Cookies, Google, Amazon, Twitter breach & warrantless surveillance. AdGuard’s digest
In this edition of AdGuard's Digest: Chrome can’t say goodbye to third-party cookies, Twitter suffers a breach, European countries deem Google not safe for schools, smart doorbells share data with police (no warrant needed), the UK wants tech companies to scan phones, while the US stockpiles cell phone location data.
Leading network operators test new cookie-free way to track users
Europe’s leading telecommunications providers, Vodafone and Deutsche Telekom, have been testing a new tracking tool that can potentially replace third-party cookies. While the old tracking method relies on storing website imprints on the device, a new tool called TrustPid allows service providers to store all the data. With TrustPid, carriers assign “pseudo-anonymous tokens” to users based on their IP addresses. If website operators, starved of user data due to the phasing out of third-party cookies, want to know more about visitors, they can call up this identifier and personalize ads. While websites might not be able to identify individual users, network operators could easily do it.
TrustPid claims that the mechanism is “privacy-friendly”, but it is already being compared to a controversial tracking code known as “supercookie”. Unlike a regular cookie, which can be cleared and blocked, a “supercookie” can’t since it is not stored on the device. Verizon was fined in the US back in 2016 for planting “supercookies” into users’ browser requests without consent. Vodafone says TrustPid is not a “supercookie” and is GDPR-compliant.
This is another one of those cases where tech companies are trying to circumvent tracking restrictions under the guise of protecting privacy. With the imminent demise of third-party cookies, companies are trying to make up for lost advertising revenue by coming up with new ways to collect user data. We see companies vying to be the first to adopt new tracking technologies, thereby grabbing a slice of the ad market. The irony is that they portray their pursuit of ad money as something that will benefit users.
Denmark and the Netherlands limit use of Google services in schools
With the new school year inching closer, Denmark has declared open season on Google. The Danish data protection agency has banned the use of Chromebooks and Google Workspace for processing personal data in schools. The ban directly applies to one municipality, but others are advised to follow suit. The agency ruled that the way the tech giant processes personal data is incompatible with the European data protection law (GDPR). It took a particular issue with the fact that Google can transfer data to third countries such as the US “without the necessary level of security.” Google Workplace for Education includes such go-to ed-tech tools as Google Classroom, Google Docs, Google Slides, Gmail, Google Meet and Google Drive.
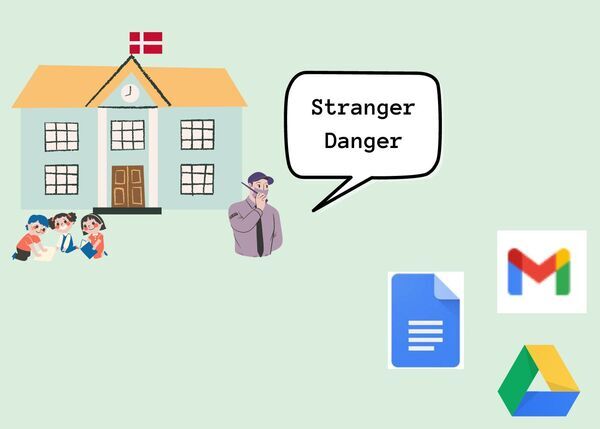
Meanwhile, the Dutch Ministry of Education urged schools to take extra steps to secure data when using Google’s Chrome web browser and Chrome OS. In its current state, the two services are not GDPR-compliant and are expected to become so no sooner than August 2023 when Google is set to release their updated versions. For now, schools that want to keep on using Chrome must abide by the rules that are sure to inconvenience some learners. For instance, schools will need to disable automatic translation for websites, turn off spell checks, switch off ad personalization and make sure the data is stored in Europe. Schools are also encouraged to ditch Google’s search engine, and opt for more privacy-friendly options such as DuckDuckGo.
If Google’s data-sharing practices have become a source of concern for the governments, then it’s high time you started having concerns yourself (if you haven't already).
5.4 million Twitter account details up for sale
It looks like Twitter can’t catch a break. In addition to its looming legal battle with Elon Musk over an ill-fated buyout deal, the social media giant has been dealt another blow. A database containing phone numbers and email addresses for 5.4 million Twitter accounts has been put up for sale for $30.000. The data was allegedly scraped in December 2021 and was obtained through a vulnerability that has since been patched. The trove contains public Twitter profile information (a nickname and profile description) complete with a phone number and/or an email address.
The breach poses a major threat to Twitter users, especially to public figures — it looks like we may see more social media crypto scams involving celebrities in the future. Moreover, by matching the user's email to known databases, attackers can try to dig up dirt on politicians, activists, celebrities and out/blackmail them. Particularly vulnerable are people who use the same email to register on many websites, including those with questionable or prohibited content, such as porn sites or illegal marketplaces. In general, it’s better to use a dedicated email for social media to avoid having your data compromised in breaches like this.
It may seem as though big companies with elaborate security infrastructure (like Twitter) are immune from bugs and leaks, but that’s a false impression — keep that in mind when allowing them access your data.
Lingering farewell: Chrome delays phasing out third-party cookies yet again
Saying goodbye to third-party cookies seems to be too painful for Google. The tech giant has announced that it would delay the depreciation of the tracking mechanism in its Chrome browser, this time till the second half of 2024.
While Safari and Firefox have been blocking third-party cookies by default, Google originally planned to end support for third-party cookies by 2022 as part of the Privacy Sandbox initiative. That deadline was first pushed back to 2023 and now to 2024.

Earlier this year Google released its Privacy Sandbox initiative, whose stated goal was to reconcile the interests of privacy-conscious users with that of advertisers. It was meant to do so by replacing third-party cookies with the mechanism called Topics. Billed as a privacy-friendly alternative to tracking, Topics, sadly, will only cement Google’s ad monopoly, allowing big tech to still identify individual users. You can read our in-depth review of Topics and the Privacy Sandbox as a whole.
It’s an emergency! Google & Amazon let police access doorbell and cam data
Google-owned Nest and Amazon-owned Ring, which both sell smart video doorbells and home security cameras, have confirmed that they can give police access to private videodata without user consent or warrant in case of an “emergency”. Ring has revealed that it has granted 11 such requests so far this year, some of them pertaining to kidnapping, self-harm and attempted murder. Nest said that it reserves the right to grant such requests but has not done so yet.
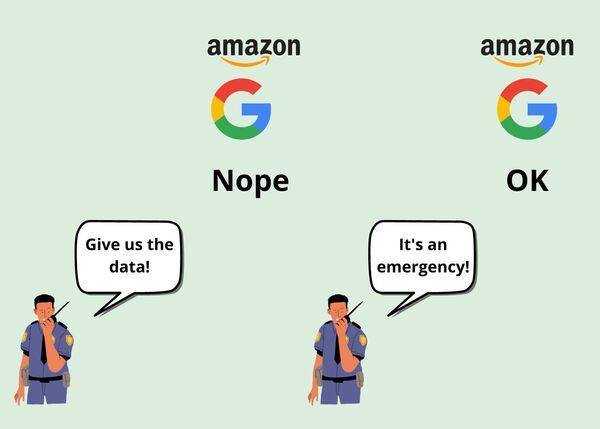
It’s unclear if Ring notifies customers after the company had provided user data to law enforcement. Nest said that it would typically notify users of emergency requests unless prohibited by law.
The US law allows companies that process video footage to comply with warrantless requests, but they are not legally obligated to do so. The practice is alarming since it is vulnerable to police overreach and abuse. Without legal oversight, companies are given an exclusive right to decide whether a given incident is an emergency, and users should think twice before entrusting their data to such companies.
Backdoors built into smart home systems allow tech companies to access user data at will. Yet we, users, are the ones who have to pay for this functionality, although we do not necessarily need it. Effectively, users are left with no choice but to finance big tech’s snooping out of their own pocket. The only alternative is not to buy these products.
UK pushes for tech giants to scan phones for child sex abuse
Cybersecurity chiefs in the UK have called for tech companies to build software for scanning phones client-side. The idea is in line with the proposed UK online safety bill. If adopted, it could force online platforms to scan user content for child sexual materials and terrorism.
The idea resembles Apple’s bid to introduce CSAM's detection feature last year. Apple faced backlash from privacy advocates, arguing it would jeopardize end-to-end encryption and eventually put off the launch of the feature. Earlier this year, the European Commission proposed a law that would require tech companies to scan messages for CSAM materials and detect “grooming” in messages.
The UK may want to walk the tightrope between privacy and child protection, but once end-to-end encryption is undermined, there is no going back. We are a firsthand witness to a disturbing trend: first in the EU and now in the UK, privacy is being eroded under the pretext of protecting children. The effectiveness of the measure is questionable, while the damage to user privacy will be irreparable and long-lasting.
Just Buy It: Data brokers sell location information to US government
Documents obtained by the American Civil Liberties Union (ACLU) showed that the US government has been buying phone location data in bulk from two brokers, eluding any judicial oversight. US agencies that deal with immigration and border security bought copious amounts of data from Venntel and Babel Street from 2017 to 2019. In one instance, the US Customs and Border Protection (CBP) obtained as many as 133,654 location points from cellphones in the span of 3 days.

The ACLU sees the practice as unwarranted tracking that relies on the data “quietly extracted from smartphone apps.”
App developers may embed third-party software development kits (SDKs) into their apps so that they can track user location. Thus, developers save money and time needed to come up with their own solutions. However, some SDKs can transfer user data to third parties and sell it. Earlier we wrote about a SDK vendor called SafeGraph, which was selling location data on abortion clincs’ clients. One way to protect your privacy is to give apps only the necessary permissions. And if you have to permit your app to identify your location (for example, if it’s a weather app), then you might want to check if it does not relay your location data elsewhere.

















































