2022
This is a small security-oriented update. This AdGuard Home version requires Go v1.17 and later to build, because older Go versions receive no further support, including security patches.
Aside from that, we've slightly updated
$dnsrewrite modifier to support the user-defined Discovery of Designated Resolvers (DDR). We are planning on continuing to make more improvements to it in the future updates, see #4463.The rest are minor changes and ever-present bugfixes.
Full Changelog
Security
User-Agent HTTP header removed from outgoing DNS-over-HTTPS requests.Go version was updated to prevent the possibility of exploiting the CVE-2022-24675, CVE-2022-27536, and CVE-2022-28327 vulnerabilities.
Added
Changed
Filtering rules with the dnsrewrite modifier that create SVCB or HTTPS responses should use ech instead of echconfig to conform with the latest drafts.
Deprecated
SVCB/HTTPS parameter name
echconfig in filtering rules with the dnsrewrite modifier. Use ech instead. v0.109.0 will remove support for the outdated name echconfig.Obsolete --no-mem-optimization option #4437. v0.109.0 will remove the flag completely.
Fixed
I/O timeout errors when checking for the presence of another DHCP server.
Network interfaces being incorrectly labeled as down during installation.
Rules for blocking the QQ service #3717.
Removed
Go 1.16 support, since that branch of the Go compiler has reached end of life and doesn't receive security updates anymore.
AdGuard Home 0.107.5


Release date: April 14, 2022
This is a security release. There are no new changes besides the update of the Go programming language version.
More substantial changes are to come in the subsequent updates.
Full Changelog
Security
Go version was updated to prevent the possibility of exploiting the CVE-2022-24921 vulnerability. As the CVE page is still showing “reserved” at the time of publishing, see also golang/go#51112.
AdGuard Home 0.107.4


Release date: April 14, 2022
A small update to fix a couple bugs and shore up some Go vulnerabilities.
More substantial changes are to come in the subsequent updates.
Full Changelog
Security
Go version was updated to prevent the possibility of exploiting the CVE-2022-23806, CVE-2022-23772, and CVE-2022-23773 vulnerabilities.
Changed
Minor UI improvements.
Fixed
AdGuard Home 0.107.3


Release date: February 3, 2022
This version contains bug fixes and cleanups 🧹. Also, there is a new minor feature: now you can rewrite responses for domains using the response code
NOERROR. Similar rules will allow to get a successful response without records, e.g.:|example.com^$dnsrewrite=NOERRORFull Changelog
Added
AdGuard Home 0.107.2


Release date: January 12, 2022
You know, it is very hard to break your bad habits. We're still struggling with one, the overwhelming need to roll out hotfixes to AdGuard Home releases 😢
Now this one is a hotfix release for a really critical CPU overconsumption bug in v0.107.1.
Please update asap and with this, we wish you happy holidays!🎄
Full Changelog
Fixed
Infinite loops when TCP connections time out (#4042).
AdGuard Home 0.107.1


Release date: January 12, 2022
In a not-futile-at-all-we-swear 😅 attempt to fix all bugs before the New Year we're rolling out a hotfix to the recent v0.107.0. Hopefully, this time we got it all right. And if not, there are still a couple of sheets left on the calendar 📆 and the mug is still half-full with lukewarm coffee ☕
Acknowledgements
A special thanks to our open-source contributors: @Aikatsui and @mdawsonuk, as well as to everyone who filed and inspected issues, added translations, and helped us test this release!
Full Changelog
Changed
The validation error message for duplicated allow- and blocklists in DNS settings now shows the duplicated elements (#3975).
Fixed
ipset initialization bugs (#4027).Legacy DNS rewrites from a wildcard pattern to a subdomain (#4016).
Service not being stopped before running the
uninstall service action (#3868).Broken
reload service action on FreeBSD.Legacy DNS rewrites responding from upstream when a request other than
A or AAAA is received (#4008).Panic on port availability check during installation (#3987).
Incorrect application of rules from the OS's hosts files (#3998).
AdGuard Home 0.107.0


Release date: January 12, 2022
We've had some big AdGuard Home updates in the past, but this one is to top them all. It's been brewing for almost eight months! 🙀 So no wonder there's heaps upon heaps of new features, improvements, bugfixes, and other changes. We'd better start listing them ASAP, or else we'll be risking missing the New Year's fireworks 🎆 🥂
Native Apple Silicon support
There's no shortage of killer features in this changelog, but this one takes the cake as the biggest of them all, without any doubt. You won't have to resort to Rosetta or any such solutions anymore if you want to configure AdGuard Home on a Mac with a Silicon chip.
RFC 9000 support In DNS-over-QUIC
It's not quite over nine thousand, but it'll do. The IETF has formalized QUIC this year with RFC 9000, and DNS-over-QUIC protocol finally supports it. If you haven't tried DoQ yet, consider this a sign.
$dnsrewrite rules and other DNS rewrites will now be applied even when protection is disabled (#1558)
Another popular demand. This change only makes sense, as DNS rewrites often carry a different purpose than simply blocking ads or trackers. You still can disable them by opening the admin panel, going to Settings → General settings, and removing the check mark from the Block domains using filters and hosts files box.
Note: rules contained in system hosts files (e.g.
/etc/hosts) now have higher priority. This may result in more rewrites appearing in your Query log. If some of these rewrites are invalid, remove the corresponding lines from your hosts files or comment them out.DNS-over-HTTPS queries now use the real IP address of the client instead of the address of the proxy (#2799)
Note that this change concerns only those proxies that you've added to the list of "Trusted proxies", otherwise it would be a major security risk. We wouldn't want anything of that sort to happen to you! 🙅♀️ Right now
trusted_proxies can only be configured in AdGuardHome.yaml, but that might change in the future.Optimistic DNS cache (#2145)
To reduce latency you may make AdGuard Home respond from the cache even when the stored entry is expired, while trying to refresh them at the same time🔄 This checkbox is located in Settings → DNS settings → DNS cache configuration and it's not ticked by default. Responses made from DNS cache are marked with a special label in the Query log.
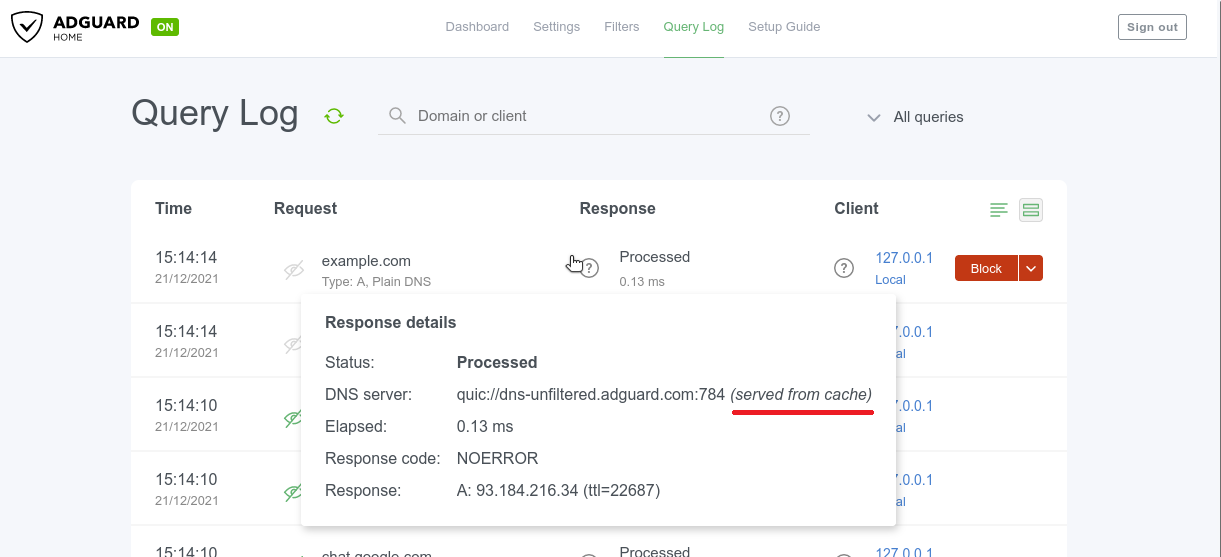
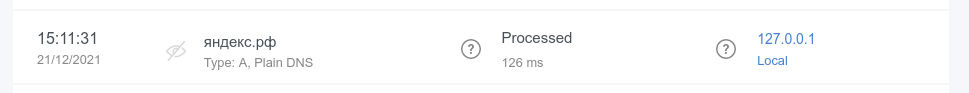
Query log search now supports internationalized domains (#3012)
Internationalized domain names (IDNAs) are domain names that contain symbols in non-Latin script/alphabet, such as
яндекс.рф or ουτοπία.δπθ.gr, for example. Previously, they were being converted to Unicode in AG Home Query log (xn--d1abqjx3f.xn--p1ai and xn--kxae4bafwg.xn--pxaix.gr in our examples), which is a detriment in most cases. Now IDNAs are displayed as is, and you can search for them without resorting to Unicode.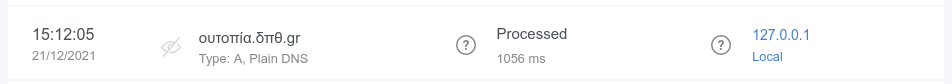
Acknowledgements
A special thanks to our open-source contributors: @Aikatsui, @anbraten, @bruvv, @DandelionSprout, @fvdm, @hnefatl, @markhicken, @p27877, and @systemcrash, as well as to everyone who filed and inspected issues, added translations, and helped us test this release! 🙏
Full Changelog
Added
Upstream server information for responses from cache (#3772). Note that old log entries concerning cached responses won't include that information.
Finnish and Ukrainian translations.
Setting the timeout for IP address pinging in the "Fastest IP address" mode through the new
fastest_timeout field in the configuration file (#1992).Static IP address detection on FreeBSD (#3289).
Optimistic cache (#2145).
New possible value of
6h for querylog_interval setting (#2504).Blocking access using client IDs (#2624, #3162).
source directives support in /etc/network/interfaces on Linux (#3257).RFC 9000 support in DNS-over-QUIC.
Completely disabling statistics by setting the statistics interval to zero (#2141).
The ability to completely purge DHCP leases (#1691).
Settable timeouts for querying the upstream servers (#2280).
Configuration file parameters to change group and user ID on startup on Unix (#2763).
Experimental OpenBSD support for AMD64 and 64-bit ARM CPUs (#2439, #3225, #3226).
Support for custom port in DNS-over-HTTPS profiles for Apple's devices (#3172).
darwin/arm64 support (#2443).freebsd/arm64 support (#2441).Output of the default addresses of the upstreams used for resolving PTRs for private addresses (#3136).
Detection and handling of recurrent PTR requests for locally-served addresses (#3185).
The ability to completely disable reverse DNS resolving of IPs from locally-served networks (#3184).
New flag
--local-frontend to serve dynamically changeable frontend files
from disk as opposed to the ones that were compiled into the binary.Changed
Port bindings are now checked for uniqueness (#3835).
The DNSSEC check now simply checks against the AD flag in the response (#3904).
Client objects in the configuration file are now sorted (#3933).
Responses from cache are now labeled (#3772).
Better error message for ED25519 private keys, which are not widely supported (#3737).
Cache now follows RFC more closely for negative answers (#3707).
$dnsrewrite rules and other DNS rewrites will now be applied even when the protection is disabled (#1558).DHCP gateway address, subnet mask, IP address range, and leases validations (#3529).
The
systemd service script will now create the /var/log directory when it doesn't exist (#3579).Items in allowed clients, disallowed clients, and blocked hosts lists are now required to be unique (#3419).
The TLS private key previously saved as a string isn't shown in API responses anymore (#1898).
Better OpenWrt detection (#3435).
DNS-over-HTTPS queries that come from HTTP proxies in the
trusted_proxies list now use the real IP address of the client instead of the address of the proxy (#2799).Clients who are blocked by access settings now receive a
REFUSED response when a protocol other than DNS-over-UDP and DNSCrypt is used.querylog_interval setting is now formatted in hours.Query log search now supports internationalized domains (#3012).
Internationalized domains are now shown decoded in the query log with the original encoded version shown in request details (#3013).
When /etc/hosts-type rules have several IPs for one host, all IPs are now returned instead of only the first one (#1381).
The setting
rlimit_nofile is now in the os block of the configuration file, together with the new group and user settings (#2763).Permissions on filter files are now
0o644 instead of 0o600 (#3198).Configuration Changes
In this release, the schema version has changed from
10 to 12.Parameter
dns.querylog_interval, which in schema versions 11 and earlier used to be an integer number of days, is now a string with a human-readable duration:# BEFORE:
'dns':
# …
'querylog_interval': 90
# AFTER:
'dns':
# …
'querylog_interval': '2160h'To rollback this change, convert the parameter back into days and change the
schema_version back to 11.Parameter
rlimit_nofile, which in schema versions 10 and earlier used to be on the top level, is now moved to the new os object:# BEFORE:
'rlimit_nofile': 42
# AFTER:
'os':
'group': ''
'rlimit_nofile': 42
'user': ''To rollback this change, move the parameter on the top level and change the
schema_version back to 10.Deprecated
Go 1.16 support. v0.108.0 will require at least Go 1.17 to build.
Fixed
EDNS0 TCP keepalive option handling (#3778).
Rules with the
$denyallow modifier applying to IP addresses when they shouldn't (#3175).The length of the EDNS0 client subnet option appearing too long for some upstream servers (#3887).
Invalid redirection to the HTTPS web interface after saving enabled encryption settings (#3558).
Incomplete propagation of the client's IP anonymization setting to the statistics (#3890).
Incorrect
$dnsrewrite results for entries from the operating system's hosts file (#3815).Matching against rules with
| at the end of the domain name (#3371).Incorrect assignment of explicitly configured DHCP options (#3744).
Occasional panic during shutdown (#3655).
Addition of IPs into only one as opposed to all matching ipsets on Linux (#3638).
Removal of temporary filter files (#3567).
Panic when an upstream server responds with an empty question section (#3551).
9GAG blocking (#3564).
DHCP now follows RFCs more closely when it comes to response sending and option selection (#3443, #3538).
Occasional panics when reading old statistics databases (#3506).
reload service action on macOS and FreeBSD (#3457).Inaccurate using of service actions in the installation script (#3450).
Client ID checking (#3437).
Discovering other DHCP servers on
darwin and freebsd (#3417).Switching listening address to unspecified one when bound to a single specified IPv4 address on Darwin (macOS) (#2807).
Incomplete HTTP response for static IP address.
DNSCrypt queries weren't appearing in query log (#3372).
Wrong IP address for proxied DNS-over-HTTPS queries (#2799).
Domain name letter case mismatches in DNS rewrites (#3351).
Conflicts between IPv4 and IPv6 DNS rewrites (#3343).
Letter case mismatches in
CNAME filtering (#3335).Occasional breakages on network errors with DNS-over-HTTP upstreams (#3217).
Errors when setting static IP on Linux (#3257).
Treatment of domain names and FQDNs in custom rules with
$dnsrewrite that use the PTR type (#3256).Redundant hostname generating while loading static leases with empty hostname (#3166).
Domain name case in responses (#3194).
Custom upstreams selection for clients with client IDs in DNS-over-TLS and DNS-over-HTTP (#3186).
Incorrect client-based filtering applying logic (#2875).
Removed
Go 1.15 support.
AdGuard Home 0.106.3


Release date: May 19, 2021
More! More bugfixes! 🧟♀️
But this time, for a change, there's a couple of new minor features to go with them. Hope you don't mind 🤷♂️
A special thanks to our open-source contributor, @ashishwt, as well as to everyone who filed and inspected issues, added translations, and helped us to test this release!
Added
Changed
Add microseconds to log output.
Fixed
Intermittent "Warning: ID mismatch" errors #3087.
Error when using installation script on some ARMv7 devices #2542.
Local PTR request recursion in Docker containers #3064.
Ignoring client-specific filtering settings when filtering is disabled in general settings #2875.
Disallowed domains are now case-insensitive #3115.
Other minor fixes and improvements.
AdGuard Home 0.106.2


Release date: May 19, 2021
It's not Friday? Not a problem! We defy the tradition of Friday hotfixes by rushing another one out a day earlier 🙌
A special thanks to our open-source contributor, @jankais3r, as well as to everyone who filed issues, added translations, and helped us to test this release!
Fixed
AdGuard Home 0.106.1


Release date: May 19, 2021
We had a release a couple days ago. You all knew it would come to this. 🦸
It's Friday.
It's hotfix time! 🔥
Nothing serious though, we didn't even break anything. Just cleaning up some minor bugs. 🧹
Fixed
AdGuard Home 0.106.0


Release date: May 19, 2021
Quite a lot of changes this time around, even if there aren't as many standouts as in some of the previous updates. We're sure that you'll be able to find a line or two in the changelog that speaks to you!
And one of the reasons for that is the constant support from the community. 👥👥 Special thanks to our open-source contributors: @jvoisin and @Paraphraser, as well as to everyone who filed issues, added translations, and helped us to test this release! 🙇
The ability to set up custom upstreams to resolve PTR queries for local addresses and to disable the automatic resolving of clients' addresses #2704
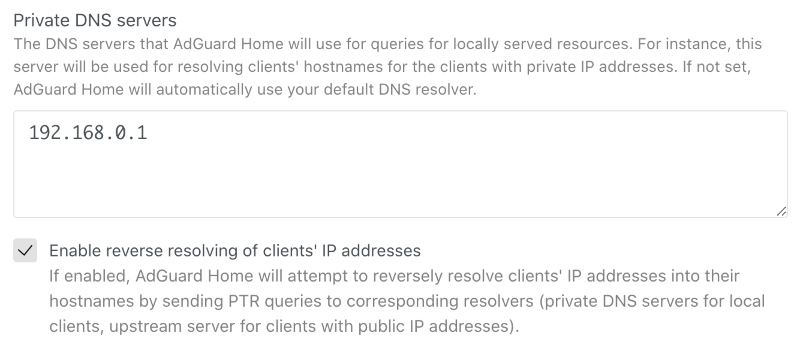
This option will improve your DNS privacy when it comes to addressing local resources. Give it a go unless you want to share your private data with googles of the world.
Search by clients' names in the query log #1273
There's not much that can be said about this feature, it's quite self-explanatory: now you can search up queries by specific clients. 🤷♀️
However, we wanted to highlight it anyway since so many of you have asked for it for quite a while. Hopefully, we delivered! 😅
Added
The ability to block user for login after configurable number of unsuccessful attempts for configurable time #2826.
$denyallow modifier for filters #2923.Hostname uniqueness validation in the DHCP server #2952.
Hostname generating for DHCP clients which don't provide their own #2723.
New flag
--no-etc-hosts to disable client domain name lookups in the operating system's /etc/hosts files #1947.Logging of the client's IP address after failed login attempts #2824.
Verbose version output with
-v --version#2416.The ability to serve DNS queries on multiple hosts and interfaces #1401.
Changed
Quality of logging #2954.
The access to the private hosts is now forbidden for users from external networks #2889.
The reverse lookup for local addresses is now performed via local resolvers #2704.
Stricter validation of the IP addresses of static leases in the DHCP server with regards to the netmask #2838.
Stricter validation of
$dnsrewrite filter modifier parameters #2498.New, more correct versioning scheme #2412.
Deprecated
Go 1.15 support. v0.107.0 will require at least Go 1.16 to build.
Fixed
Multiple answers for
$dnsrewrite rule matching requests with repeating patterns in it #2981.Root server resolving when custom upstreams for hosts are specified #2994.
Inconsistent resolving of DHCP clients when the DHCP server is disabled #2934.
Comment handling in clients' custom upstreams #2947.
Overwriting of DHCPv4 options when using the HTTP API #2927.
Assumption that MAC addresses always have the length of 6 octets #2828.
Support for more than one
/24 subnet in DHCP #2541.Invalid filenames in the
mobileconfig API responses #2835.Removed
Go 1.14 support.
AdGuard Home 0.105.2


Release date: March 15, 2021
There are big flashy updates, and there are seemingly unassuming ones, which constitute, however, the backbone of any successful project. This is the latter, as you may have guessed. You'll find here a heap of bugfixes and a security update for CVE-2021-27935.
Security
Session token doesn't contain user's information anymore (#2470).
Fixed
Incomplete hostnames with trailing zero-bytes handling (#2582).
Wrong DNS-over-TLS ALPN configuration (#2681).
Inconsistent responses for messages with EDNS0 and AD when DNS caching is
enabled (#2600).
Incomplete OpenWrt detection (#2757).
DHCP lease's
expired field incorrect time format (#2692).Incomplete DNS upstreams validation (#2674).
Wrong parsing of DHCP options of the
ip type (#2688).
AdGuard Home v0.105.1


Release date: February 16, 2021
Have you ever thought about why traditions are so important?🧙♂️ Traditions help us remember that we are part of a history that defines our past, shapes who we are today, and who we are likely to become. This is why we at AdGuard respect our traditions, and the most important one is pushing the inevitable hotfix right after every major update.🔥🔧
Jokes aside, here's the list of things fixed and improved in this hotfix.
Changed
"Permission denied" errors when checking if the machine has a static IP no
longer prevent the DHCP server from starting (#2667).
The server name sent by clients of TLS APIs is not only checked when
strict_sni_check is enabled (#2664).Fixed
Error when enabling the DHCP server when AdGuard Home couldn't determine if
the machine has a static IP.
Optical issue on custom rules (#2641).
Occasional crashes during startup.
The field
"range_start" in the GET /control/dhcp/status HTTP API response
is now correctly named again (#2678).DHCPv6 server's
ra_slaac_only and ra_allow_slaac settings aren't reset to
false on update any more (#2653).The
Vary header is now added along with Access-Control-Allow-Origin to
prevent cache-related and other issues in browsers (#2658).The request body size limit is now set for HTTPS requests as well.
Incorrect version tag in the Docker release (#2663).
DNSCrypt queries weren't marked as such in logs (#2662).
AdGuard Home 0.105.0


Release date: February 12, 2021
We took our sweet time with this update, but you'll most certainly find it to be worth the wait. The changelog contains three absolute 💥bangers and a laundry list of lesser changes.
🕵️♂️ Client ID support for DNS-over-HTTPS, DNS-over-QUIC, and DNS-over-TLS #1387
This feature would be really useful to those of you who run an encrypted DNS resolver on a public server. In short, you can now identify your devices not just by their IP address (which is, frankly, not too useful in a public server scenario 🤷♀️), but by using a special "Client ID".

Here's how it works:
First, you add a client and specify an arbitrary string as its "Identifier", for instance,
my-iphone.On the client device you can now configure:
DNS-over-HTTPS: https://example.org/dns-query/my-iphoneQueries and stats are now properly attributed to your device.

🔐 AdGuard as a DNSCrypt-resolver #1361
DNSCrypt was the very first DNS encryption protocol that got some traction. It may not be as popular as DoH/DoT/DoQ now, but it is still viable. Moreover, performance-wise DNSCrypt is better than any of them. And now that v0.105.0 is out, AdGuard Home can be configured to work as a DNSCrypt resolver!
However, here goes the tricky part. We haven't yet exposed these settings to the Web admin panel so if you want to have DNSCrypt, you'll need to follow this instruction and do it via editing the configuration file (
AdGuardHome.yaml). Not that it would scare you off, would it? 🤓
Regarding DNSCrypt clients - AdGuard for Android, Windows and iOS support it, Mac will get its support pretty soon. Besides that, here is a long list of client software that supports it as well.
🆎 $dnsrewrite and $dnstype modifiers #2102#2337
AdGuard Home now supports two more powerful rule modifiers that will help blocklists' maintainers.
$dnstype lets you narrow down the rule scope and apply it only to queries of a specific type(s). For instance, Apple devices now support HTTPS DNS query type. While being generally a good thing, this new type may sometimes be harmful😲. By using $dnstype you can block it completely using a simple rule like this: $dnstype=HTTPS$dnsrewrite is another powerful modifier that allows you to modify DNS responses. Note that this modifier is much more powerful compared to something like a hosts file.Here are some examples:
||example.org^$dnsrewrite=SERVFAIL;; - return SERVFAIL for example.org and all it's subdomains|test.example.org^$dnsrewrite=NOERROR;TXT;hello_world - add a TXT record for test.example.org|example.org^$dnsrewrite=example.com - redirect example.org to example.com|example.org^$dnsrewrite=1.1.1.1 - redirect example.org to example.comYou can find more examples in the documentation.
Added
The host checking API and the query logs API can now return multiple matched rules #2102
Detecting of network interface configured to have static IP address via
/etc/network/interfaces#2302A 5 second wait period until a DHCP server's network interface gets an IP address #2304
HTTP API request body size limit #2305
Changed
Access-Control-Allow-Origin is now only set to the same origin as the domain, but with an HTTP scheme as opposed to *#2484workDir now supports symlinks.Stopped mounting together the directories
/opt/adguardhome/conf and /opt/adguardhome/work in our Docker images #2589When
dns.bogus_nxdomain option is used, the server will now transform responses if there is at least one bogus address instead of all of them #2394. The new behavior is the same as in dnsmasq.Made the mobileconfig HTTP API more robust and predictable, add parameters and improve error response #2358
Improved HTTP requests handling and timeouts #2343
Our snap package now uses the
core20 image as its base #2306Deprecated
Go 1.14 support. v0.106.0 will require at least Go 1.15 to build.
The
darwin/386 port. It will be removed in v0.106.0.The
"rule" and "filter_id" fields in GET /filtering/check_host and
GET /querylog responses. They will be removed in v0.106.0 #2102Fixed
Autoupdate bug in the Darwin (macOS) version #2630
Inability to set DNS cache TTL limits #2459
Possible freezes on slower machines #2225
A mitigation against records being shown in the wrong order on the query log page #2293
A JSON parsing error in query log #2345
Incorrect detection of the IPv6 address of an interface as well as another infinite loop in the
/dhcp/find_active_dhcp HTTP API #2355Removed
The undocumented ability to use hostnames as any of
bind_host values in the configuration. Documentation requires them to be valid IP addresses, and now the implementation makes sure that that is the case #2508Dockerfile#2276. Replaced with the script scripts/make/build-docker.sh which uses scripts/make/Dockerfile.Support for pre-v0.99.3 format of query logs #2102
AdGuard Home 0.104.3


Release date: February 12, 2021
Bugfixes... 😌 There's something about them that we just can't resist. We always want more! 🧟
When there's nothing more to fix, we just roll out a new major update, introduce some fresh bugs and start all over. It's a circle of life ☯️
Luckily, there are still some to prey upon in v0.104. Have a look at what we've fixed this time:
Fixed
Don't expose the profiler HTTP API #2336
Load query logs from files after loading the ones buffered in memory #2325
Don't show Unnecessary errors in logs when switching between query log files #2324
Don't show
404 Not Found errors on the DHCP settings page on Windows. Show that DHCP is not currently available on that OS instead #2295Fix an infinite loop in the
/dhcp/find_active_dhcp HTTP API method #2301Various internal improvements
AdGuard Home 0.104.1


Release date: February 12, 2021
Those who pay close attention to AdGuard Home releases know that we keep hotfixes close to our hearts 🔥♥️ This time we held for as long as we could, but ultimately gave in to the urge 😔
Here's a patch to v0.104 with some fixes and minor improvements.
Fixed
Solve the
permission denied error when launching a DHCP server on Linux using Snap#2228. Users experiencing this issue should refresh their snap and call:
snap connect adguard-home:network-controlThis won't be required in the future versions.
Use matching fonts in the Custom Filters textarea #2254
Show the correct query type for DNS-over-QUIC queries in query log #2241
Increase the default number of simultaneous requests to improve performance #2257
Always set a secondary DNS in DHCP #1708
Improve stability on DNS proxy restart #2242
Improve logging on DNS proxy restart #2252
Don't show a “Loading” message and don't rerequest logs once we've reached the end of logs on the query log page #2229
Various internal improvements.
AdGuard Home 0.104.0


Release date: February 12, 2021
We have something special for y'all today. Not just an implementation of a new feature but the first ever implementation of a new feature! 😮 This is about DNS-over-QUIC, a new DNS encryption protocol — read on to learn more.
Ah, yes, there's also a bunch of other good stuff, too: DHCP-related changes, a .mobileconfig generator for iOS and macOS, and a handful of other enhancements and bugfixes.
DNS-over-QUIC support #2049
AdGuard Home now natively supports a new DNS encryption protocol called DNS-over-QUIC. DoQ standard is currently in the draft state, and AdGuard Home (and dnsproxy) is it's first open-source implementation.🥇

So what's good about it? 🤔 Unlike DoH and DoT, it uses QUIC as a transport protocol and finally brings DNS back to its roots — working over UDP. It brings all the good things that QUIC has to offer — out-of-the-box encryption, reduced connection times, better performance when data packets are lost. Also, QUIC is supposed to be a transport-level protocol and there are no risks of metadata leaks that could happen with DoH. 🔒
At this moment, the only major public DNS resolver that provides DNS-over-QUIC is AdGuard DNS. 😎 Use
quic://dns-unfiltered.adguard.com in the upstreams settings to start using AdGuard DNS "Non-Filtering".DHCP rework: DHCP6 support, custom DHCP options
We did a huge rework of our DHCP server implementation. Thanks to it, AdGuard Home now supports DHCP6 and allows setting custom DHCP options.
Please note that in order to set DHCP options, you'll need to edit the configuration file.
Add support for DHCPv6: #779
DHCPv6 RA+SLAAC: #2076
DHCP: automatic hostnames: #1956
Add DHCP Options: #1585
iOS and MacOS .mobileconfig generator: #2110
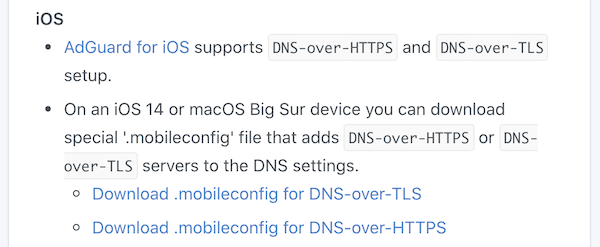
iOS 14 and macOS Big Sur natively support DNS-over-HTTPS and DNS-over-TLS. However, it's not that simple to configure them — you need to install a special "configuration profile" for that. 🤯 In order to make things easier, AdGuard Home can generate these configuration profiles for you. Just head to "Setup Guide" -> "DNS Privacy" and scroll to iOS.
Binary transparency
AdGuard Home binaries are now signed with our GPG key and you can now easily verify that they really come from us: https://github.com/AdguardTeam/AdGuardHome/wiki/Verify-Releases
Other improvements
Allow entering comments to the Upstreams box: #2083
Load upstreams list from a file: #1680
Add ARMv8 to future releases, potentially append a v8 binary to the most recent non-beta release: #2125
Redesign query logs block/unblock buttons: #2050
Treat entries starting with "/" as "://" under specific circumstances: #1950
Use "Null IP" instead of NXDOMAIN by default: #1914
Bootstrap with TCP upstreams: #1843
Add block and unblock buttons to 'check the filtering' result: #1734
ipset feature support: #1191
Add Belarusian and Chinese Traditional HK languages: #2106
Add new language: en-silk: #1796
Use DOH or DOT as bootstrap: #960
Fixed
Reverse lookups return empty answers for hosts from /etc/hosts: #2085
Static lease hostnames are overridden by client-identifier: #2040
Query log doesn't display name for blocked services: #2038
Custom filter editor works with delay: #1657
Incorrect link address: #2209
Smartphone compatible design for user interface: #2152
Misleading information during service installation: #2128
Remove the limit on cache-min-ttl, 3600: #2094
Cannot change minimum TTL override in UI: #2091
Optical Issue on mobile phone: #2090
Setting a large DNS Cache Size in the Web GUI will exceed the unit32 range.: #2056
Clients requests aren't counted properly: #2037
Publish privacy policy on front page (README.md): #1960
Sorting various IP Address Columns in the UI (eg in dhcp static leases) does not sort correctly. They are treated as strings instead of numeric.: #1877
Requests count for clients with CIDR IP addresses: #1824



